Configuring SAML2 login contains the following steps:
NOTE: Authentication configuration is shared between the SPS central configuration and the managed hosts, therefore you must configure the Service Provider (SP) settings and the SAML2 login methods on the central configuration node.
Navigate to Users & Access Control > Login options. The SSO Configuration menu contains information about your SP configuration.
To configure SPS as a SAML2 Service Provider (SP), complete the following steps.
-
Navigate to Users & Access Control > Login options, and click SSO Configuration.
The SSO Configuration menu contains information about your SP configuration.
-
Click SAML2 Service Provider settings from the drop down menu.
-
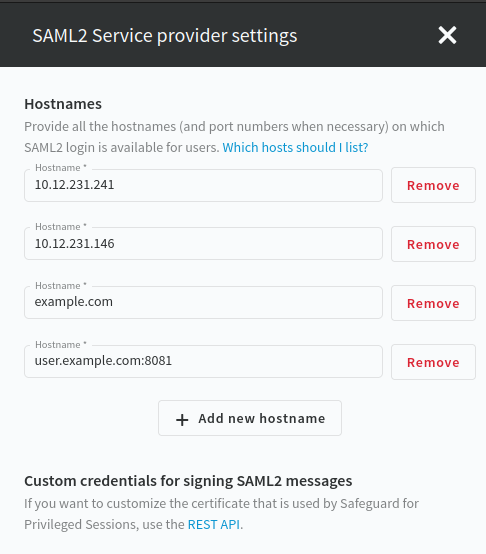
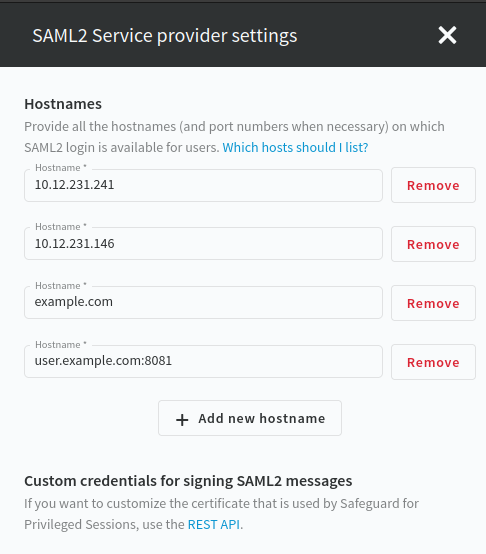
Click Add new hostname to provide all the host names on which the SAML2 login method is available for users. When necessary, provide the port number as well. For example, 10.12.231.241, example.com, or user.example.com:8081.
The web user interface allows you to configure the Assertion Consumer Service URLs. You can configure the entityID and the custom credentials on the REST API, if the defaults are not suitable.
Figure 91: Users & Access Control > Login Options > SSO Configuration > SAML2 Service Provider settings – Configuring SP entity ID and host names
-
Click Save.
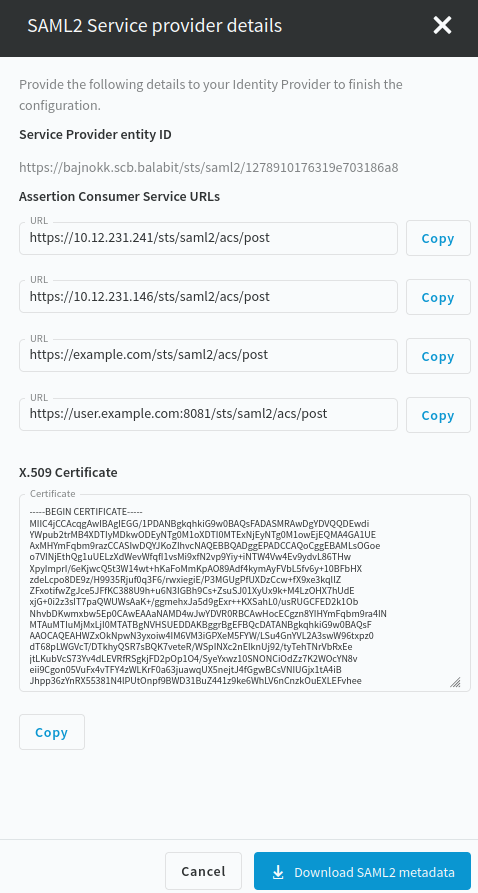
To configure your Identity Provider (IdP) to trust One Identity Safeguard for Privileged Sessions (SPS) as a Service Provider (SP), you must provide the SP metadata XML file of your SPS to your IdP. If your IdP supports the import of SP metadata, then you can choose either of the following methods to download the SP metadata XML file:
-
Download the SP metadata XML file by clicking Users & Access Control > Login Options > SSO Configuration > SAML2 Service Provider details > Download SAML2 metadata on the SPS web interface.
-
Download the SP metadata XML file from your SPS at the following location:
https://<ADDRESS-OF-YOUR-SPS>/sts/saml2/sp-metadata.xml
This file is accessible also for unauthenticated users since it only contains public information about the SAML2 SP configuration.
If your IdP does not support the import of SP metadata, then you must configure your IdP based on the summary of the SAML2 Service Provider details page.
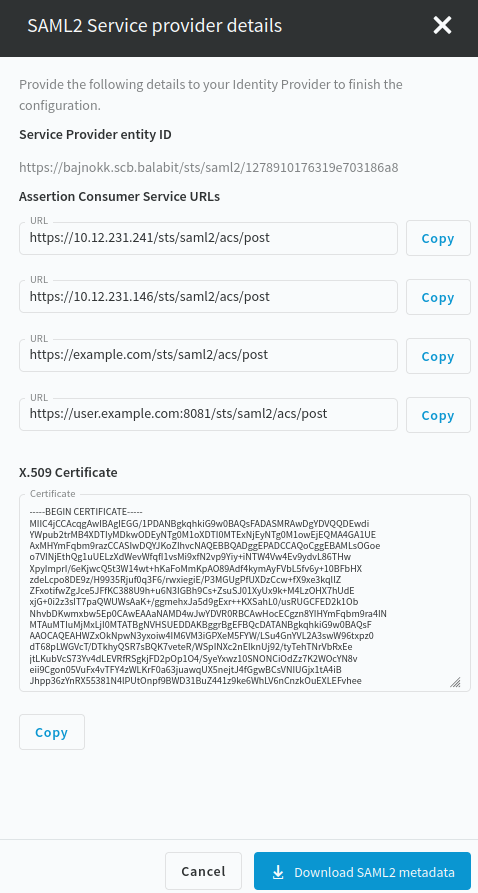
Figure 92: Users & Access Control > Login Options > SSO Configuration > SAML2 Service Provider details
To authenticate SPS users with a SAML2 login method, complete the following steps.
-
Navigate to Users & Access Control > Login Options.
-
To configure a SAML2 login method, select one of the following options:
-
Select an existing SAML2 login option and click Edit.
-
Click Create new login method and select SAML2.
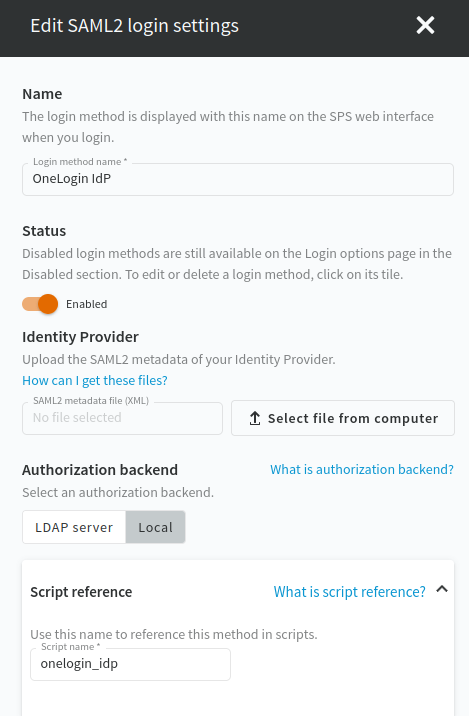
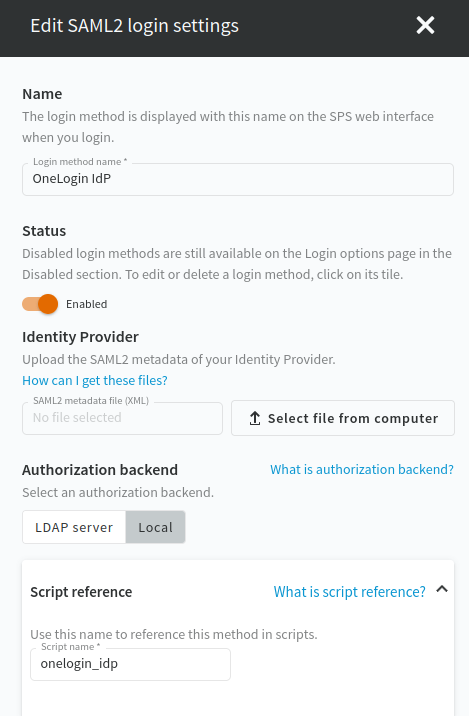
The following figure shows the configuration options of the SAML2 login method.
Figure 93: Users & Access Control > Login options — Configuring SAML2 authentication
-
In the Name field, specify a name for the login option.
-
Upload the SAML2 metadata XML of your Identity Provider.
NOTE: Your IdP metadata file should contain a single SAML2 IdP metadata entity. To support SAML2 login with multiple IdPs, you have to configure additional SAML2 login methods.
-
Select LDAP server or Local as the Authorization backend.
-
(Optional) To add a new LDAP server, click Add new LDAP server under Authorization backend and select one of the server types:
-
Script reference is filled out automatically when you specify the name for the login option. Special characters are automatically replaced with dashes ("-"). The Script name is a unique, human readable ID that is used by the REST API clients to select the login method.
-
To save your modifications, click Commit.