Policies in this category are intended to automate the removal of deprovisioned user accounts from groups. A policy can be configured to remove user accounts from all groups with optional exceptions. Individual policy rules can be applied to security groups and to mail-enabled groups of both the security and distribution type.
Group Membership Removal
How this policy works
When processing a request to deprovision a user, Active Roles uses this policy to determine what changes are to be made to group memberships of the user’s account. By removing the account from security groups, the policy revokes user access to resources. By removing the account from mail-enabled groups, the policy prevents erroneous situations where e-mail is sent to the deprovisioned mailbox.
|
|
IMPORTANT: The deprovisioned users are automatically removed from all Dynamic Groups, regardless of the Group Membership Removal policy settings. |
A Group Membership Removal policy includes separate rules for security groups and for mail-enabled groups. For each category of groups, a rule can instruct Active Roles to perform one of the actions that are summarized in the following table.
|
Category |
Action |
Result |
|
Security groups |
Do not remove from groups. |
The deprovisioned user remains in all security groups it was a member of as of the time of deprovisioning, except for the Dynamic Groups. |
|
|
Remove from all groups. |
The deprovisioned user is removed from all security groups. |
|
|
Remove from all groups except for the specified ones. |
The deprovisioned user is not removed from the specified security groups, with the exception of Dynamic Groups. The user is removed from all the other security groups. |
|
Mail-enabled groups |
Do not remove from groups. |
The deprovisioned user is not removed from distribution groups or mail-enabled security groups, except for the Dynamic Groups. |
|
|
Remove from all groups. |
The deprovisioned user is removed from all distribution groups and from all mail-enabled security groups. |
|
|
Remove from all groups except for the specified ones. |
The deprovisioned user is not removed from the specified distribution or mail-enabled security groups, with the exception of Dynamic Groups. The user is removed from all the other distribution and mail-enabled security groups. |
In the event of a conflict in policy implementation, the remove action takes precedence. For example, with a rule configured to remove the user account from all security groups, the user account is removed from all security groups even if there is another rule according to which Active Roles does not remove the user account from mail-enabled security groups.
Another conflict may occur in the situation where a policy of this category attempts to remove a deprovisioned user from a group that is configured as Active Roles’ Dynamic Group (see the Dynamic Groups chapter, later in this document). The Dynamic Group policy detects the removal, and might add the deprovisioned user back to the Dynamic Group. To avoid such a situation, Active Roles does not allow Dynamic Groups to hold deprovisioned users. Once a user is deprovisioned, the user’s account is removed from all Dynamic Groups.
How to configure a Group Membership Removal policy
To configure a Group Membership Removal policy, select Group Membership Removal on the Policy to Configure page in the New Deprovisioning Policy Object wizard or in the Add Deprovisioning Policy wizard. Then, click Next to display the Removal from Security Groups page.
Figure 76: Removal from Security Groups

On this page, you can configure a rule on how to remove a deprovisioned user from security groups.
Select one of these options:
- Click Do not remove from security groups for the policy not to make changes to security group memberships of the user account.
- Click Remove from all security groups, with optional exceptions for the policy to remove the user account from all security groups.
With the second option, you can specify whether you want the policy not to remove the user account from certain security groups. To set up a list of such groups, select the Keep the user account in these security groups check box, and then click the Add button and select the groups you want to include in the list.
When you are done configuring the rule for security groups, click Next to display the Removal from Mail-enabled Groups page.
Figure 77: Removal from Mail-enabled Groups
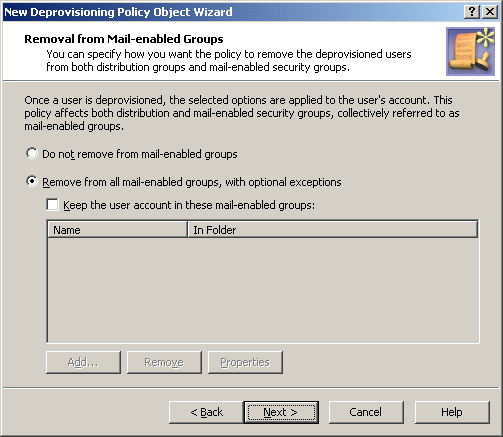
This page is similar to the previous one. It allows you to configure a rule on how to remove a user account from both distribution groups and mail-enabled security groups, which are collectively referred to as mail-enabled groups.
Select one of these options:
- Click Do not remove from mail-enabled groups for the policy not to make changes to mail-enabled group memberships of the user account.
- Click Remove from all mail-enabled groups, with optional exceptions for the policy to remove the user account from all mail-enabled groups.
With the second option, you can specify whether you want the policy not to remove the user account from certain mail-enabled groups. To set up a list of such groups, select the Keep the user account in these mail-enabled groups check box, and then click the Add button and select the groups you want to include in the list.
When you are done configuring the rule for mail-enabled groups, click Next and follow the instructions in the wizard to create the Policy Object.
Steps for configuring a Group Membership Removal policy
To configure a Group Membership Removal policy
- On the Policy to Configure page, select Group Membership Removal, and then click Next.
- On the Removal from Security Groups page, do one of the following:
- If you selected the second option in Step 2, specify whether you want the policy not to remove the user account from certain security groups. Do one of the following:
- Click Next.
- On the Removal from Mail-enabled Groups page, do one of the following:
- Click Do not remove from mail-enabled groups for the policy not to make changes to mail-enabled group memberships of the user account.
- Click Remove from all mail-enabled groups, with optional exceptions for the policy to remove the user account from all mail-enabled groups.
- If you selected the second option in Step 5, specify whether you want the policy not to remove the user account from certain mail-enabled groups. Do one of the following:
- Select the Keep the user account in these mail-enabled groups check box and set up the list of mail-enabled groups from which you want the policy not to remove the user account.
- If you want the policy to remove the user account from all mail-enabled groups, leave the check box cleared.
- Click Next.
- On the Enforce Policy page, you can specify objects to which this Policy Object is to be applied:
- Click Next, and then click Finish.

