Step 1: Creating and configuring the Policy Object
You can create and configure the Policy Object you need by using the New Provisioning Policy Object wizard. For information about the wizard, see Creating a Policy Object in the Policy Object management tasks section earlier in this chapter.
To configure the policy, click Property Generation and Validation on the Policy to Configure page of the wizard. Then, click Next.
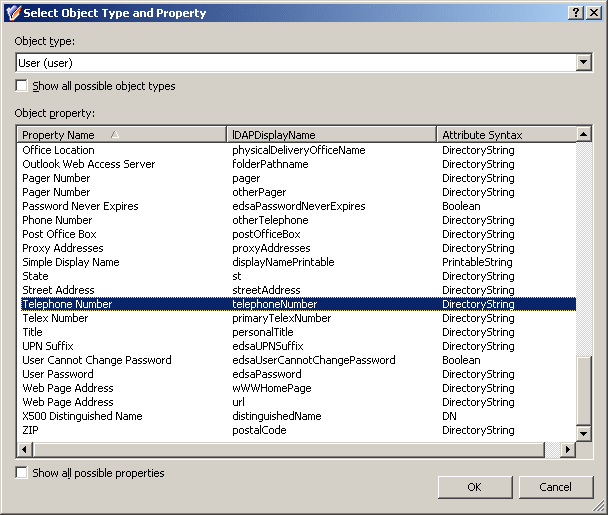
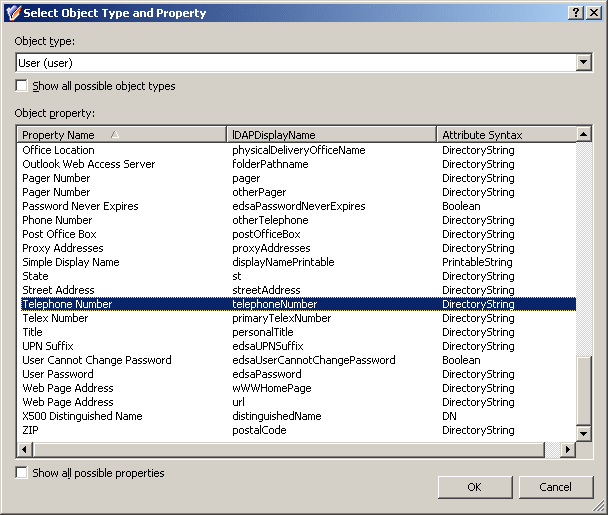
On the Controlled Property page, click Select. Then, in the Select Object Type and Property dialog box, select User from the Object type list, and click Telephone number in the Object property list, as shown in the following figure.
Figure 53: Select Object type and property
Click OK, and then click Next.
On the Configure Policy Rule page, in the upper box, select the following check boxes:
- ‘Telephone Number’ must be specified. This makes the phone number a required property, that is, requires that a phone number be specified in every user account.
- ‘Telephone Number’ must be <value>. This allows you configure a mask for the telephone number by adding the appropriate entry to the value for this condition.
At this stage, the Configure Policy Rules page looks like the following figure.
Figure 54: Configure policy rules

The next phase is to configure the value.
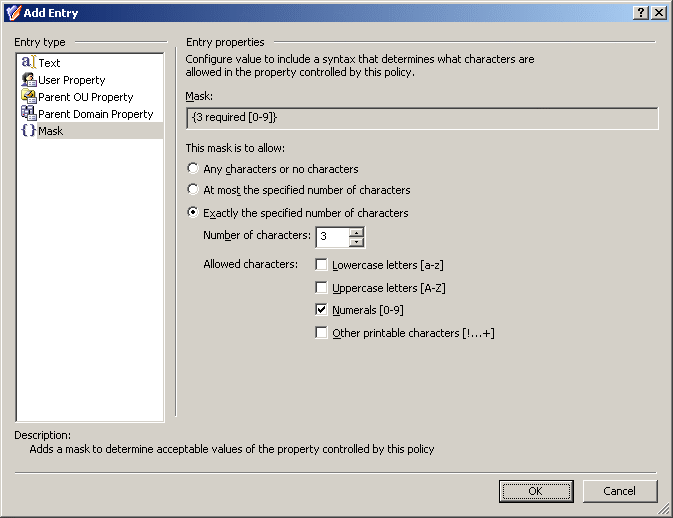
Click the link labeled <click to add value>. In the Add Value dialog box, click Configure. In the Configure Value dialog box, click Add. In the Add Entry window, under Entry type, click Mask.
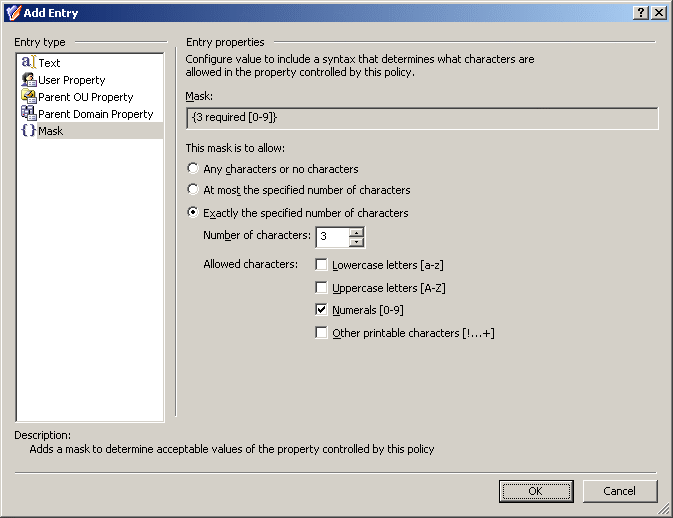
Now you can use the Entry properties area in the Add Entry window to configure a mask.
The format consists of four groups of numerals divided by certain characters—space character, hyphens, and brackets. First, configure a mask that requires the first three characters to be numerals:
- Select Exactly the specified number of characters.
- In the Number of characters box, enter 3.
- Under Allowed characters, select the Numerals check box.
The Add Entry window should look as shown in the following figure.
Figure 55: Add entry
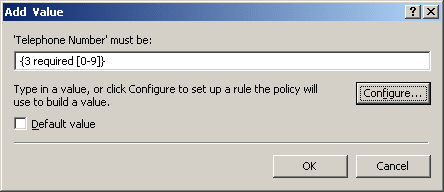
Click OK to close the Add Entry window. Then, click OK to close the Configure Value dialog box. As a result, the Add Value dialog box looks as shown in the following figure.
Figure 56: Add value dialog box
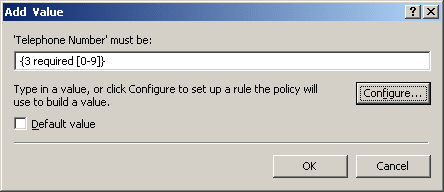
Taking into consideration the mask you have configured, you can guess that the mask for the phone number format you need is as follows:
({3 required [0-9]}) {3 required [0-9]}-{2 required [0-9]}-{2 required [0-9]}
Type this mask in the ‘Telephone Number’ must be box in the Add Value dialog box. Pay attention to the round brackets enclosing the first three characters, a space character following the group in the round brackets, and two hyphen characters that separate the groups of characters.
Click OK to close the Add Value dialog box. Click Next and follow the instructions in the wizard to create the Policy Object.
Step 2: Applying the Policy Object
You can apply the Policy Object by using the Enforce Policy page in the New Provisioning Policy Object wizard, or you can complete the wizard and then use the Enforce Policy command on the domain, OU, or Managed Unit where you want to apply the policy.
For more information on how to apply a Policy Object, see Applying Policy Objects and Managing policy scope earlier in this chapter.
This scenario describes how to configure a policy that forces the user phone number to conform to the following format:
- Use spaces (instead of dashes or braces) to separate area code.
- Use spaces (instead of dashes) to separate the phone number.
- Optionally, use a lowercase “x” to indicate an extension.
The following table provides some examples to clarify how the phone number should look in accordance with these formatting requirements.
Table 17: Phone number format
|
+1 949 754 8515 |
949-754-8515 |
The incorrect entry does not begin with + and country code, and uses dashes instead of space. |
|
+44 1628 606699 x1199 |
+44 1628 606699 X1199 |
The incorrect entry uses the upper-case X. |
To implement this scenario, you must perform the following actions:
- Configure the Policy Object that defines the appropriate policy.
- Apply the Policy Object to a domain, OU, or Managed Unit.
As a result, when creating or modifying a user object in the container you selected in Step 2, Active Roles checks whether the phone number conforms to the stated format. If not, the policy disallows the creation or modification of the user object.
Step 1: Configuring the Policy Object
You can configure the Policy Object you need by modifying the Policy Object that implements the previous scenario, see Scenario 1: Using mask to control phone number format earlier in this section.
Display the Properties dialog box for that Policy Object and go to the Policies tab. Then, select the policy from the list, and click View/Edit to display the Property Generation and Validation Policy Properties dialog box.
The Policy Rule tab in the Property Generation and Validation Policy Properties dialog box looks similar to the Configure Policy Rule page in the wizard you used to configure the policy. You can use that tab to modify the policy rules.
First, modify the rule to remove the mask entry. On the Policy Rule tab, in the upper box, clear the ‘Telephone Number’ must be <value> check box.
Next, choose to configure a rule based on regular expressions. On the Policy Rule tab, in the upper box, select the ‘Telephone Number’ must match regular expression <value> check box. To access this check box, you need to scroll down the list of check boxes.
Finally, specify the regular expressions that define the policy in question. The regular expressions you need are as follows:
^\+([0-9]+ )+[0-9]+$
^\+([0-9]+ )+x[0-9]+$
The following table briefly describes the elements that are used in the two above syntax. For more information about regular expressions, see Appendix A: Using regular expressions later in this document.
Table 18: Regular expressions
|
^ |
The beginning of the input string to validate |
|
\+ |
The escape sequence to represent the plus character (+) |
|
([0-9]+ )+ |
Concatenation of one or more substrings, with each substring consisting of one or more digit characters followed by a space character |
|
[0-9]+ |
One or more digit characters. |
|
x[0-9]+ |
A lowercase "x" followed by one or more digit characters |
|
$ |
The end of the input string to validate |
Thus, the policy must be configured to only allow the telephone numbers that match ^\+([0-9]+ )+[0-9]+$ (telephone numbers without extensions) or ^\+([0-9]+ )+x[0-9]+$ (telephone numbers that include extensions). Proceed with configuring the policy as follows:
- On the Policy Rule tab, in the lower box, click the link labeled <click to add value>.
- In the Add Value dialog box, enter ^\+([0-9]+ )+[0-9]+$, and click OK.
- On the Policy Rule tab, in the lower box, click the link labeled <click to add value>.
- In the Add Value dialog box, enter ^\+([0-9]+ )+x[0-9]+$, and click OK.
- Click OK to close the Property Generation and Validation Policy Properties dialog box.