Managing SharePoint environments
In One Identity Manager, components and access rights from SharePoint 2013, SharePoint 2016, SharePoint 2019, and the SharePoint Server Subscription Edition can be mapped. The aim of this is to guarantee company employees access to the SharePoint site. To achieve this, information about the following SharePoint components is loaded into the One Identity Manager database.
SharePoint roles, groups, and user accounts are mapped in the context of the SharePoint components for which they are set up. In the One Identity Manager, these objects provide SharePoint users with access permissions to the different websites. For that, you can use the different One Identity Manager mechanisms for linking identities with their SharePoint user accounts. The following objects are provisioned:
- SharePoint user accounts and their relations to SharePoint roles and groups
- SharePoint groups and their assignments to user accounts and roles
- SharePoint roles and their site permissions
To log into the SharePoint server, One Identity Manager supports classic Windows authentication as well as claims-based authentication. Every SharePoint user account that can log in with classic Windows authentication, is assigned either an Active Directory or an LDAP user account or an Active Directory or LDAP group in One Identity Manager. Login requires that the associated Active Directory or LDAP systems are also mapped in the One Identity Manager database. You can maintain information in One Identity Manager about authentication systems used by the SharePoint environment.
For every SharePoint user account linked to an Active Directory or LDAP user account, an additional identity defined in the One Identity Manager database can also can be assigned. This makes it possible to maintain identity memberships in SharePoint roles and groups. Identities can inherit SharePoint permissions by assigning SharePoint roles and groups to the organizational units. It is also possible to request permissions through the IT Shop. Permissions assigned to an identity can be monitored over compliance rules.
Architecture overview
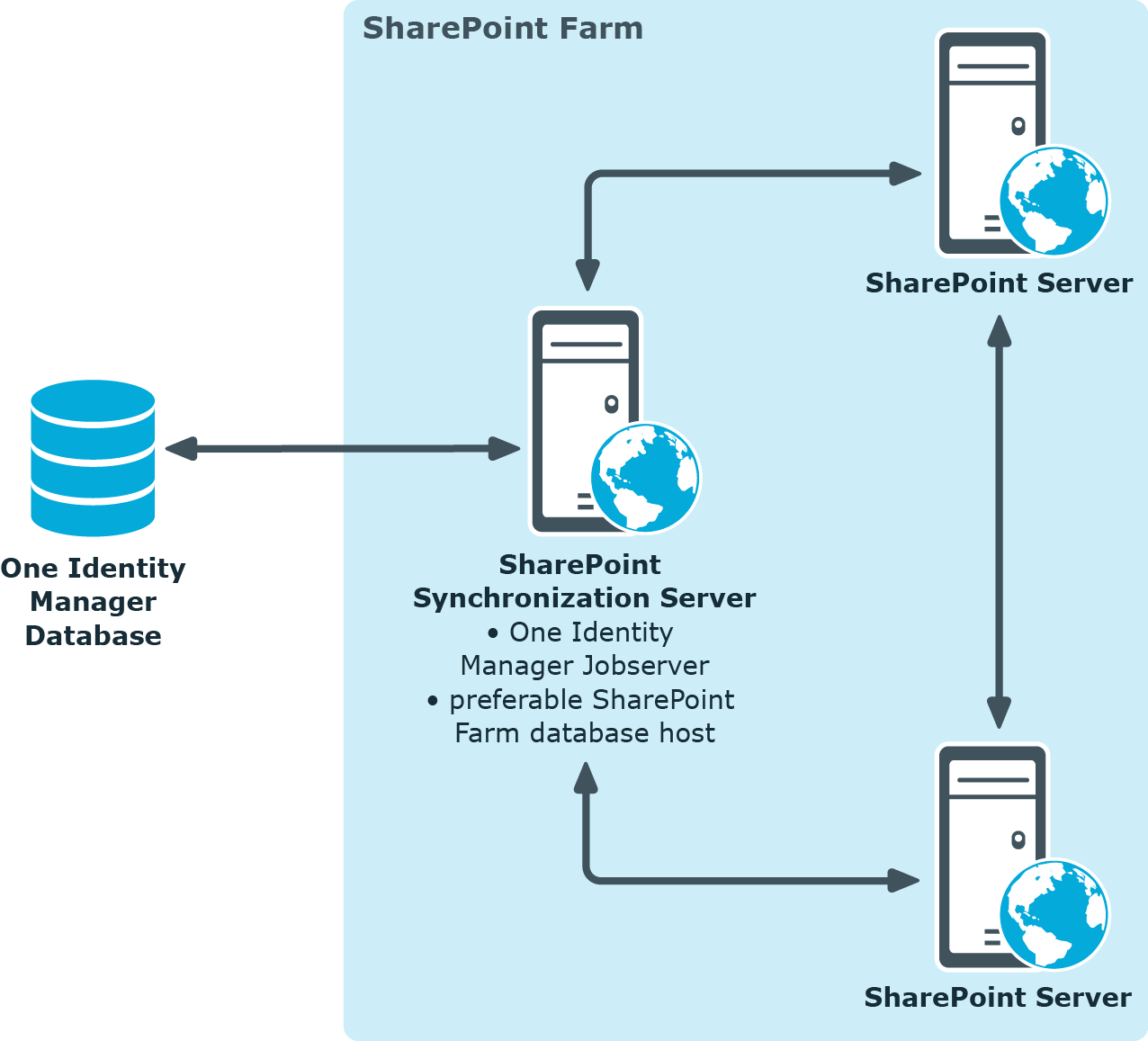
The SharePoint connector is used for synchronization and provisioning SharePoint. The connector communicates directly with a SharePoint farm's SharePoint servers.
Figure 1: Connector paths for communicating with SharePoint
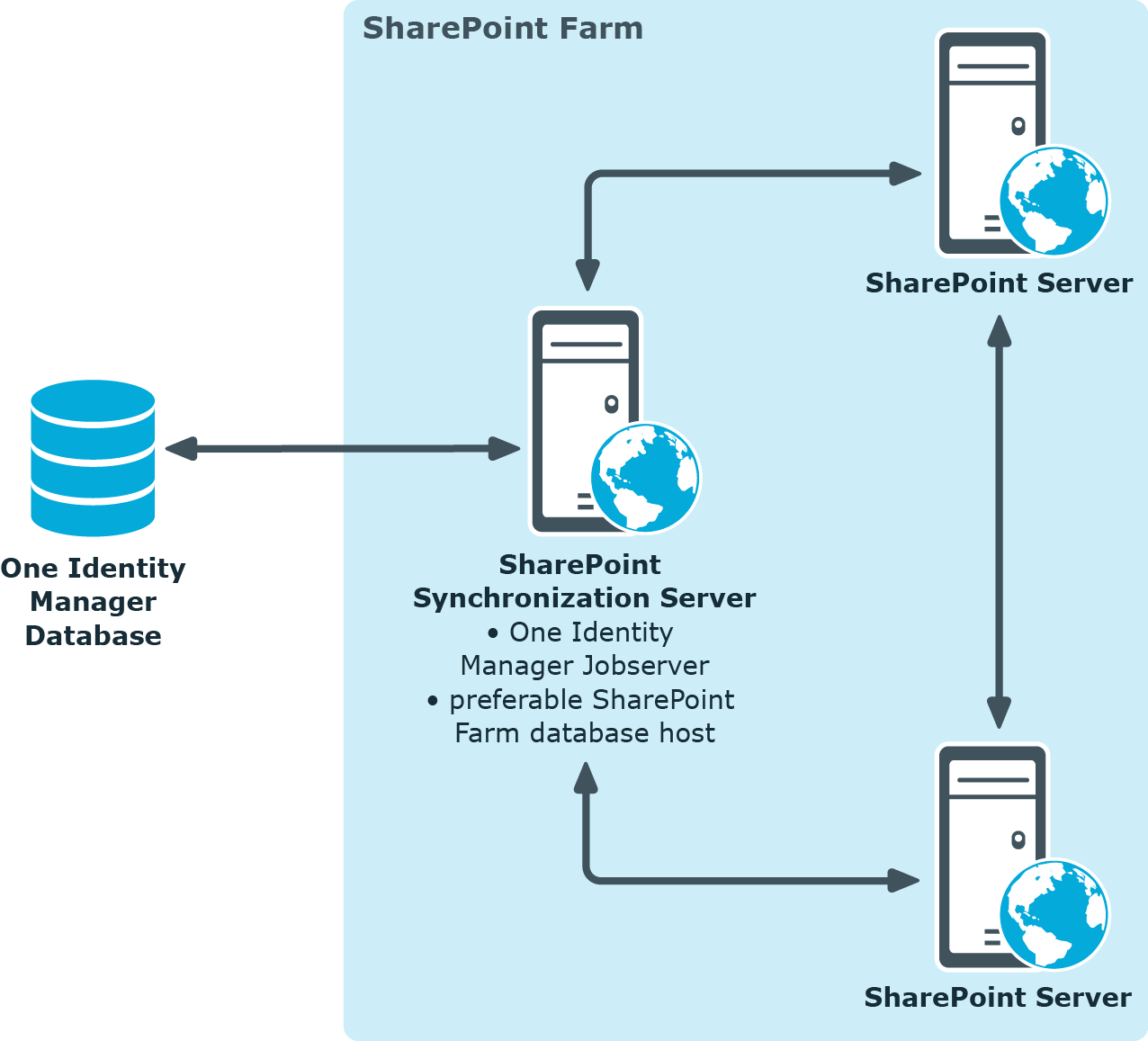
To be able to synchronize and provision, the SharePoint farm, the One Identity Manager Service, the SharePoint connector, and the Synchronization Editor must be installed on one of the servers. In the following, this server is known as the synchronization server. All One Identity Manager Service actions are run against the target system environment on the synchronization server. Data entries required for synchronization and administration with the One Identity Manager database are processed by the synchronization server.
Detailed information about this topic
One Identity Manager users for managing SharePoint
The following users are used setting up and administration of SharePoint with One Identity Manager.
Table 1: Users
| Target system administrators |
Target system administrators must be assigned to the Target systems | Administrators application role.
Users with this application role:
-
Administer application roles for individual target system types.
-
Specify the target system manager.
-
Set up other application roles for target system managers if required.
-
Specify which application roles for target system managers are mutually exclusive.
-
Authorize other identities to be target system administrators.
-
Do not assume any administrative tasks within the target system. |
| Target system managers |
Target system managers must be assigned to the Target systems | SharePoint application role or a child application role.
Users with this application role:
-
Assume administrative tasks for the target system.
-
Create, change, or delete target system objects.
-
Edit password policies for the target system.
-
Prepare system entitlements to add to the IT Shop.
-
Can add identities that do not have the Primary identity identity type.
-
Configure synchronization in the Synchronization Editor and define the mapping for comparing target systems and One Identity Manager.
-
Edit the synchronization's target system types and outstanding objects.
-
Authorize other identities within their area of responsibility as target system managers and create child application roles if required. |
| One Identity Manager administrators |
administrator and administrative system users Administrative system users are not added to application roles.
administrators:
-
Create customized permissions groups for application roles for role-based login to administration tools in the Designer as required.
-
Create system users and permissions groups for non role-based login to administration tools in the Designer as required.
-
Enable or disable additional configuration parameters in the Designer as required.
-
Create custom processes in the Designer as required.
-
Create and configure schedules as required.
-
Create and configure password policies as required. |
| Administrators for the IT Shop |
Administrators must be assigned to the Request & Fulfillment | IT Shop | Administrators application role.
Users with this application role:
|
|
Product owners for the IT Shop |
Product owners must be assigned to the Request & Fulfillment | IT Shop | Product owners application role or a child application role.
Users with this application role:
|
| Administrators for organizations |
Administrators must be assigned to the Identity Management | Organizations | Administrators application role.
Users with this application role:
|
| Business roles administrators |
Administrators must be assigned to the Identity Management | Business roles | Administrators application role.
Users with this application role:
|
Claims-based authentication
One Identity Manager supports claims-based authentication as well as classical Windows authentication for logging in to the SharePoint server. Information about the SharePoint provider and authentication modes are stored in the database for this purpose. Existing SharePoint providers for claims-based authentication are loaded into the database during synchronization. Registered providers are stored for each web application.
Every user account stores which authentication mode the user with this user account uses to log in. The default authentication mode depends on whether claims-based authentication is permitted with the associated web applications.
The authentication mode is required to add user accounts to One Identity Manager. The user account login name for claims-based authentication contains a prefix that depends on which authentication mode is used. These prefixes are maintained with the authentication modes.
Related topics