Modes of operation
One Identity Safeguard for Privileged Sessions (SPS) can be configured to monitor both transparent and non-transparent connections.
-
In transparent mode, SPS acts as a transparent router between two network segments. For details, see Transparent mode.
-
You can also use policy-based routing to forward connections within the same network segment to SPS, in which case it acts like a single interface transparent router. For details, see Single-interface transparent mode.
-
In non-transparent mode, users have to address SPS to initiate connections to protected servers. For details, see Non-transparent mode.
-
When addressing SPS, you can also use inband destination selection to choose the server to connect to. For details, see Inband destination selection.
One Identity recommends that you design the network topology so that only management and server administration traffic passes SPS. This ensures that the services and applications running on the servers are accessible even in case SPS breaks down, so SPS cannot become a single point of failure.
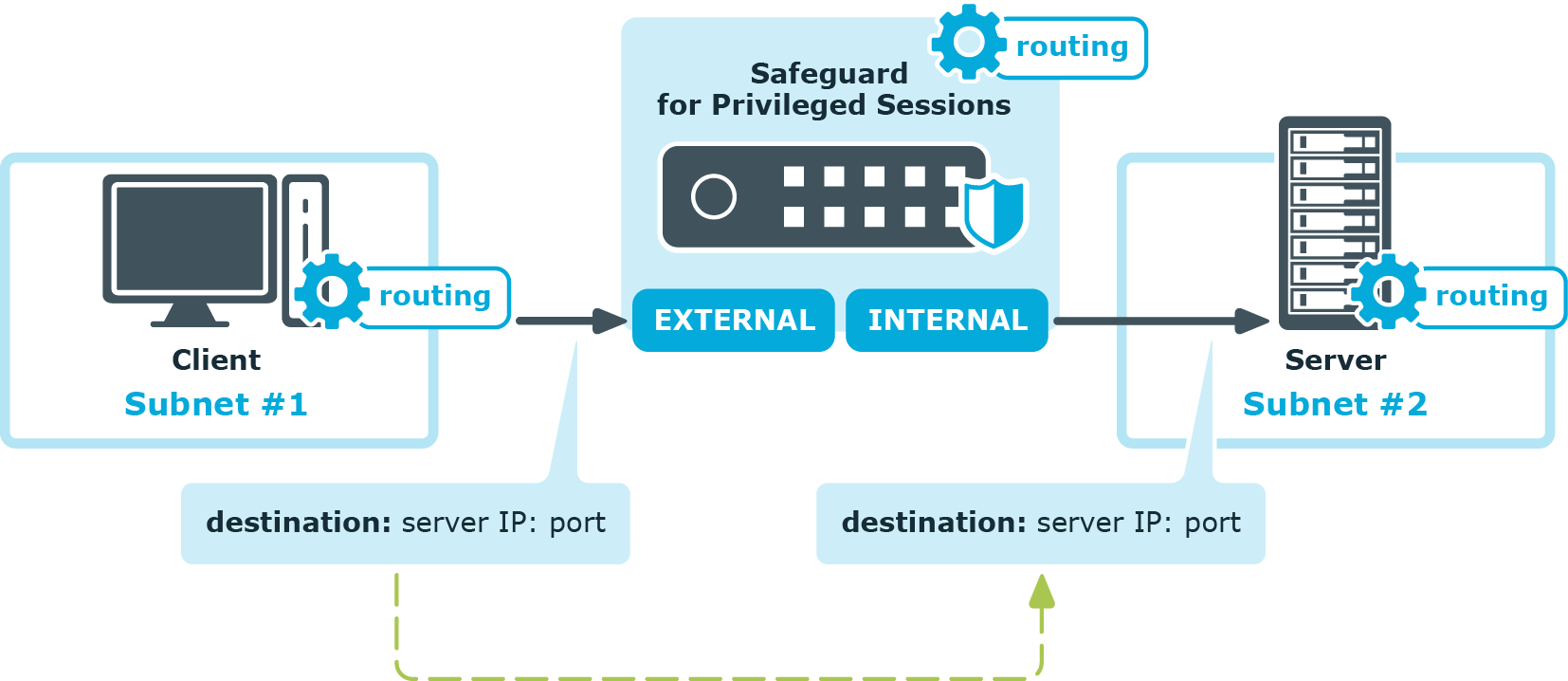
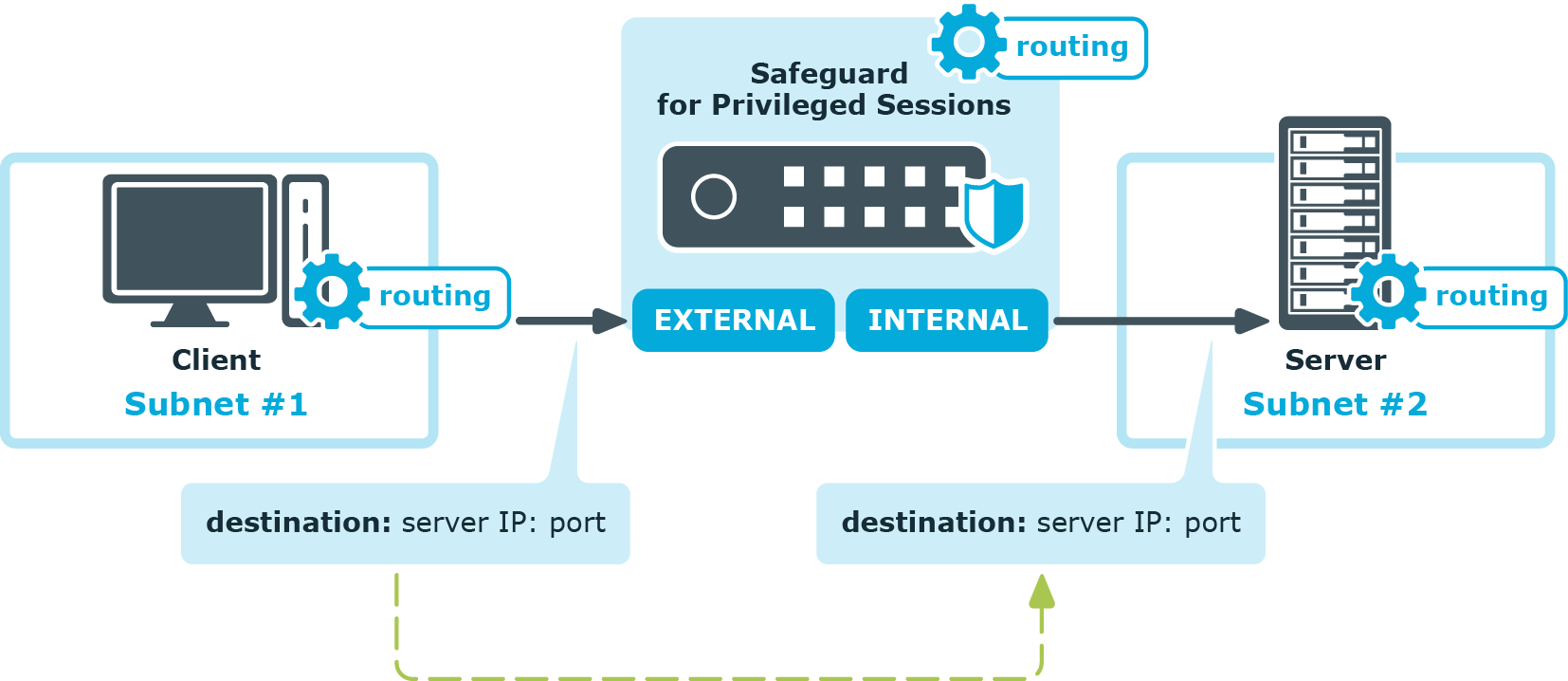
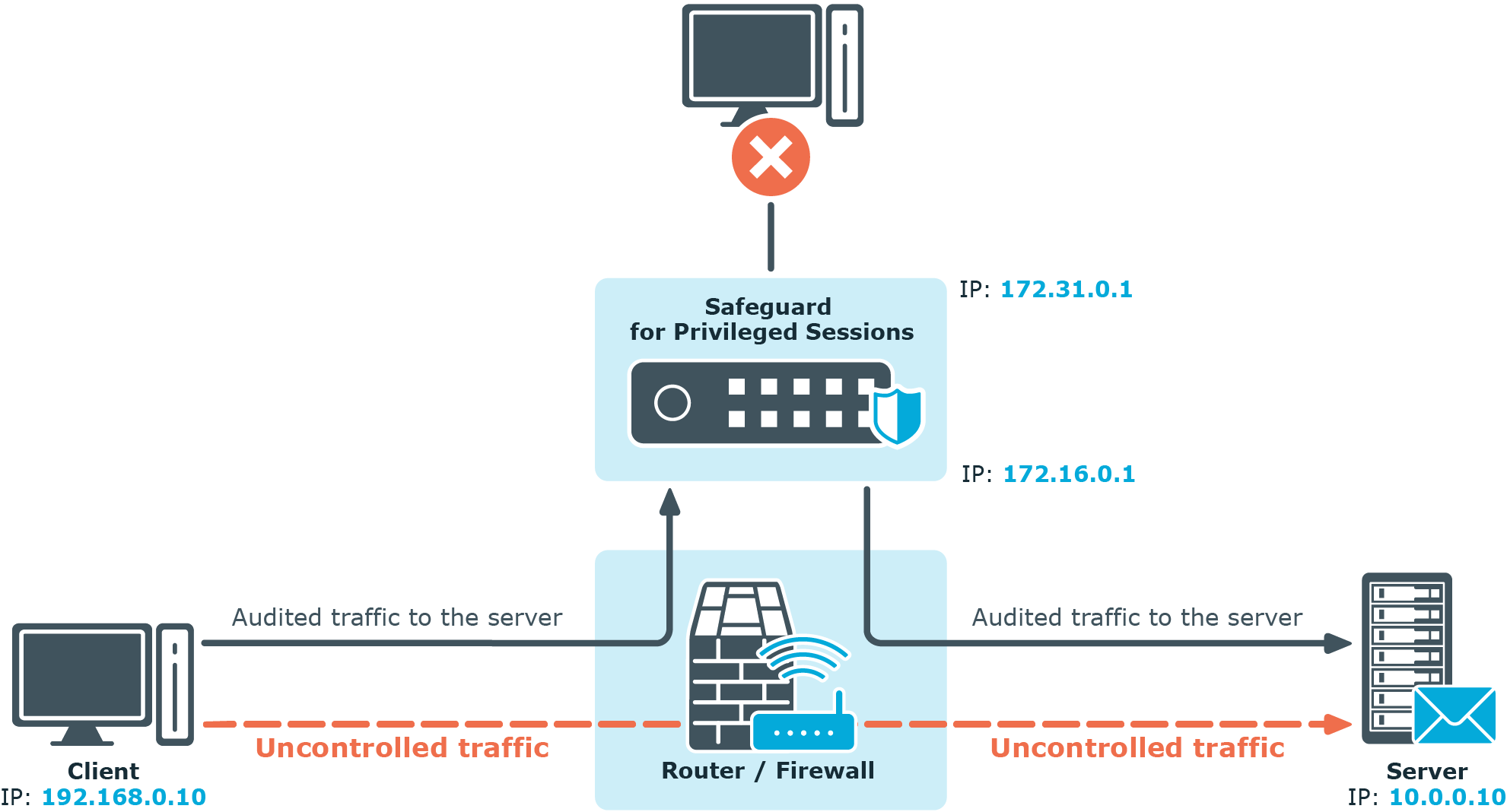
Transparent mode
In transparent mode, One Identity Safeguard for Privileged Sessions (SPS) acts as a transparent router connecting the network segment of the administrators to the segment of the protected servers at the network layer (Layer 3 in the OSI model). All connections must pass through SPS to reach the servers — SPS is a proxy gateway, completely separating the protected servers from the rest of the network. Controlled connections and traffic are inspected on the application level, while other types of connections are simply forwarded on the packet level.
SPS can also be configured to act as a single-interface transparent router. For details, see Single-interface transparent mode.
|

|
Caution:
Transparent mode does not support multicast traffic. |
Figure 8: SPS in transparent mode
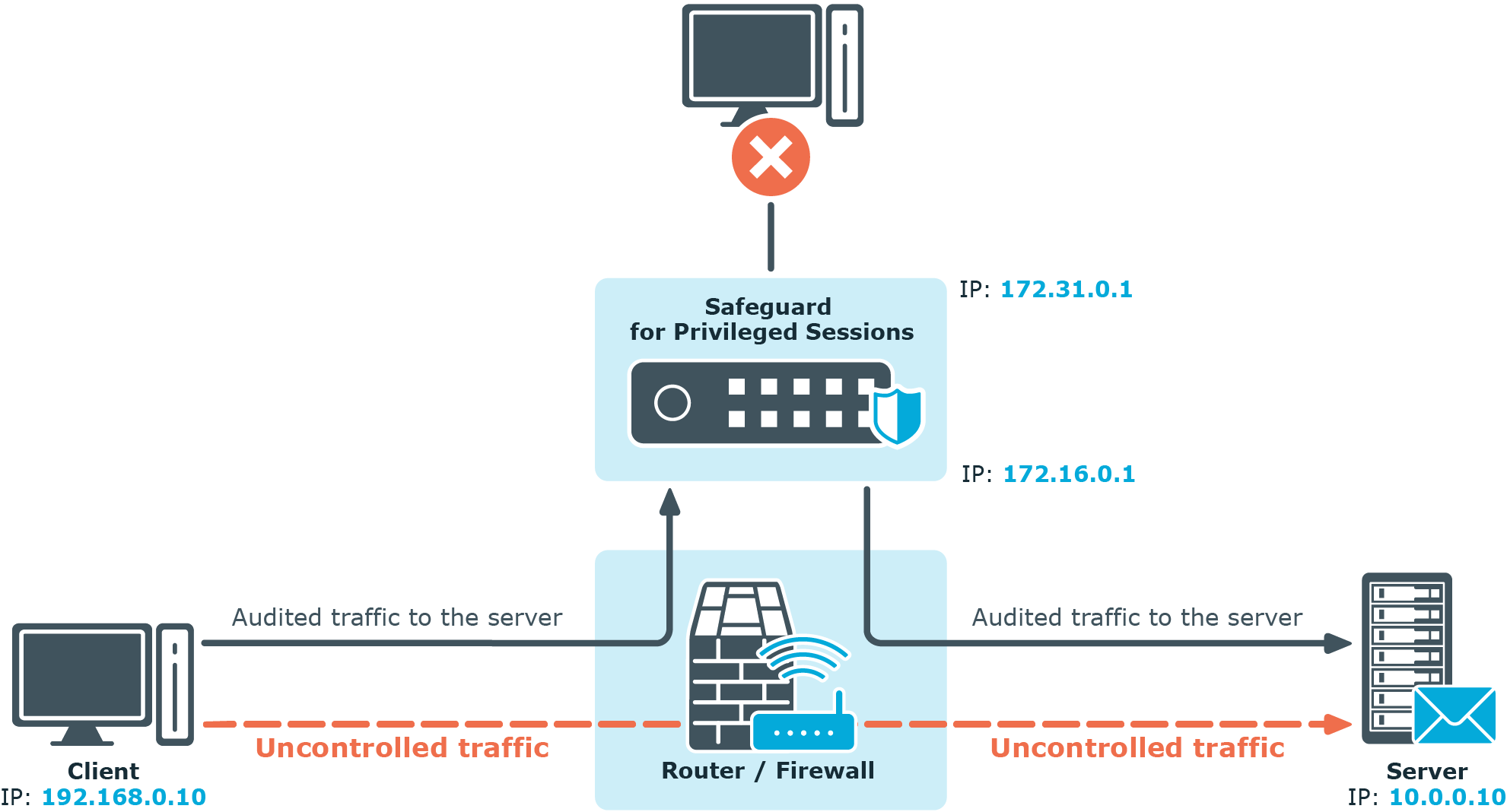
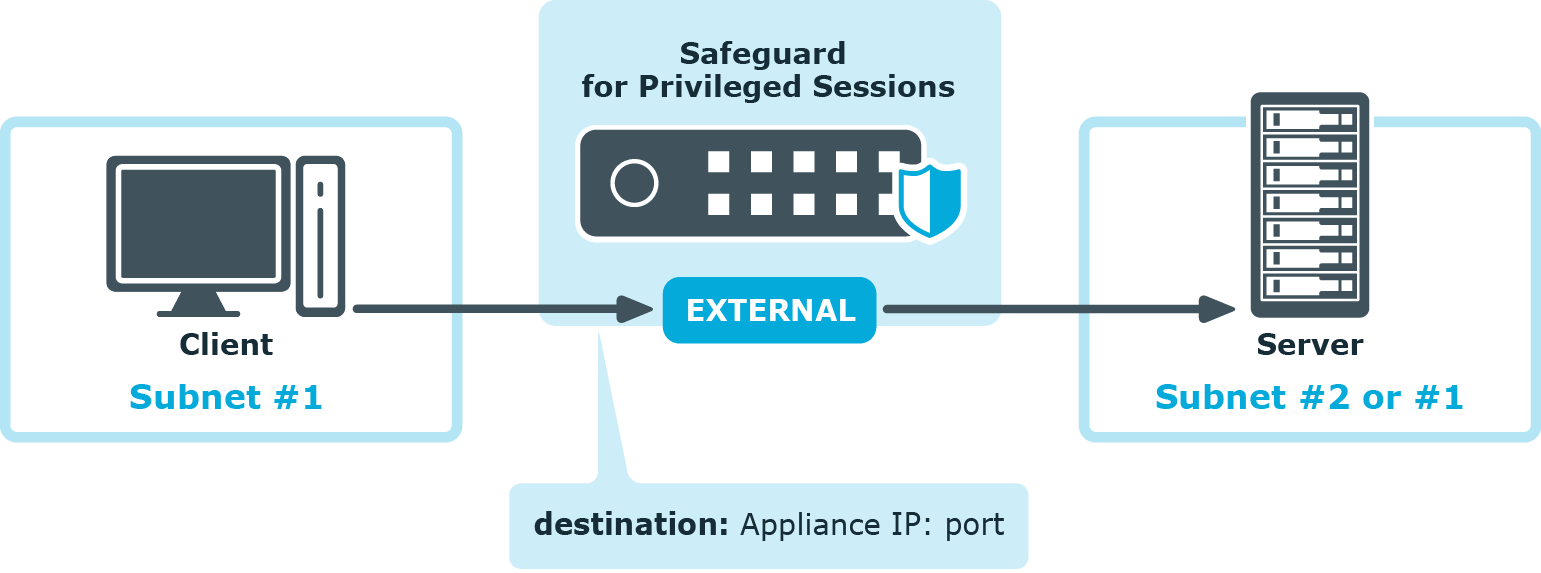
Single-interface transparent mode
Single-interface transparent mode is similar to transparent mode, but both client-side and server-side traffic use the same interface. An external device that actively redirects the audited traffic to One Identity Safeguard for Privileged Sessions (SPS) (typically, a firewall, a router, or a layer3 switch) is required . To accomplish this, the external device must support advanced routing (also called policy-based routing or PBR). For details on configuring an external device to work with SPS in single-interface transparent mode, see Configuring external devices in the Administration Guide.
Figure 9: SPS in single-interface transparent mode
Advantages
The advantages of using the single-interface transparent mode are:
-
Totally transparent for the clients, no need to modify their configuration.
-
The network topology is not changed.
-
Only the audited traffic is routed to SPS, production traffic is not.
Disadvantages
The disadvantages of using the single-interface transparent mode are:
-
SPS acts as a man-in-the-middle regarding the connection between the client and the target server. Instead of a single client-server connection, there are two separate connections: the first between the client and SPS, and a second between SPS and the server. Depending on how you configure SPS, the source IP in the SPS-server connection can be the IP address of SPS, or the IP address of the client. In the latter case — when operating in transparent mode (including single-interface transparent mode) — SPS performs IP spoofing. Consult the security policy of your organization to see if it permits IP spoofing on your network.
-
Traffic must be actively routed to SPS using an external device. Consequently, a network administrator can disable SPS by changing routing rules.
-
When adding a new port or subnet to the list of audited connections, the configuration of the external device must be modified as well.
-
A network administrator can (intentionally or unintentionally) easily disable monitoring of the servers, therefore additional measures have to be applied to detect such activities.
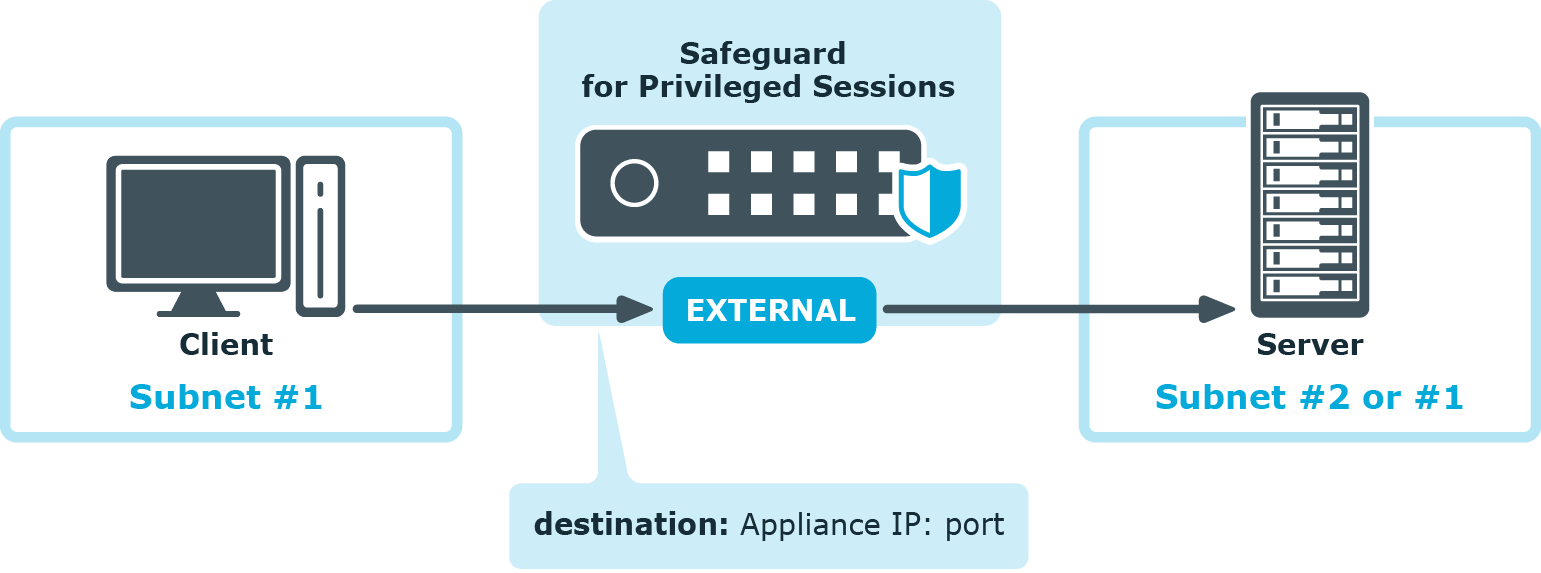
Non-transparent mode
In non-transparent mode, One Identity Safeguard for Privileged Sessions (SPS) acts as a bastion host (that is, administrators can address only SPS, the administered servers cannot be targeted directly). The firewall of the network has to be configured to ensure that only connections originating from SPS can access the servers. SPS determines which server to connect to based on the parameters of the incoming connection (the IP address of the administrator and the target IP and port).
Non-transparent mode inherently ensures that only the controlled (management and server administration) traffic reaches SPS. Services and applications running on the servers are accessible even in case SPS breaks down, so SPS cannot become a single point of failure.
TIP: Non-transparent mode is useful if the general (that is, not inspected) traffic is very high and could not be forwarded by SPS.
NOTE: In case there is a high number of target devices, do not use fixed address rules in non-transparent mode, as configuration validation might fail. Consider using one of the dynamic configuration options, such as inband destination selection or transparent mode.
Figure 10: SPS in non-transparent mode
Non-transparent mode is often used together with inband destination selection. For details, see Inband destination selection).