Managing the indexers
The indexers that run on an external host send log messages into the standard syslog of the external host. These log messages are not visible on One Identity Safeguard for Privileged Sessions (SPS).
The indexers use the standard init.d framework of the host. You can restart the indexer processes using the /etc/init.d/indexerworker restart command, and the entire indexer service using the /etc/init.d/external-indexer restart command. Note that restarting the indexer service automatically restarts the worker processes as well.
The hosts that are running indexers should be visible in the list of indexers on the Indexer > Worker status page of the SPS web interface.
Upgrading the external indexer
This section describes how to upgrade the indexer application on your external indexer hosts.
|

|
Caution:
After SPS 6.5, CentOS 6 operating systems will not be supported for external indexers. This means that after upgrading to SPS 6.5, or the LTS maintanance release in that cadence, you will not be able to use your external indexers that are running on CentOS 6. Make sure that you prepare your affected systems for this change and upgrade to CentOS 7 or later. |
NOTE: The version of the external indexer must be equal to or greater than the version of One Identity Safeguard for Privileged Sessions (SPS). To make sure you meet this criterion, One Identity recommends that you always upgrade your external indexer when you upgrade SPS. You can check that SPS has established a connection to the external indexer on the Indexer > Worker status page of the SPS web interface.
Prerequisites
Before you start, create a backup copy of the /etc/indexer/indexerworker.cfg and /etc/indexer/indexer-certs.cfg indexer configuration files.
To upgrade the indexer application on your external indexer hosts
-
Download the latest indexer .rpm package from the Basic Settings > Local Services > Indexer service page of the SPS web interface.
NOTE: Due to legal reasons, installation packages of the external indexer application will be available only from the SPS web interface. After SPS versions 6.4 and 6.0.3 are released, the installation packages will be removed from our website.
-
Copy the downloaded .rpm package to your external indexer hosts.
-
Stop the indexer by using the following command.
-
On Red Hat or CentOS 6.5:
service external-indexer stop
-
On Red Hat or CentOS 7:
systemctl stop external-indexer.service
-
Execute the following command: yum upgrade -y indexer.rpm
-
Resolve any warnings displayed during the upgrade process.
-
Restart the indexer by using the following command.
-
On Red Hat or CentOS 6.5:
service external-indexer start
-
On Red Hat or CentOS 7:
systemctl start external-indexer.service
-
Repeat this procedure on every indexer host.
Troubleshooting external indexers
The indexers that run on an external host send log messages into the standard syslog of the external host. These log messages are not visible on One Identity Safeguard for Privileged Sessions (SPS). If a problem occurs, check the logs of SPS and the external indexer to find out which component on which host causes the problem. If the problem is on the external indexer host, verify that the required decryption keys are available on the host, then restart the indexer service using the following command.
-
On Red Hat or CentOS 6.5:
service external-indexer restart
-
On Red Hat or CentOS 7:
systemctl restart external-indexer.service
If the problem persists, contact our Support Team. You can increase the log level of the indexer processes from the configuration file.
Monitoring the status of the indexer services
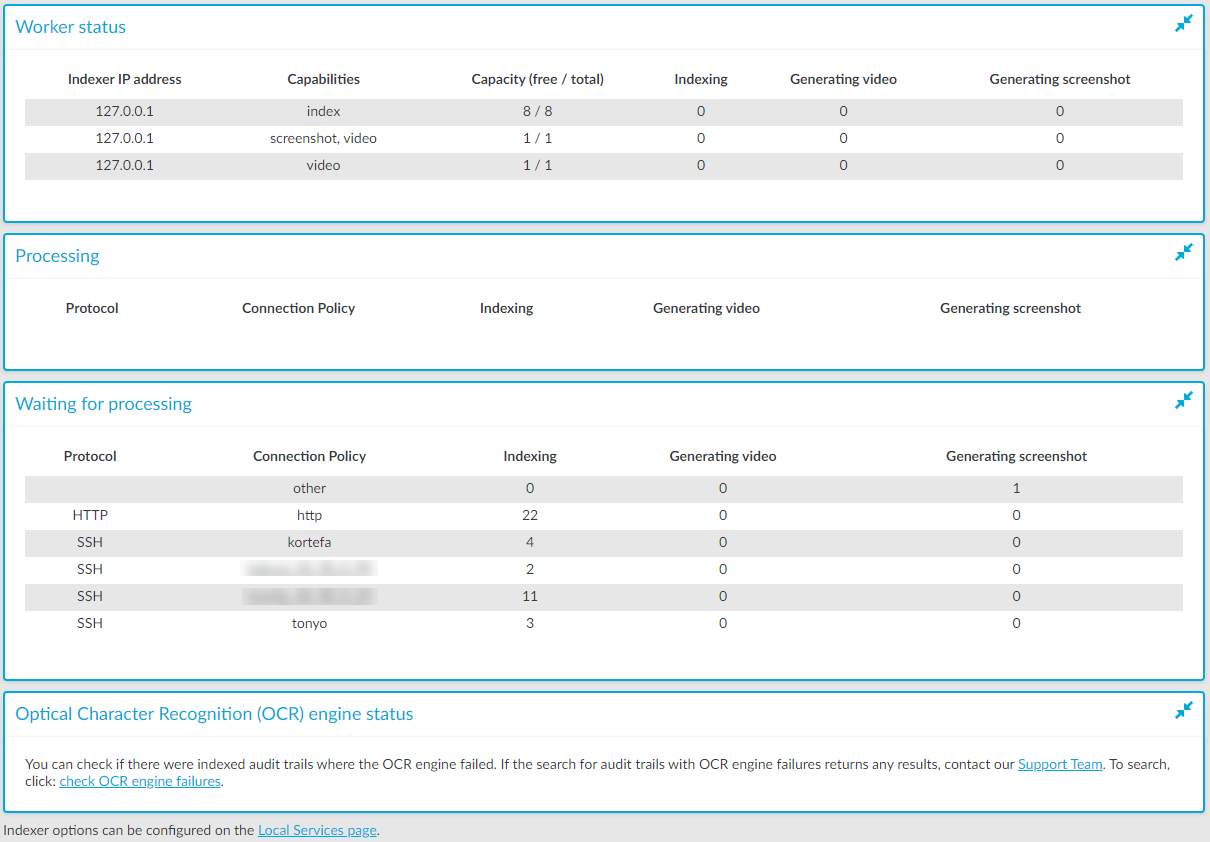
The status of audit-trail processing is displayed on the Indexer page of the Main Menu.
Elements of the Indexer page
The following list describes the elements of the Indexer page and their functions.
-
Worker status: displays various data about the worker groups.
-
Indexer IP address: displays the IP address of the indexer (either the indexer running on One Identity Safeguard for Privileged Sessions (SPS) or an external indexer). It may display the following:
- 127.0.0.1: indicated the indexer running on SPS.
- An IP address other than127.0.0.1: indicates an external indexer.
-
Capabilities: the type of job(s) this worker will perform.
-
Capacity: the available and total Capacity (Maximum parallel audit trails to process) of the indexer, and also the number of active processes that are Indexing an audit trail, or Generating video or Generating screenshot.
-
Processing: audit trails that are currently being processed per connection policy.
-
Waiting for processing: audit trails waiting to be processed.
When you see audit trails in the Indexing column, that could mean any of the following:
-
The maximal queue size is 1000. If there are many trails waiting to be indexed, SPS will keep lots of trails in the queue.
-
The worker with the appropriate key for decryption is not available at the moment, and other workers do not have the required key.
-
There are no workers available that have the required capability.
-
Optical Character Recognition (OCR) engine status: It allows you to check and report if there were indexed audit trails where the OCR engine failed. Perform a search on the Search interface using the provided link and if the search returns any results, contact our Support Team to submit a report.
Figure 245: Indexer > Indexer status — Monitoring the status of the indexers
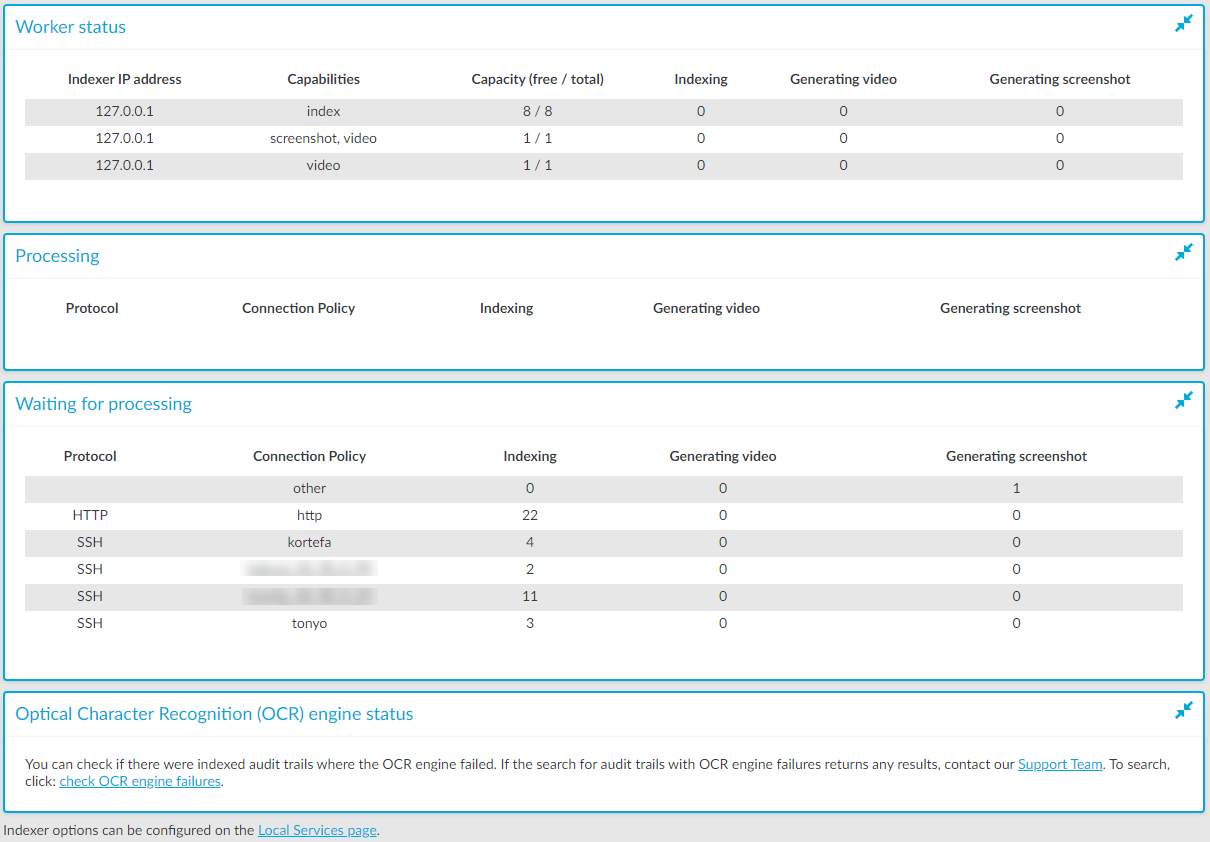
To automatically refresh the Indexer Status page every 5 seconds, select Auto refresh. To refresh the page immediately, click Refresh now.