The current version of One Identity Safeguard for Privileged Sessions (SPS) has the following limitations:
- TDS protocol version 7.3 or later is required.
- Due to the TDS protocol version requirement, Microsoft® SQL Server® 2008, or later, is recommended.
- The Require Gateway Authentication on the SPS Web Interface option in MSSQL Control > Connections does not work in case of MSSQL connections.
-
MSSQL server with TCP dynamic port settings is not supported.
You must specify a static TCP port for every instance in the SQL Server Configuration Manager you want to audit. By doing so, you can configure the access to multiple MSSQL instances with multiple connection policies and specify the instances with inband or fixed targets and ports. You can also create and assign different Credential Store policies to check out SQL users' passwords of the instances.
In the MSSQL client program, always specify the address with the port number of the SPS connection policy you want to connect to.
The available MSSQL channel types and their functionalities are described below. For details on configuring Channel Policies, see Creating and editing channel policies. For a list of supported client applications, see Supported protocols and client applications.
-
MSSQL: Enables you to use the MSSQL protocol. This channel must be enabled for MSSQL to work.
The available channel policy options are the following: From, Target, Time policy, Four-eyes, Record audit trail, Gateway groups, Remote groups, and Content policy. Note that the Gateway groups option is used only if the user performs inband authentication using one of the supported MSSQL authentication methods (see Authentication in MSSQL). To retrieve the groups of an authenticated user from an LDAP database, you must also set an LDAP Server in the Connection Policy (for MSSQL connections, One Identity Safeguard for Privileged Sessions (SPS) uses this server only to retrieve the group membership of authenticated users, you cannot authenticate the users to LDAP from SPS). For details on configuring these options, see Creating and editing channel policies.
When setting Target, note the following:
-
If the connection uses DNAT (NAT destination address), the target address of the original client will be compared to the Target parameter of the Channel policy, that is not necessarily equivalent with the server's address.
-
If the connection is redirected to a Fix address, the redirected address will be compared to the Target parameter of the Channel policy.
For the audited MSSQL connections, Safeguard for Privileged Sessions(SPS) supports SQL Server Authentication.
SPS records the username used in the authentication process into the Username and Remote username fields of the connection database.
For authenticated sessions, SPS can perform group-based user authorization that allows you to finetune access to your servers and services: you can set the required group membership in the Channel policy of the MSSQL connection. Note that group-based authorization in MSSQL works only for authenticated sessions (for MSSQL connections, SPS uses this server only to retrieve the group membership of authenticated users, you cannot authenticate the users to LDAP from SPS). If a username is not available for the session, SPS will permit the connection even if the Remote groups field is set.
SPS does not store failed MSSQL authentication attempts in the connection database. This means that the Verdict field of the Search page will never contain CONN-AUTH-FAIL values for MSSQL connections.
An authentication policy is a list of authentication methods that can be used in a connection. Connection definitions refer to an authentication policy to determine how the client can authenticate to the target server. Separate authentication methods can be used on the client and the server-side of the connection.
To create a new authentication policy
-
Navigate to MSSQL Control > Authentication Policies, and click  .
.
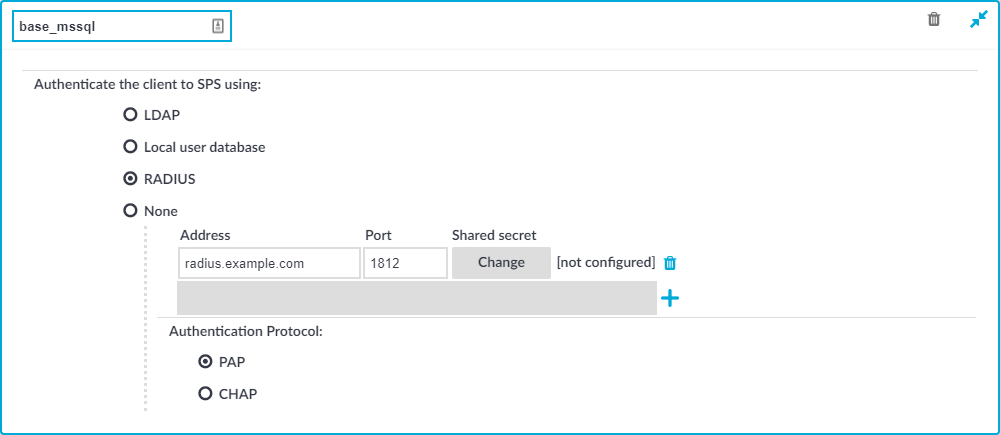
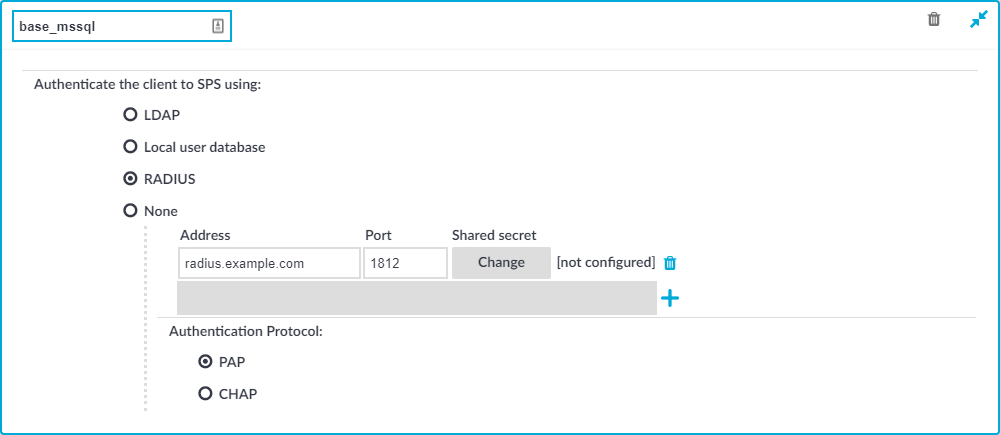
Figure 202: MSSQL Control > Authentication Policies — Configuring MSSQL authentication policies
-
Enter a name for the policy into the Name field.
-
Select the authentication method used on the client-side in the Authenticate the client to SPS using field. For the client-side connection, SPS can authenticate the client inband (within the MSSQL protocol) using the following authentication methods:
-
LDAP: SPS will authenticate the client to the LDAP database set in the LDAP Server of the connection policy. To use LDAP authentication on the client side, select Authenticate the client to SPS using > LDAP.
NOTE:SPS will authenticate the client-side connection to the LDAP server configured in the connection policy. This is not necessarily the same as the LDAP server used to authenticate the users accessing the SPS web interface.
-
Local user database: Authenticate the client locally on the SPS gateway using a Local user database. Select the database to use in the Local user database field. For details on creating a Local User Database, see Creating a Local User Database.
-
RADIUS: SPS will authenticate the client to the specified RADIUS server. Select Authenticate the client to SPS using > RADIUS, enter the IP address or hostname of the RADIUS server into the Address field, the port number of the RADIUS server into the Port field, and the shared secret of the RADIUS server into the Shared secret field. Only password-authentication is supported (including one-time passwords), challenge-response based authentication is not.
Use an IPv4 address.
To add more RADIUS servers, click  and fill in the respective fields.
and fill in the respective fields.
-
None: Do not perform client-side authentication, the client will authenticate only on the target server.
|

|
Caution:
Hazard of security breach. If the None authentication option is selected on the client side and SPS is configured to use public-key or certificate based authentication on the server, the user will not be authenticated at all unless gateway authentication is required for the connection. |
-
Click  .
.

 .
.

 .
.