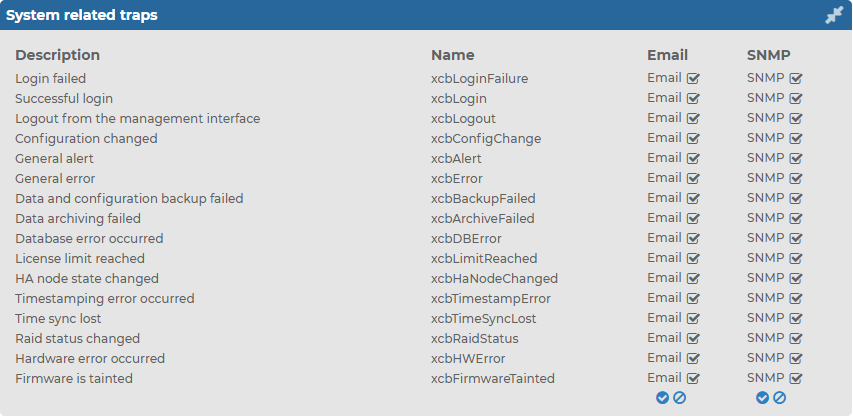
System related traps
This section provides detailed information about system related SNMP traps. For more information about configuring SNMP traps, see Health related traps and SNMP trap settings.
To enable Email notifications and SNMP trap notifications related to syslog-ng
-
Navigate to Basic Settings > Alerting > System related traps.
-
Select Email and/or SNMP for the traps you want to be notified about, then click  .
.
Figure 58: Basic Settings > Alerting > System related traps
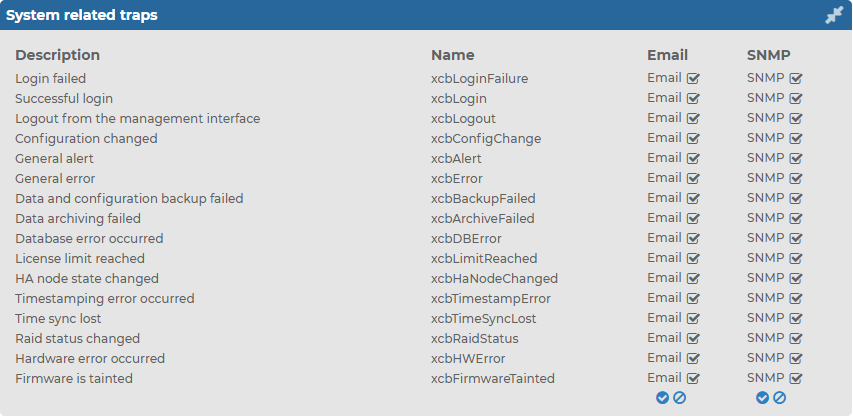
The following table provides detailed information about the system related SNMP traps .
Table 5: System related traps
| Login failed |
xcbLoginFailure |
Failed login attempts from syslog-ng Store Box (SSB) web interface. |
| Successful login |
xcbLogin |
Successful login attempts into SSB web interface. |
| Logout from the management interface |
xcbLogout |
Logouts from SSB web interface. |
| Configuration changed |
xcbConfigChange |
Any modification of SSB's configuration. |
| General alert |
xcbAlert |
General alerts and error messages occurring on SSB.
Note, that alerts on general alerts and errors are sent whenever there is an alert or error level message in the SSB system log. These messages are very verbose and mainly useful only for debugging purposes.
Enabling these alerts may result in multiple e-mails or SNMP traps sent about the same event. |
| General error |
xcbError |
| Data and configuration backup failed |
xcbBackupFailed |
Alerts if the backup procedure is unsuccessful. |
| Data archiving failed |
xcbArchiveFailed |
Alerts if the archiving procedure is unsuccessful. |
| Database error occurred |
xcbDBError |
An error occurred in the database where SSB stores alerts and accounting information. Contact our support team (see About us for contact information). |
| License limit reached |
xcbLimitReached |
Maximum number of clients has been reached. |
| HA node state changed |
xcbHaNodeChanged |
A node of the SSB cluster changed its state (for example, a takeover occurred). |
| Timestamping error occured |
xcbTimestampError |
An error occurred during the time stamping process (for example, the time stamping server did not respond). |
| Time sync lost |
xcbTimeSyncLost |
The system time became out of sync. |
| Raid status changed |
xcbRaidStatus |
The status of the node's RAID device changed its state. |
| Hardware error occured |
xcbHWError |
SSB detected a hardware error. |
| Firmware is tainted |
xcbFirmwareTainted |
A user has locally modified a file from the console. |
| Disk usage is above the defined ratio |
xcbDiskFull |
Disk space is used above the limit set in Disk space fill up prevention. |
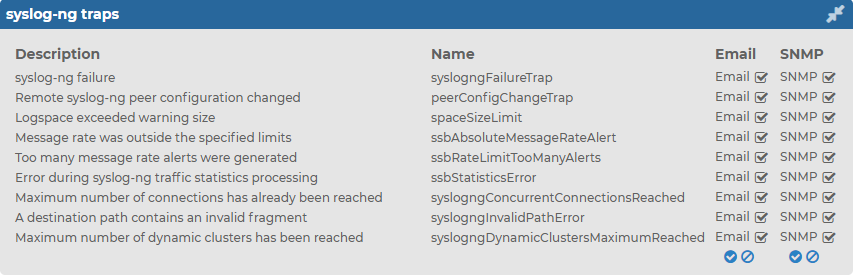
Alerts related to syslog-ng PE
This section provides detailed information about alerts related to syslog-ng PE.
To enable Email notifications and SNMP trap notifications related to syslog-ng
-
Navigate to Basic Settings > Alerting > syslog-ng traps.
-
Select Email and/or SNMP for the traps you want to be notified about, then click 
Figure 59: Basic Settings > Alerting > syslog-ng traps
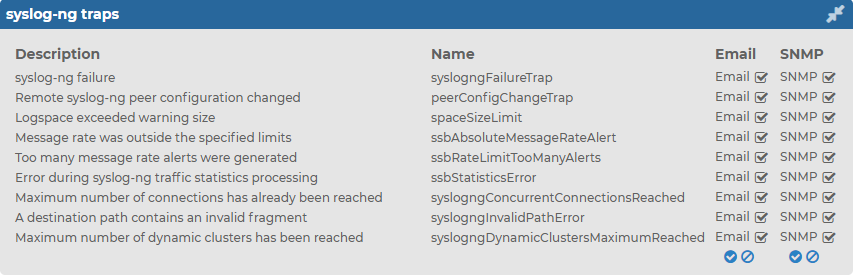
The following table provides detailed information about the SNMP traps related to syslog-ng PE.
Table 6: Alerts related to
| syslog-ng failure |
syslogngFailureTrap |
The syslog-ng PE application did not start properly, shut down unexpectedly, or encountered another problem. Depending on the error, syslog-ng Store Box (SSB) may not accept incoming messages or send them to the destinations. |
| Remote syslog-ng peer configuration changed |
peerConfigChangeTrap |
The configuration of the syslog-ng PE application running on a remote host that sents its logs to SSB has been changed. Note that such changes are detected only if the remote peer uses at least version 3.0 of syslog-ng PE or version 3.0 of the syslog-ng Agent, and if messages from the internal source are sent to SSB. |
| Logspace exceeded warning size |
spaceSizeLimit |
The size of a logspace has exceeded the size set as warning limit. |
| Message rate was outside the specified limits |
ssbAbsoluteMessageRateAlert |
The message rate has exceeded the minimum or maximum value. |
| Too many message rate alerts were generated |
ssbRateLimitTooManyAlerts |
SSB is generating too many message rate alerts, probably due to unusual traffic that may need investigation and further user actions. |
| Error during syslog-ng traffic statistics processing |
ssbStatisticsError |
There was an error during querying and processing statistics of incoming, forwarded, stored, and dropped messages. |
| Maximum number of connections has already been reached |
syslogngConcurrentConnectionsReached |
There was an attempt to establish a new connection but this would have meant exceeding the log source's maximum number of allowed connections (set in Log > Sources > Maximum connections). The new connection was refused by syslog-ng PE. |
| A destination path contains an invalid fragment |
syslogngInvalidPathError |
The application was unable to open a specific logspace destination, because its path contains a prohibited fragment (such as a reference to a parent directory). |
| Maximum number of dynamic clusters has been reached |
syslogngDynamicClustersMaximumReached |
SSB collects various statistics about log messages received, processed, and dropped for objects (every source, destination, and individual application or program). To avoid performance issues, the maximal number of objects that SSB collects statistics for is 100000. This alert means that SSB has reached this limit. |
Data and configuration backups
Backups create a snapshot of syslog-ng Store Box (SSB)'s configuration or the data which can be used for recovery in case of errors. SSB can create automatic backups of its configuration and the stored logs to a remote server.
To configure backups, you first have to create a backup policy. Backup policies define the address of the backup server, which protocol to use to access it, and other parameters. SSB can be configured to use the Rsync, SMB/CIFS, and NFS protocols to access the backup server:
The different backup protocols assign different file ownerships to the files saved on the backup server. The owners of the backup files created using the different protocols are the following:
-
Rsync: The user provided on the web interface.
-
SMB/CIFS: The user provided on the web interface.
-
NFS: root with no-root-squash, nobody otherwise.
|

|
Caution:
SSB cannot modify the ownership of a file that already exists on the remote server. If you change the backup protocol but you use the same directory of the remote server to store the backups, make sure to adjust the ownership of the existing files according to the new protocol. Otherwise SSB cannot overwrite the files and the backup procedure fails. |
Once you have configured a backup policy, set it as a system backup policy (for configuration backups) or data backup policy (for logspace backups):
NOTE: Backup deletes all other data from the target directory, restoring a backup deletes all other data from SSB. For details on restoring configuration and data from backup, see Restoring SSB configuration and data.
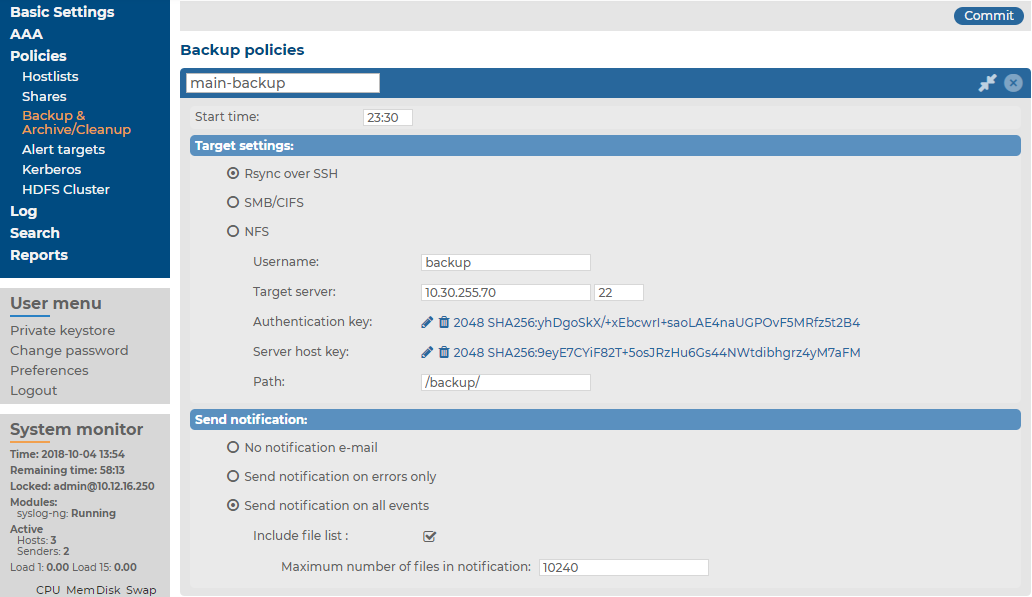
Creating a backup policy using Rsync over SSH
The Rsync over SSH backup method connects the target server with SSH and runs the rsync UNIX command to copy the data to the remote server. syslog-ng Store Box (SSB) authenticates itself with a public key — password-based authentication is not supported.
|

|
Caution:
The backup server must run rsync version 3.0 or newer. |
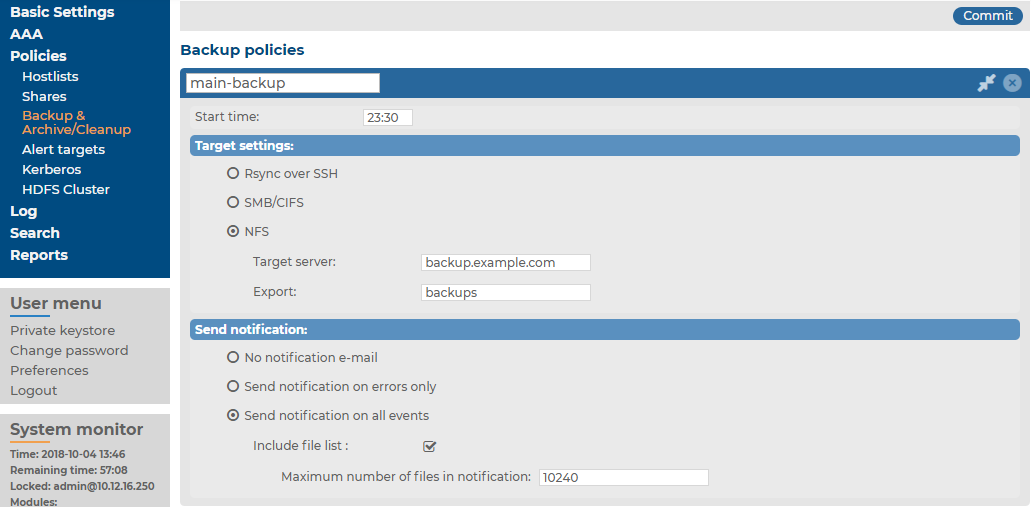
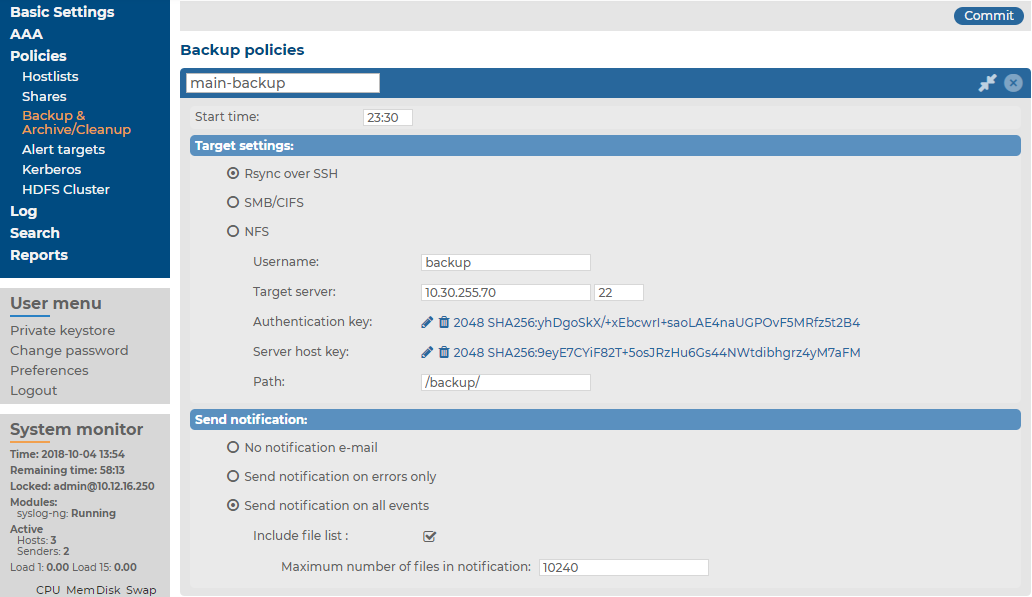
To create a backup policy using Rsync over SSH
-
Navigate to Policies > Backup & Archive/Cleanup, and click  in the Backup policies section to create a new backup policy.
in the Backup policies section to create a new backup policy.
Figure 60: Policies > Backup & Archive/Cleanup > Backup policies — Configure backup
-
Enter a name for the backup policy (for example, main-backup).
-
Enter the time when the backup process should start into the Start time field, in HH:MM format (for example, 23:30).
-
Enter the IP address or the hostname of the remote server into the Target server field (for example, backup.example.com).
-
Select Rsync over SSH from the Target settings radio buttons.
Figure 61: Policies > Backup & Archive/Cleanup > Backup policies — Configure backup using rsync
-
Enter the username used to logon to the remote server into the Username field.
-
Click  in the Authentication key field. A popup window is displayed.
in the Authentication key field. A popup window is displayed.
-
Generate a new keypair by clicking Generate or upload or paste an existing one. This key will be used to authenticate SSB on the remote server. The public key of this keypair must be imported to the remote server.
NOTE: The SSB currently generates an SSH RSA key with the size of 4096 bits (by default), or 2048 bits. The SSB can also generate an SSH Ed25519 key, which has a fixed size of 256 bits.
-
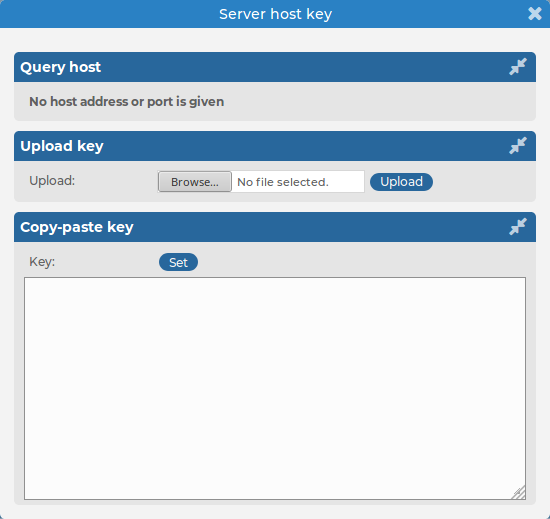
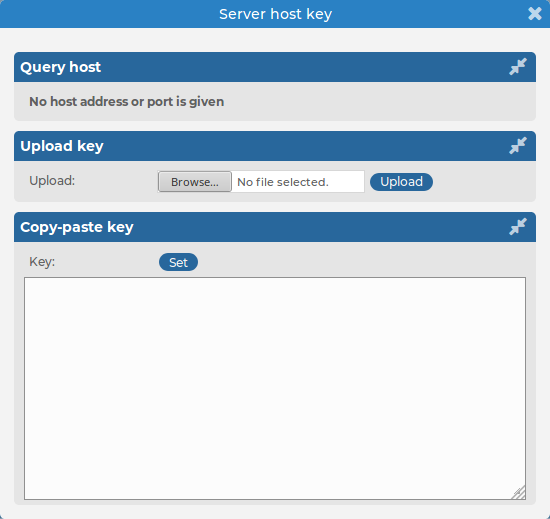
Click  in the Server host key field. A popup window is displayed.
in the Server host key field. A popup window is displayed.
-
Click Query to download the host key of the server, or upload or paste the host key manually. SSB will compare the host key shown by the server to this key, and connect only if the two keys are identical.
Figure 62: Policies > Backup & Archive/Cleanup > Backup policies > Rsync over SSH > Server host key — Configure SSH keys
-
Enter the port number of the SSH server running on the remote machine into the Port field.
-
Enter the path to the backup directory on the target server into the Path field (for example, /backups).
SSB saves all data into this directory, automatically creating subdirectories for logspaces. As a result, the same backup policy can be used for multiple logspaces. To ensure that a restore can be performed even if the logspace has been renamed, the subdirectories are created using a persistent internal ID of the logspace. To facilitate manual debugging, a text file is also saved in the directory with the name of the logspace, containing the internal ID for the logspace. This text file is only provided for troubleshooting purposes and is not used by SSB in any way.
-
To receive e-mail notification of the backup, select the Send notification on errors only or the Send notification on all events option. Notifications are sent to the administrator e-mail address set on the Management tab.
To include the list of files in the e-mail, select Send notification on all events and enable the Include file list option. However, note that if list is very long, the SSB web interface might become unaccessible. In this case, set the Maximum number of files in notification lower. After this number has been reached, file names will be omitted from the notification.
-
Click  .
.
-
To assign the backup policy to a logspace, see Creating data backups.
.


 in the Backup policies section to create a new backup policy.
in the Backup policies section to create a new backup policy.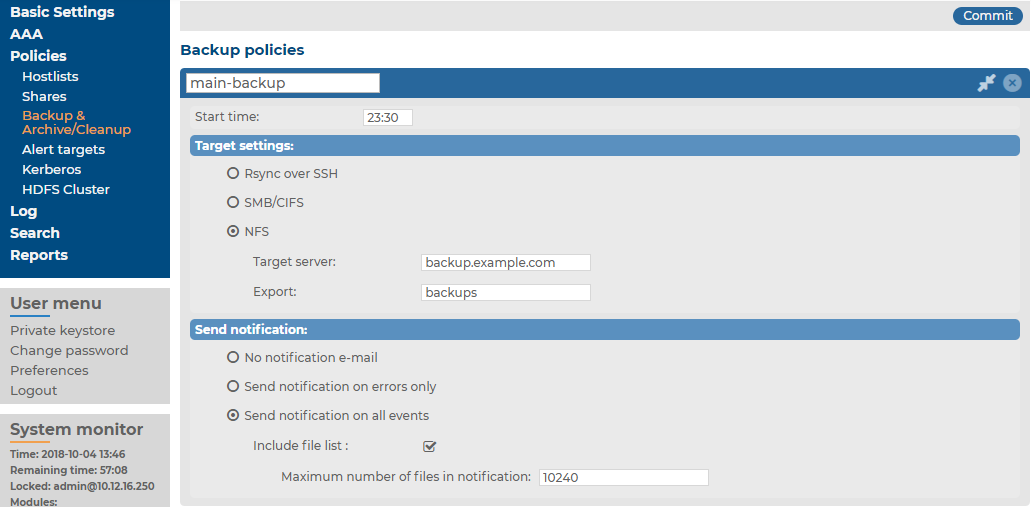
 in the Authentication key field. A popup window is displayed.
in the Authentication key field. A popup window is displayed.