User Account Deprovisioning
Policies in this category are intended to automate the following deprovisioning-related tasks on user accounts:
- Disable the user account.
- Set the user password to a random value.
- Set the user’s logon names to random values.
- Rename the user account.
- Modify other properties of the user account.
When configuring a policy of this category, you specify how you want Active Roles to modify the user’s account in Active Directory upon a request to deprovision a user so that once the deprovision operation is completed, the deprovisioned user cannot log on to the network.
You may also configure a policy to update any user properties, such as those that regulate users’ membership in Active Roles Managed Units. In this way, the policy can automate the addition or removal of deprovisioned users from Managed Units.
How this policy works
When processing a request to deprovision a user, Active Roles uses this policy to modify the user’s account so that once the user has been deprovisioned, they cannot log on to the network.
A policy can also be configured to update user accounts. Depending on the policy configuration, each policy-based update results in the following:
- Certain portions of account information are removed from the directory by resetting specified properties to empty values.
- Certain properties of user accounts are set to new, non-empty values.
A policy can be configured so that new property values include:
- Properties of the user account being deprovisioned, retrieved from the directory prior to starting the process of the user deprovisioning
- Properties of the user who originated the deprovisioning request
- Date and time when the user was deprovisioned
Thus, when deprovisioning a user, Active Roles modifies the user’s account in Active Directory as determined by the User Account Deprovisioning policy that is in effect.
How to configure a User Account Deprovisioning policy
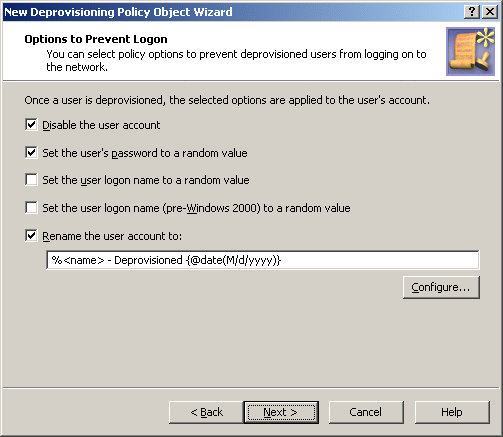
To configure a User Account Deprovisioning policy, select User Account Deprovisioning on the Policy to Configure page in the New Deprovisioning Policy Object wizard or in the Add Deprovisioning Policy wizard. Then, click Next to display the Options to Prevent Logon page.
Figure 68: User Account Deprovisioning
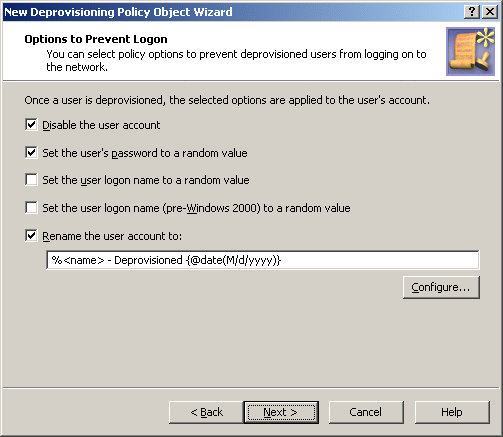
On this page, you can select options that make the account ineligible for logon. The option names are self-explanatory:
- Disable the user account
- Set the user’s password to a random value
- Set the user logon name to a random value
- Set the user logon name (pre-Windows 2000) to a random value
Select check boxes next to the options you want the policy to apply.
By selecting the Rename the user account to check box, you direct the policy to change the user name of the account. This option allows you to configure a property update rule that specifies how to modify the user name. The following subsection provides instructions on how to configure a property update rule, taking the user name as the example.
Configuring a property update rule
Configuring a property update rule
To configure a property update rule for the user name, click the Configure button. This displays the Configure Value dialog box, discussed earlier in this chapter (see How to configure a Property Generation and Validation policy). You can use that dialog box to set up a value for the ‘name’ must be condition, in the same way as you do when configuring a Property Generation and Validation policy.
To start configuring a value, click Add in the Configure Value dialog box. This displays the Add Entry window.
A value is a concatenation of one or more entries. In the Add Entry window, you can select the type of the entry to add, and then configure the entry. The following table summarizes the available types of entries.
Table 21: Types of entries: Configuring a property update rule
|
Text |
Adds a text string to the value. |
|
User Property |
Adds a selected property (or a part of a property) of the user account being deprovisioned. |
|
Parent OU Property |
Adds a selected property (or a part of a property) of an organizational unit in the hierarchy of containers above the user account being deprovisioned. |
|
Parent Domain Property |
Adds a selected property (or a part of a property) of the domain of the user account being deprovisioned. |
|
Date and Time |
Adds the date and time when the account was deprovisioned. |
|
Initiator ID |
Adds a string that identifies the Initiator, that is, the user who originated the deprovisioning request. This entry is composed of Initiator-related properties, retrieved from the directory. |
Instructions on how to configure an entry depend on the type of the entry. You can use the instructions outlined in the How to configure a Property Generation and Validation policy section earlier in this chapter to configure an entry of any of these types:
The following subsections elaborate on the Date and Time and Initiator ID entries.