Access to Active Roles Administration Service
You can set up a firewall between Active Roles client components, such as the Active Roles Console (also known as the MMC Interface), Web Interface, ADSI Provider or Management Shell, and the Active Roles Administration Service.
To access the Active Roles Administration Service with the Active Roles client components through a firewall, you must open port 15172 and all high ports (1024-65535) on port 15172 in the firewall. The client machines randomly select high ports to use for outgoing traffic on port 15172 to access the Active Roles Administration Service.
To give access to the Active Roles Administration Service through a firewall
-
In the firewall, open port 15172 TCP Inbound/Outbound.
NOTE: For more information about opening ports in your firewall, refer to the operating system's or the network device vendor's documentation.
-
In the firewall, open the high ports (port range 1024-65535) on port 15172.
NOTE: To check the list of high ports being used on port 15172, in the Active Roles Console of a client machine, use the netstat -an command.
Access to Active Roles Web Interface
To access the Active Roles Web Interface through a firewall, open the following ports:
The Web Interface normally runs over port 80, or over port 443 if SSL is enabled (off by default).
Active Roles and supported Azure environments
Active Roles and supported Azure environments
Active Roles supports 3 different Azure environment configurations: Non-federated, Synchronized Identity, and Federated.
Non-federated
In a non-federated environment, the on-premises domains are not registered in Azure AD, and neither Azure AD Connect nor any third-party synchronization tools are configured in the domain for synchronization. In non-federated environments, the changes made in Active Roles are immediately replicated to Azure or Microsoft 365 using Graph API calls or cmdlet calls. Azure users or guest users are typically created with the onmicrosoft.com UPN suffix.
Example: Non-federated environment configuration
A non-federated environment may have the following settings:
-
On-premises domain: test.local
-
Azure AD Domain: ARSAzure.onmicrosoft.com
-
Azure AD Connect is not configured for synchronization.
The on-premises domain is not registered in Azure. The Azure user is created in Active Roles with the ID of user001@test.local and in Azure as user001@ARSAzure.onmicrosoft.com. The user is created in Azure simultaneously when it is created in Active Roles using a Graph API call.
NOTE: One Identity recommends using Non-federated environments for testing purposes only, and does not recommend setting them up as a live production environment.
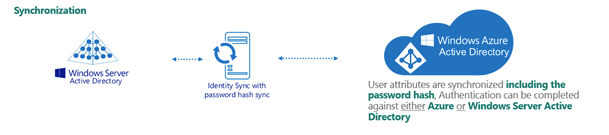
Synchronized identity
In a Synchronized identity environment, the on-premises domain is optionally registered in Azure AD, while Azure AD Connect is configured to synchronize the local AD objects to Azure. Azure users or guest users are typically created either with the selected on-premises domain or with the onmicrosoft.com UPN suffix.
Figure 171: Synchronized identity configuration
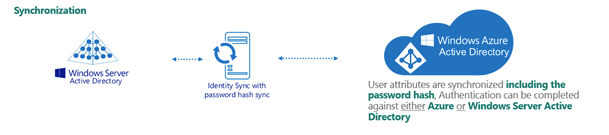
Example: Synchronized identity configuration
A synchronized identity environment may have the following settings:
-
On-premises domain: test.local
-
Azure AD Domain: rd4.qsftdemo.com
-
Azure AD Connect is configured for synchronization.
The on-premises domain is optionally registered in Azure. The Azure user is created in Active Roles with the ID of user001@test.local and in Azure as user001@rd4.qsftdemo.com.
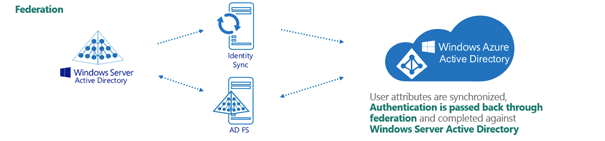
Federated
In a federated environment, the on-premises domain is always registered in Azure AD, while Azure AD Connect and Active Directory Federation Services (ADFS) are configured to facilitate synchronization. Azure users and guest users are typically created with the onmicrosoft.com UPN suffix of the selected on-premises domain.
Figure 172: Federated configuration
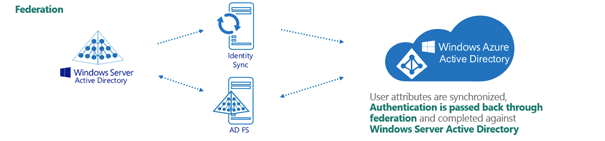
Example: Federated configuration
A federated configuration may have the following settings:
-
On-premises domain: rd4.qsftdemo.com
-
Azure AD Domain: rd4.qsftdemo.com
-
Azure AD Connect and ADFS are configured for synchronization.
The on-premises domain is registered and verified in Azure. The Azure user is created in Active Roles and Azure AD with the same ID of user001@rd4.qsftdemo.com.
Azure object management supported in various Azure environments
This section provides information about the supported Azure object operations and methods in various Azure environments using the Active Roles Web Interface. Active Roles supports Non-federated, Federated and Synchronized Identity environments.
You can select the Azure environment configuration type in the Active Roles Configuration Center when creating the Azure tenant, as described in Configuring a new Azure tenant and consenting Active Roles as an Azure application. You can modify the configuration type later by changing the Azure properties of the tenant.
Active Roles identifies the environment based on the Azure tenant type and applies the changes accordingly.