Step 2: Applying the Policy Object
Step 2: Applying the Policy Object
You can apply the Policy Object by using the Enforce Policy page in the New Deprovisioning Policy Object wizard, or you can complete the wizard and then use the Enforce Policy command on the domain, OU, or Managed Unit where you want to apply the policy.
For more information on how to apply a Policy Object, see Applying Policy Objects and Managing policy scope earlier in this chapter.
Scenario 2: Managed Unit for deprovisioned groups
This scenario describes how to configure a Managed Unit and a Group Object Deprovisioning policy so that the Managed Unit includes all deprovisioned groups. The policy sets the Notes property to Deprovisioned upon the deprovisioning of a group, whereas the Managed Unit is configured to include the groups that have the Notes property set to Deprovisioned.
To implement this scenario, you must perform the following actions:
- Create and configure the Managed Unit.
- Configure the Policy Object that defines the appropriate policy.
- Apply the Policy Object to a domain, OU, or Managed Unit.
As a result, after deprovisioning a group in the container you selected in Step 3, Active Roles automatically adds that group to the Managed Unit you created in Step 1.
The following sections elaborate on the steps to implement this scenario.
Step 1: Creating and configuring the Managed Unit
You can create and configure the Managed Unit by using the Active Roles console:
- In the console tree, under Configuration, right-click Managed Units, and select New | Managed Unit.
- In Name, type a name for the Managed Unit. For example, you might type Deprovisioned Users.
- Click Next.
- Configure the membership rule to have the Managed Unit include the deprovisioned user accounts from all domains that are registered with Active Roles (managed domains):
- On the wizard page, click Add.
- In the Membership Rule Type dialog box, click Include by Query, and then click OK.
- Use the Create Membership Rule window to set up the rule:
- In Find, click Users.
- Click Browse and select Active Directory.
- Click the Advanced tab.
- Click the Field button, and then click Notes.
- In Condition, click Is (exactly).
- In Value, type Deprovisioned.
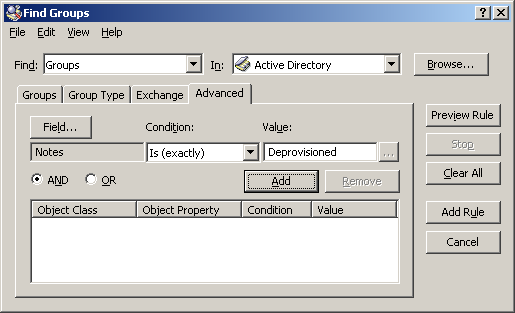
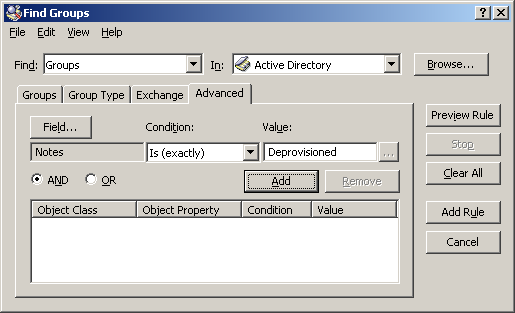
At this stage, the window should look like the following figure.
Figure 87: Find Groups
- Click the Add button.
- Click the Add Rule button.
- On the wizard page, click Add.
- In the Membership Rule Type dialog box, click Retain Deprovisioned, and then click OK.
- Click Next, click Next, and then click Finish.
Step 2: Configuring the Policy Object
You can configure the Policy Object you need by modifying the Policy Object that implements the previous scenario, see Scenario 1: Disabling and renaming the user account upon deprovisioning earlier in this section.
Display the Properties dialog box for that Policy Object and go to the Policies tab. Then, select the policy from the list, and click View/Edit to display the Group Object Deprovisioning Policy Properties dialog box. Click the Change Properties tab.
The Change Properties tab looks similar to the page of the same name in the wizard you used to create the Policy Object. You can use that tab to add the update rule for the Notes property:
- Click Add to display the Select Object Property dialog box.
- Select the check box next to the Notes property, and then click OK.
- In the Add Value dialog box, type Deprovisioned in the ‘Notes’ must be box, and then click OK.
Click OK to close the Group Object Deprovisioning Policy Properties dialog box.