Inband destination selection in Telnet connections
When using inband destination selection in Telnet connections, the user can provide the server address and the username using the following methods:
-
By setting the TELNET ENVIRON option using the SERVER environment variable in the server:port format.
-
By setting the TELNET ENVIRON option using the USER environment variable in the user@server:port format.
-
If neither the SERVER nor the USER environment variable, One Identity Safeguard for Privileged Sessions (SPS) displays a terminal prompt where the user can enter the username and the server address.
Limitations of using TN5250 protocol with IBM iSeries Access for Windows
Using the TN5250 protocol with IBM iSeries Access for Windows is not supported in non-transparent mode if the client tries to set up all its connections using One Identity Safeguard for Privileged Sessions's (SPS's) IP addresses (for example, when both the client and SPS are within the same zone and the firewall is behind SPS). This is problematic in the case of an IBM iSeries Access for Windows client, which initiates administrative communication with components other than the Telnet server itself. Bypassing non-audited traffic goes against the purpose of non-transparent mode.
Possible workarounds:
-
Use a local service file instead of active client-server communication.
-
Use transparent mode.
-
Use single-interface transparent mode and policy-based routing.
VMware Horizon View connections
The following sections describe how to use One Identity Safeguard for Privileged Sessions (SPS) to control and audit VMware Horizon View (formerly known as VMware View) connections. When using SPS to control and audit VMware Horizon View connections, the following requirements and restrictions apply:
-
Only connections using the Remote Desktop (RDP) display protocol are supported. Connections using the PCoIP or HP Remote Graphics Software display protocols are not supported.
-
Both direct connections and tunnel connections are supported.
-
The VMware Horizon View connections must pass SPS directly. It is best if SPS is deployed directly before the Virtual Desktops accessed with VMware Horizon View, and connections are configured in transparent mode.
Deploying SPS that way has the advantage of auditing connections even if the clients access the Virtual Desktops directly, without using a View Connection Server.
NOTE: Using non-transparent mode is also possible if the VMware Horizon View traffic is routed to SPS with an external device (for example, a firewall).
SPS treats VMware Horizon View connections that satisfy these criteria as common RDP connections. All the features of SPS that are available for RDP connections can be used with VMware Horizon View connections as well, for example, four-eyes authorization, auditing and replaying, indexing the recorded audit trails, and so on. For details on RPD-specific settings, see RDP-specific settings.
One Identity Safeguard for Privileged Sessions (SPS) deployment scenarios in a VMware environment
One Identity Safeguard for Privileged Sessions (SPS) supports a variety of deployment scenarios, which make it really flexible when it comes to deployment. The following network topologies illustrate typical SPS VMware Horizon View deployment scenarios.
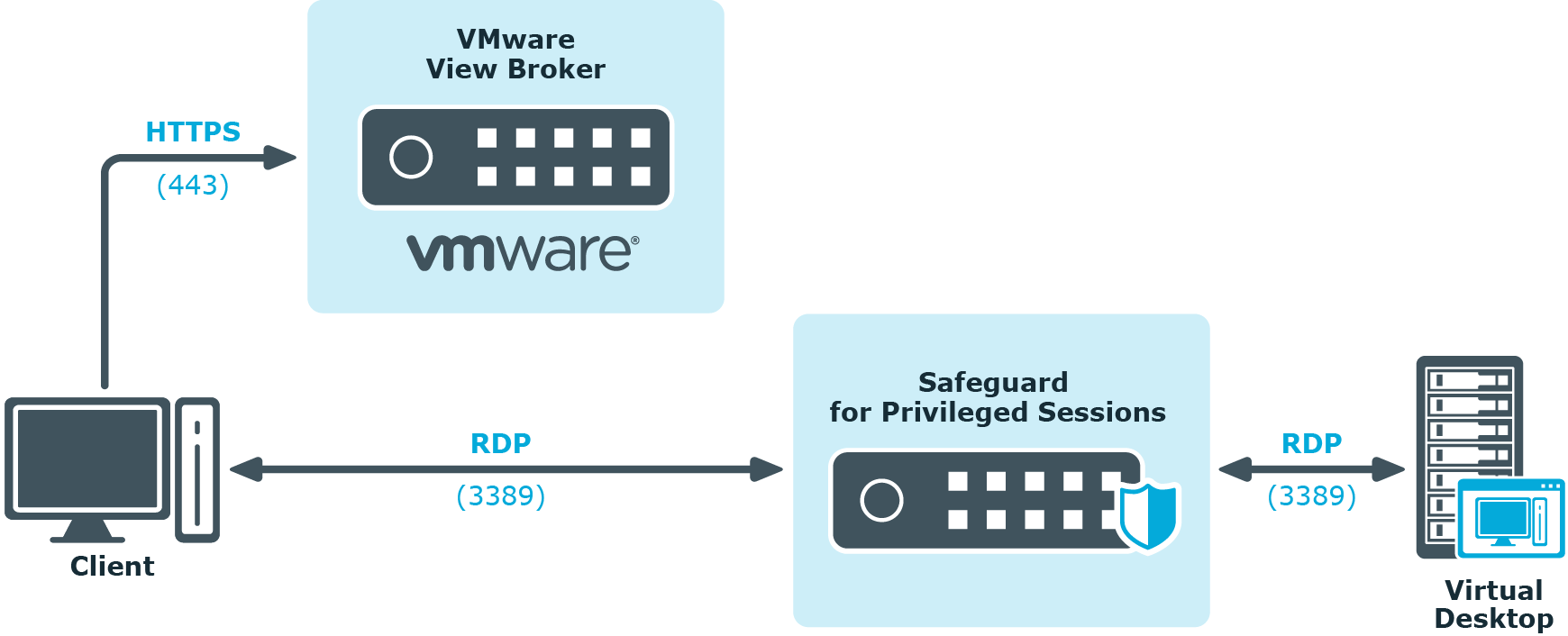
Client - Broker - SPS - Server
SPS is deployed between the Broker and the virtual desktop, where the RDP traffic is embedded into a HTTPS tunnel between the Client and the Broker.
Figure 200: Client - Broker - SPS - Server
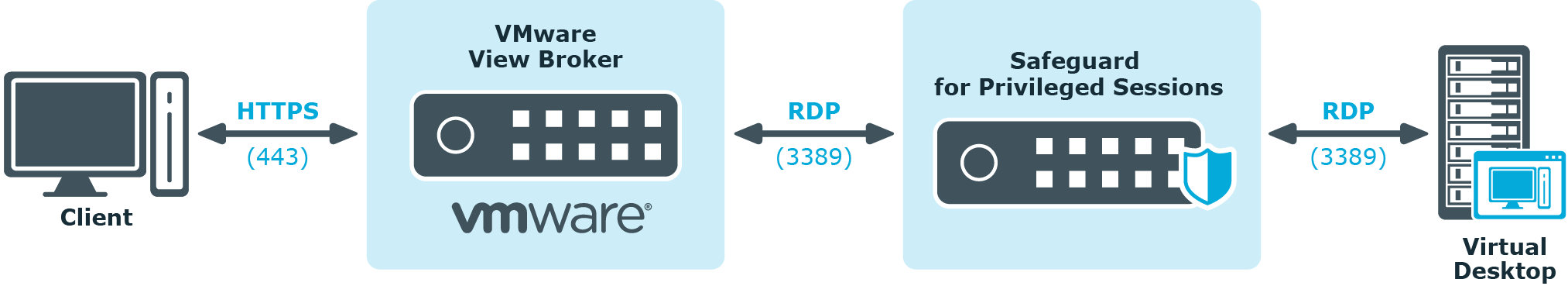
Client - SPS - Server
SPS is deployed between the Client and the virtual desktop, the client makes a direct RDP connection to the Server, without tunneling it through the Broker.
Figure 201: Client - SPS - Server