This section describes the machine account password processes (including the creation of the machine account for SPS), the mandatory password change periods, the password rotation details, the details of the Service Principal Name for SPS and inband target selection.
Machine Account Password Process
When SPS joins a domain, a machine account is created for SPS. By default, Active Directory requires password change for machine accounts every 30 days. Since SPS requires an up-to-date machine account with a current password, SPS forces the machine account password change every 5 days.
If your machine account passwords are rotated more frequently than 5 days, users might experience Kerberos login failures. If your password policy requires more frequent machine account password rotation, contact our Support Team.
Service Principal Name (SPN) for SPS
When a user wants to authenticate with Kerberos, the server has to be addressed with FQDN so the client program can search for the SPN of the server (TERMSRV/target-server.target-realm). Therefore, during the process, SPS domain join registers TERMSRV SPN for its computer account (TERMSRV/<SPS-hostname>.<realm-fqdn>) address.
Make sure that <SPS-hostname>.<realm-fqdn> is resolvable from DNS.
Inband target selection
Since the user has to address the SPS during the Kerberos authentication, the connection policy that uses Kerberos authentication has to use inband target selection so that SPS can forward the incoming service ticket to the required target server.
The available RDP channel types and their functionalities are described below. For details on configuring Channel Policies, see Creating and editing channel policies. For a list of supported client applications, see Supported protocols and client applications.
-
Drawing: Enables access to the server's graphical desktop (screen). This channel must be enabled for RDP to work.
NOTE: In case the Drawing channel is disabled and the load of One Identity Safeguard for Privileged Sessions (SPS) is high, or the connection requires four-eyes authorization and the Authorizer is slow to accept the connection, the client might receive the following error message:
The Remote Desktop Gateway server administrator has ended the connection.
Try reconnecting later or contact your network administrator for assistance
-
Clipboard: Enables access to the server's clipboard: the clipboard of the remote desktop can be pasted into local applications (and vice-versa). Note that SPS can audit the clipboard channel, and that files transferred via the clipboard can be audited Configuring SPS to enable exporting files from audit trails after RDP file transfer through clipboard or disk redirection.
If the Clipboard channel is enabled, it implicitly enables copying files as well, as the user can simply copy-paste the file. Copy-pasted files will not be visible in the logs or the File operations column of the Sessions page. To ensure that SPS records file transfer events, you must disable the Clipboard channel.
-
Redirects: Enables access to every device redirection available in RDP, like file-sharing, printer sharing, device (for example, CD-ROM) sharing, and so on.
-
To make the list of file operations available in the File operations column of the Sessions page, navigate to the Channel Policies page of the protocol, and enable the Log file transfers to database option. This option is disabled by default.
-
To send the file operations into the system log, enable the Log file transfers to syslog option. This option is disabled by default.
NOTE: Turning logging on might result in a slight performance penalty. If traffic load slows processes down, disable the option.
To enable only specific types of redirections, use the following channels:
NOTE: Due to the way RDP handles device redirection, these channels work only if the Sound channel type is also enabled. Make sure that you enable the Sound channel if you enable one of the specific redirection types, for example, Serial, Parallel, Printer,Disk, SCard, or Custom redirect.
-
Serial redirect: Enables access to serial-port redirections.
-
Parallel redirect: Enables access to parallel-port redirections.
-
Printer redirect: Enables access to shared printers.
When enabling printer redirection, you may need to use TSVCTKT and XPSRD channels — these enable XPS printing.
Note that these channels are dynamic virtual channels and you have to be enable them using the Custom channel type.
For more information on TSVCTKT and XPSRD channels, see section 2.1 Transport in Microsoft Technical Document [MS-RDPEXPS].
Before consulting the cited Microsoft Technical Document, it is recommended to start by reading [MS-RDSOD]: Remote Desktop Services Protocols Overview.
-
Disk redirect: Enables access to shared disk drives.
-
To make the list of file operations available in the File operations column of the Sessions page, navigate to the Channel Policies page of the protocol, and enable the Log file transfers to database option. This option is disabled by default.
-
To send the file operations into the system log, enable the Log file transfers to syslog option. This option is disabled by default.
NOTE: Turning logging on might result in a slight performance penalty. If traffic load slows processes down, disable the option.
If the Clipboard channel is enabled, it implicitly enables copying files as well, as the user can simply copy-paste the file. Copy-pasted files will not be visible in the logs or the File operations column of the Sessions page. To ensure that SPS records file transfer events, you must disable the Clipboard channel.
-
SCard redirect: Enables access to shared SCard devices.
To permit only specific redirections, enter the unique name of the redirection into the Details field. For example, if you want to enable access only to the shared disk drive C:, enable the Disk redirect channel and enter C: into the Permitted devices field. Note that the name of the device comes from the device itself, so it is case sensitive, and may not always be reliable from a security point of view.
-
Sound: Enables access to the sound that is played on the server.
NOTE: Due to the way RDP handles device redirection, these channels work only if the Sound channel type is also enabled. Make sure that you enable the Sound channel if you enable one of the specific redirection types, for example, Serial, Parallel, Printer,Disk, SCard, or Custom redirect.
To enable auditing the sound that is transferred between an RDP client and the server, make sure that the Record audit trail checkbox is selected for the Sound and the Dynamic virtual channel.
NOTE: If the Record audit trail checkbox is selected only for the Sound channel, only the output sound (the one that is received by the audited user) is recorded in the audit trail.
If the Record audit trail checkbox is selected for the Dynamic virtual channel, both the input sound (the one that comes from the audited user) and output sound (the one that is received by the audited user) are recorded.
-
Custom: Applications can open custom channels to the clients connecting remotely to the server. Enabling the Custom channel allows the clients to access all of these custom channels. To permit only specific channels, enter the unique names of the channel into the Permitted devices field.
For example, to monitor RemoteApp connections, you need to configure custom channels. For more information, see Configuring RemoteApps.
-
Seamless: Enables seamless channels that run a single application on the RDP server, instead of accessing the entire desktop.
-
Dynamic virtual channel: Enables the server to open channels back to the client dynamically. To restrict which dynamic channels are permitted, select Channel details, click  and enter the name of the permitted channel.
and enter the name of the permitted channel.
Additionally, you may need to use one or more of the following:
Before consulting any of the listed Microsoft Technical Documents, it is recommended to start by reading [MS-RDSOD]: Remote Desktop Services Protocols Overview.
To enable auditing the sound that is transferred between an RDP client and the server, make sure that the Record audit trail checkbox is selected for the Sound and the Dynamic virtual channel.
NOTE: If the Record audit trail checkbox is selected only for the Sound channel, only the output sound (the one that is received by the audited user) is recorded in the audit trail.
If the Record audit trail checkbox is selected for the Dynamic virtual channel, both the input sound (the one that comes from the audited user) and output sound (the one that is received by the audited user) are recorded.
NOTE: When the channel opens, there are certain cases when the remote group is not known yet. For example, in case of an RDP or ICA login screen, the drawing channel has to be opened first to properly display the logon screen. Only those channel rules will apply, where the Remote group field is empty. In case of network level authentication, all required information is present already so this limitation does not apply.
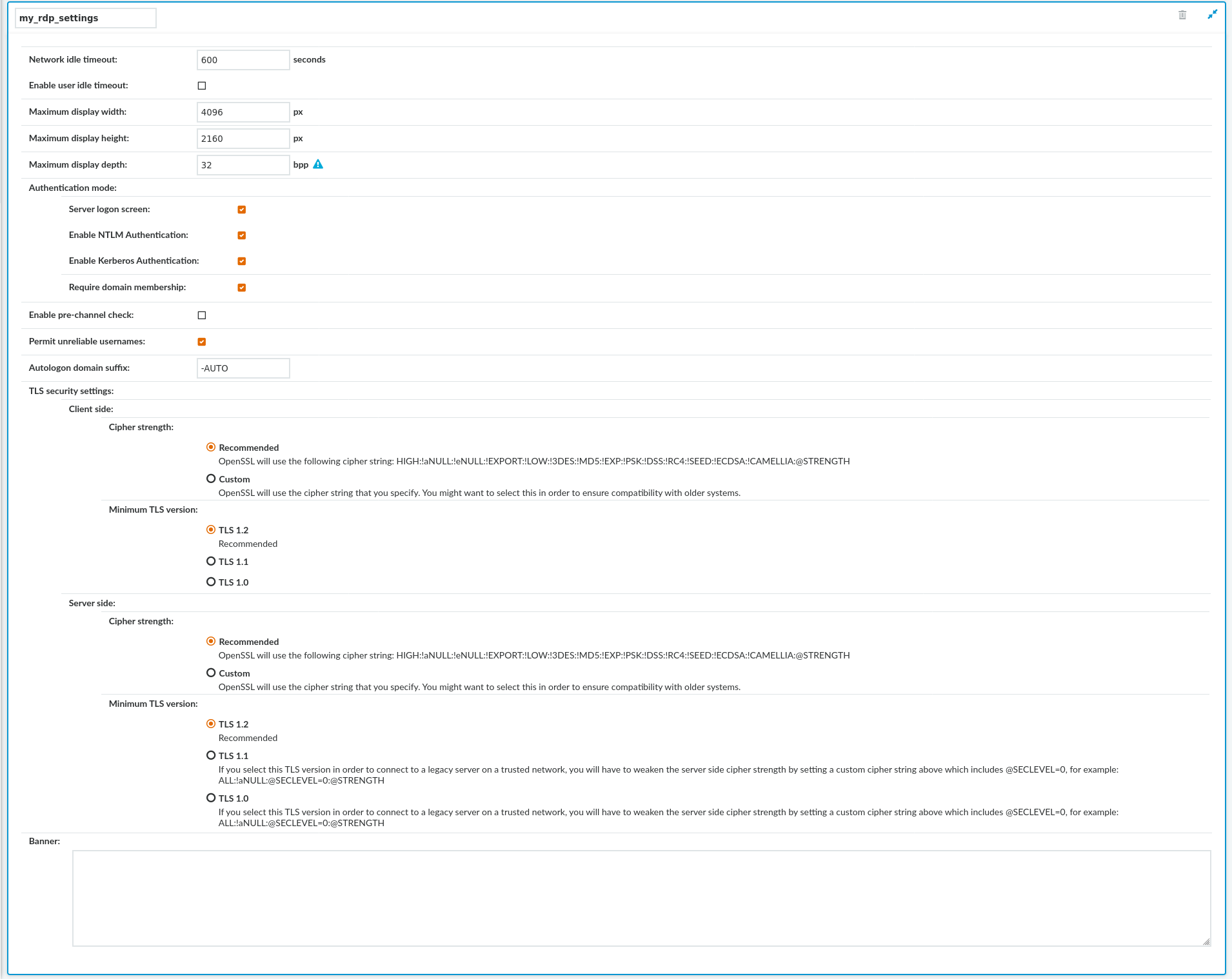
RDP settings determine the parameters of the connection on the protocol level. For example, timeout value, the supported authentication modes, and display parameters.
Figure 204: Traffic Controls > RDP > Settings — RDP settings
|

|
Caution:
Modifying the RDP settings is recommended only to advanced users. Do not modify these settings unless you exactly know what you are doing. |
To create a new RDP settings profile or edit an existing one
-
Navigate to Traffic Controls > RDP > Settings and click  to create an RDP setting profile. Enter a name for the profile (for example, rdp5only).
to create an RDP setting profile. Enter a name for the profile (for example, rdp5only).
-
Click  to display the parameters of the RDP connection.
to display the parameters of the RDP connection.
-
Modify the parameters as needed. The following parameters are available:
-
Network idle timeout: Connection timeout value in seconds. To avoid early timeout, set it to a larger value, for example a week (604800 seconds).
Even if the user is not active, the session can contain activity that must be audited (for example, the output of a script). The idle timeout period will start only after this activity has stopped.
|

|
Caution:
Determining if a connection is idle is based on the network traffic generated by the connection, not the activity of the user. For example, if an application or the taskbar of a graphical desktop displays the time which is updated every minute, it generates network traffic every minute, negating the effects of timeout values greater than one minute and preventing One Identity Safeguard for Privileged Sessions (SPS) from closing the connection. |
|

|
Caution:
If the value is set below 31 seconds, MSTSC can fail and prevent new connections if Act as a Remote Desktop Gateway is enabled in Traffic Controls > RDP > Connections. To prevent this, set the Idle timeout value to at least 31 seconds. |
-
User idle timeout: If no user activity is detected, terminate the session after the configured time has passed since the last user activity.
This can be useful if only user-generated network traffic is important in a session. By using this option, situations described in the caution of Network idle timeout (such as a taskbar clock keeping the network traffic open indefinitely) can be avoided. To enable user idle timeout, select Enable user idle timeout and enter a value that is greater than or equal to the value of Network idle timeout.
-
Maximum display width: The maximum allowed width of the remote desktop in pixels (for example 1024).
NOTE: The Maximum display width and Maximum display height options should be high enough to cover the combined resolution of the client monitor setup. Connections that exceed these limits will automatically fail. Make sure to adjust these settings if your clients use multiple monitors. For example, if your clients use two monitors that have a resolution of 1920x1080 pixels each, set Maximum display width to 4000, and Maximum display height to 2200.
-
Maximum display height: The maximum allowed height of the remote desktop in pixels (for example 768).
NOTE: The Maximum display width and Maximum display height options should be high enough to cover the combined resolution of the client monitor setup. Connections that exceed these limits will automatically fail. Make sure to adjust these settings if your clients use multiple monitors. For example, if your clients use two monitors that have a resolution of 1920x1080 pixels each, set Maximum display width to 4000, and Maximum display height to 2200.
-
Maximum display depth: The maximum allowed color depth of the remote desktop in bits (for example 24). The following values are valid: 8, 15, 16, 24.
|

|
Caution:
-
Using 32-bit color depth is currently not supported: client connections requesting 32-bit color depth automatically revert to 24-bit.
-
Certain Windows versions do not support 24-bit color depth. In this case, those versions can only be displayed in 16-bit color depth. SPS automatically changes its settings to 16-bit. |
-
Authentication mode: Enable the authentication option that best matches the authentication method supported by your server. The available options are Server logon screen and Enable NTLM Authentication. Network Level Authentication (NLA) is also called Credential Security Service Provider (CredSSP).
By default, both the Server logon screen and the Enable NTLM Authentication options are enabled. If you want to ensure a higher level of security, enable only the Enable NTLM Authentication option. In this case, the connection must use TLS as the transport security. For information on enabling the TLS encryption, see Enabling TLS-encryption for RDP connections.
NOTE: Smartcard authentication cannot be used if Network Level Authentication is negotiated at the beginning of the connection.
-
Server logon screen: Use this option if the RDP server is not NLA-enabled. This option allows you to log in directly to the RDP server through its graphical login screen.
-
Enable NTLM Authentication: Use this option to connect to NLA-enabled RDP servers with RDP 6 or later versions. NTLM is the preferred option and considered more secure than the authentication provided by the Server logon screen option.
-
Enabling Kerberos Authentication: Use this option to connect to RDP servers that support Kerberos authentication. Kerberos is the preferred option and considered more secure than the authentication provided by the Server logon screen option or NTLM.
NOTE: When enabling Kerberos authentication, note that
-
Kerberos authentication can only be used with the Require domain membership sub-option enabled.
-
The AA plugin is not supported with Kerberos authentication.
-
SPS has to forward the incoming service ticket to the required target server. Therefore, the referrer connection policy has to use inband target selection. For more information, see Kerberos.
-
The Act as Remote Desktop Gateway option cannot be selected for the referrer connection policy.
-
Require domain membership: This is a sub-option of the Enable NTLM Authentication option. By default, the Require domain membership option is not enabled. In the default operation, you can use SPS to monitor RDP access to servers that accept only NLA, even if the client, SPS, and the server are not in the same domain. You can also use this option if the RDP server is a standalone server and is not part of a domain, or if, for some reason, you cannot add SPS to the domain.
If you enable the Require domain membership option, you can only authenticate to the RDP server successfully if SPS is a member of the domain to which the RDP server belongs. To configure SPS to join your domain, see Network Level Authentication (NLA) with domain membership.
-
Enable pre-channel check: Select this option to evaluate the connection and channel policies before establishing the server-side connection. That way if the connection is not permitted at all, SPS does not establish the server-side connection.
-
Permit unreliable usernames: SPS automatically terminates RDP connections if it cannot reliably extract the username from the RDP connection. Enable this option to permit connections with unreliable usernames. For details on ensuring that the usernames in RDP connections are reliable, see Usernames in RDP connections.
Known issue
When accessing a Windows Server 2003 R2 host, the Permit unreliable usernames option is disabled, and the username is unreliable, SPS terminates the connection, but only after the user logs in. As a result, the session is not closed on the server-side.
-
Autologon domain suffix: Enter the suffix that the client will append to the domain when using autologon in conjunction with Network Level Authentication (CredSSP).
-
To display a banner message to the clients before authentication, enter the message into the Banner field. For example, this banner can inform the users that the connection is audited. SPS displays this banner in a graphical window that has only an OK button. Note the following points:
-
You can write a plain-text or a basic HTML-formatted banner.
|

|
Caution:
If the banner is overly complex HTML using deeply embedded structures, displaying the banner will fail, causing the RDP connections to time out. |
-
When using HTML markup, the entire banner must be a single HTML object (for example, a div).
<div align="center"><b>Your session is recorded using Privileged Session Monitoring</b></div>
-
In HTML, you can embed images (for example, a company logo) as data URLs in an img tag:
To include a logo or other image, use a base64-encoded data url within an, like this: <img alt="Embedded Image" src="data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAADIA..." />.
-
Note that while you can include links in the text, your users cannot click or copy them.
-
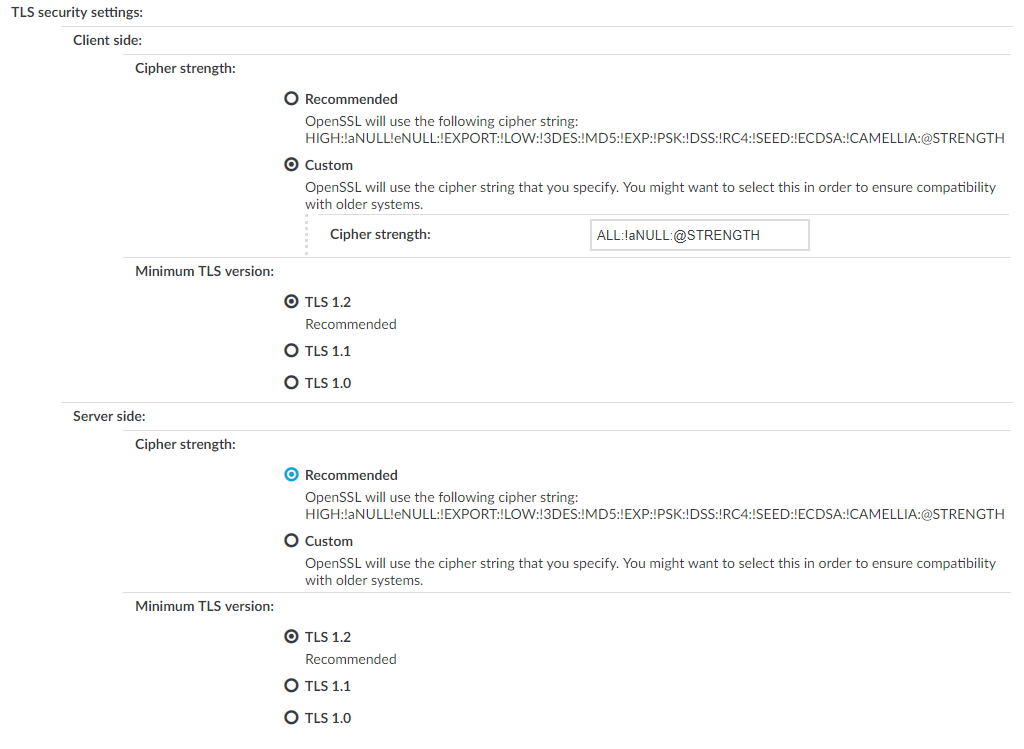
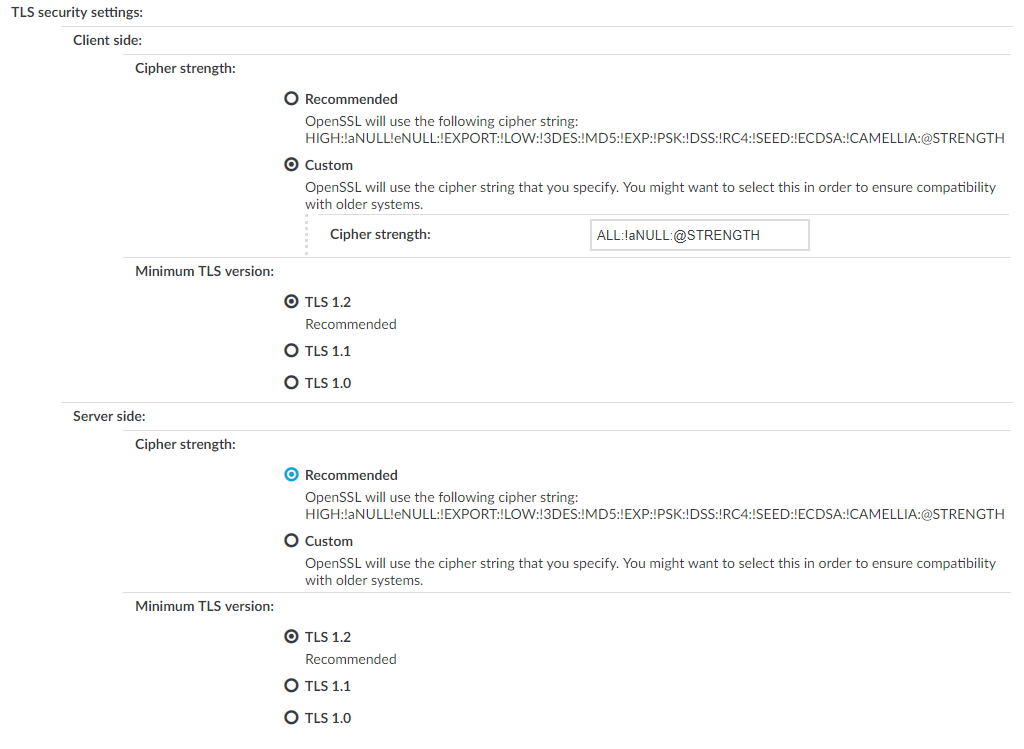
To configure TLS security settings on both the Client side and the Server side, proceed to TLS security settings.
Figure 205: <Protocol> Control > Settings > TLS security settings - configuring TLS security settings
-
Cipher strength specifies the cipher string OpenSSL will use. The following options are possible:
-
Recommended: this setting only uses ciphers with adequate security level.
-
Custom: this setting allows you to specify the list of ciphers you want to permit SPS to use in the connection. This setting is only recommended to ensure compatibility with older systems. For more details on customizing this list, check the 'openssl-ciphers' manual page on your SPS appliance.
For example: ALL:!aNULL:@STRENGTH
-
Minimum TLS version specifies the minimal TLS version SPS will offer during negotiation. The following options are possible:
-
TLS 1.2: this setting only offers TLS version 1.2 during the negotiation. This is the recommended setting.
-
TLS 1.1: this setting offers TLS version 1.1 and later versions during the negotiation.
-
TLS 1.0: this setting offers TLS version 1.0 and later versions during the negotiation.
NOTE: Setting up sessions to legacy systems that do not support at least TLS 1.2 is only possible when the security level of the connection is degraded to 0, which is possible by specifying the TLS ciphers manually and appending the string `:@SECLEVEL=0` to the cipher list. However, this setting also enables the use of known vulnerable algorithms and key sizes, therefore it is absolutely critical to only use such connection settings when it is necessary and when you can fully trust your network between SPS and the legacy system. It is strongly recommended to use different security settings on the server and the client side of the connection, when degrading the security level of a connection is unavoidable.
NOTE: Note that SPS only permits TLS-encrypted connections. SSLv3 is not supported.
-
Click Commit.
-
Select this settings profile in the RDP settings field of your connections.

 and enter the name of the permitted channel.
and enter the name of the permitted channel.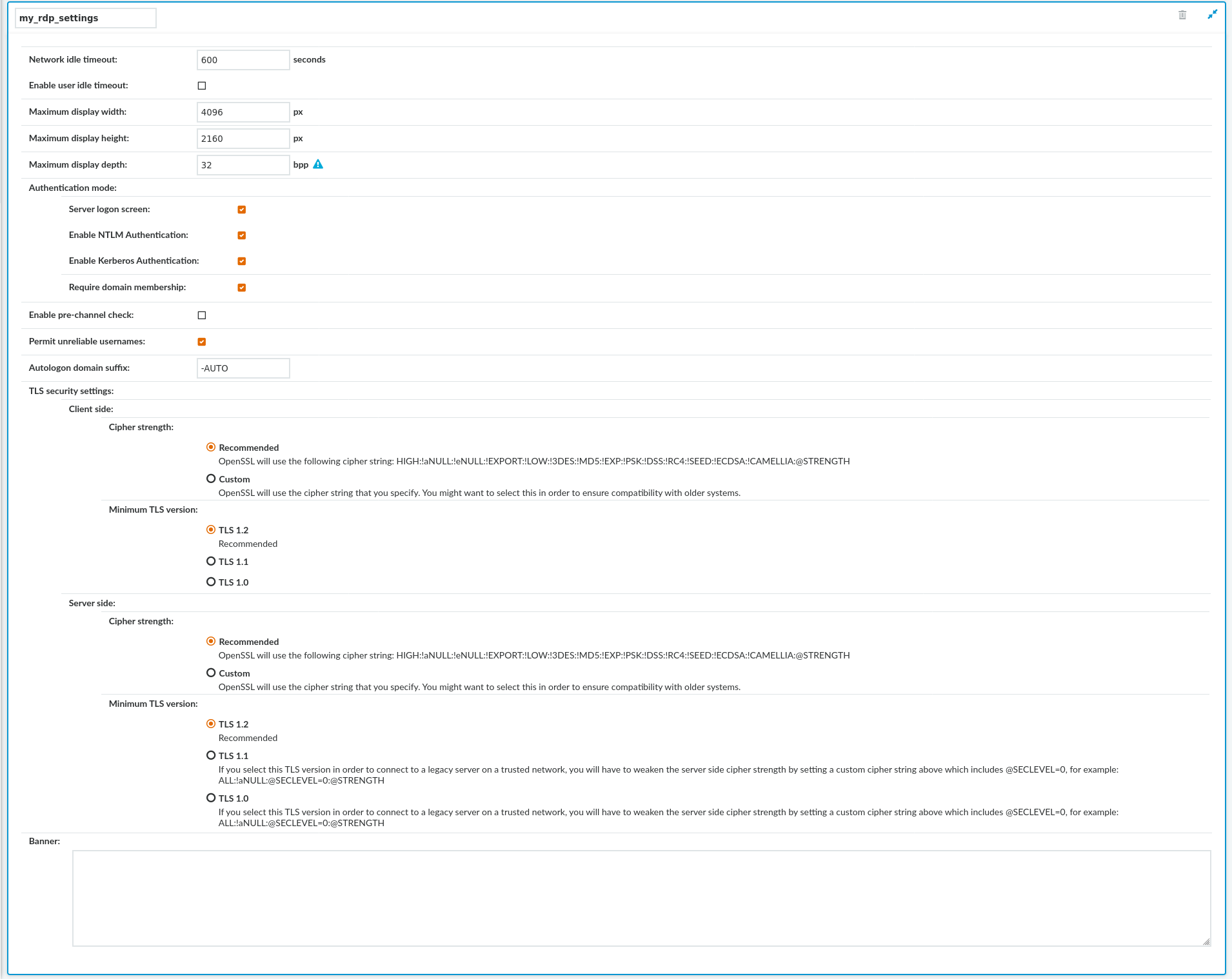

 to display the parameters of the RDP connection.
to display the parameters of the RDP connection.