The Basic Settings > System > License page displays the following information of the current license:
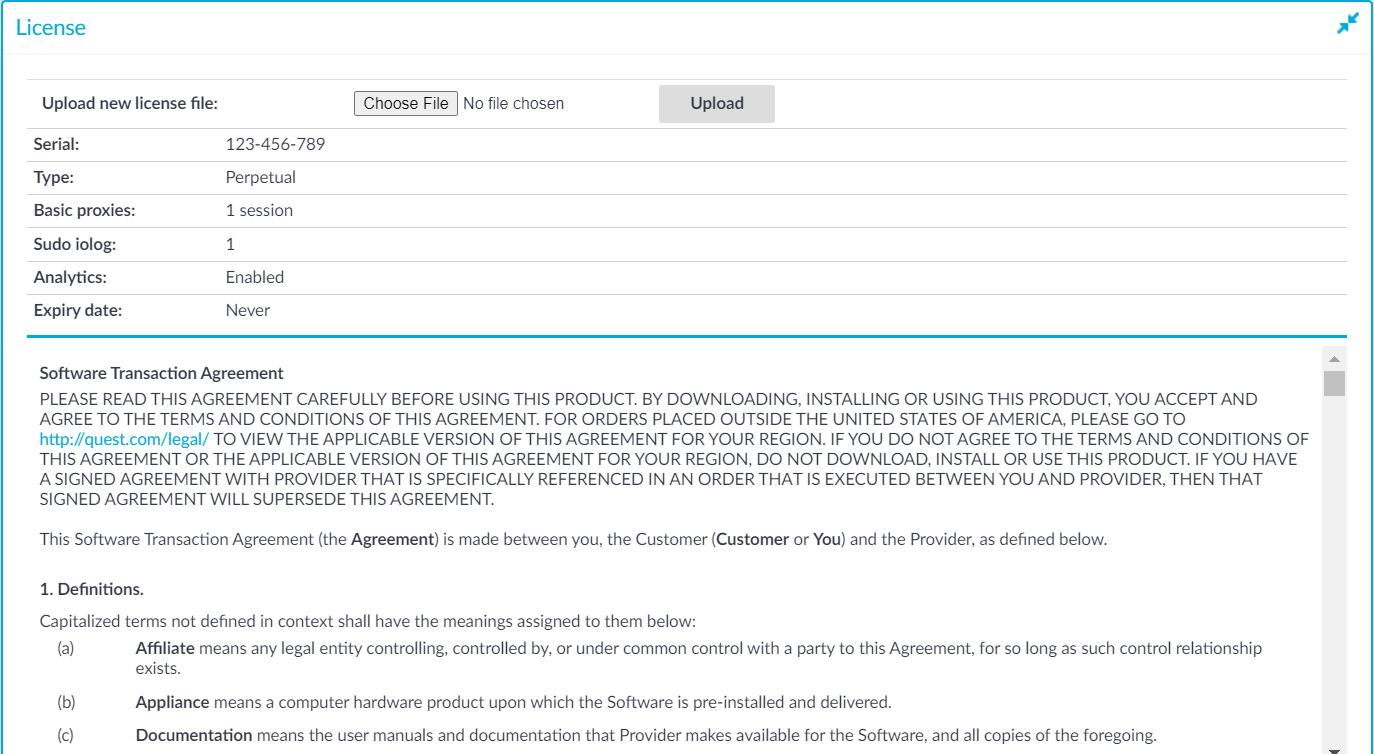
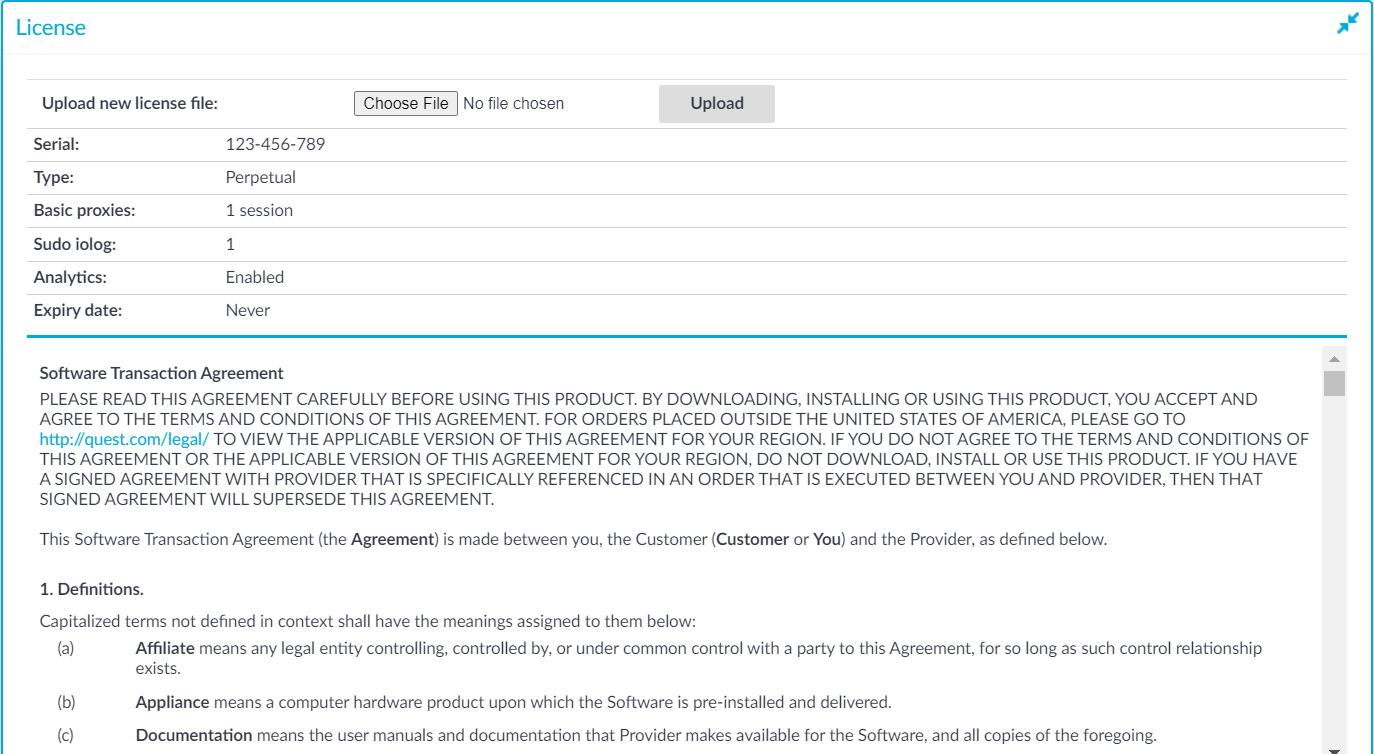
Figure 139: Basic Settings > System > License — Updating the license
-
Serial: The unique serial number of the license.
-
Type: The license type, for example: Perpetual.
-
Basic proxies: The actual value of the sessions or hosts. You can select the following sub-options:
-
Host: Limits the number of servers (individual IP addresses) that can be connected through SPS.
-
Session: Limits the number of concurrent sessions (parallel connections) that can pass through SPS at a time (for example 25).
-
Sudo iolog: Number of enabled Sudo iolog connections.
For more information, see Using Sudo with SPS.
-
Analytics: Enables the Analytics option.
For more information, see Analyzing data using One Identity Safeguard for Privileged Analytics.
-
Expiry Date: The license expiration date. The date is displayed in YYYY-MM-DD format.
SPS starts sending automatic alerts daily, 60 days before the license expires.
One Identity recommends that you update the SPS license before the existing license expires or when you purchase a new license.
|

|
Caution:
After upgrading to version 7.0 LTS, SPS requires a new license. To avoid possible downtimes due to certain features not being available, before starting the upgrade, ensure that you have a valid SPS license for 7.0 LTS.
Upgrade as follows:
-
Perform the upgrade to 7.0 LTS with your current license.
-
Update your SPS license to 7.0 LTS.
For a new SPS license for 7.0 LTS, contact our Licensing Team. |
To update the license
-
Navigate to Basic Settings > System > License.
-
Click Browse and select the new license file.
-
Click Upload, then Commit.
Connecting to One Identity Safeguard for Privileged Sessions (SPS) locally or remotely using Secure Shell (SSH) allows you to access the console menu of SPS. The console menu provides access to the most basic configuration and management settings of SPS. It is mainly used for troubleshooting purposes, the primary interface of SPS is the web interface.
The console menu is accessible to the root user using the password set during completing the Welcome Wizard.
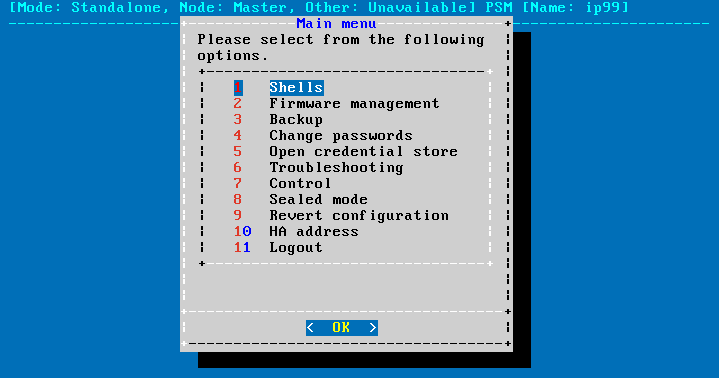
Figure 140: The console menu
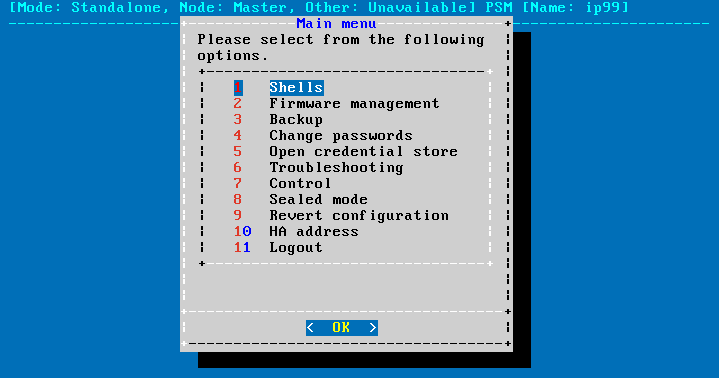
The console menu provides allows you to perform the following actions.
Access the local core and boot shells.
This is usually not recommended and only required in certain troubleshooting situations. Select the boot/core shell's keyboard layout for the local console. This will not affect the keyboard layout if you have accessed the shell via SSH.
The boot firmware boots up SPS, provides High Availability support, and starts the core firmware. The core firmware, in turn, handles everything else: provides the web interface, manages the connections, and so on.
Select the active firmware, and delete unneeded firmwares.
Accessing the firmware management is useful if after an update the new firmware does not operate properly and the web interface is not available to activate the previous firmware.
Start backup processes.
For more information about backup processes, see Data and configuration backups.
Change the passwords of the root and admin users.
For details, see Changing the root password of One Identity Safeguard for Privileged Sessions (SPS).
Access the network-troubleshooting functions and display the available log files.
If the web interface is inaccessible, it can be the result of an internal locking error. To resolve this issue, delete the lock files. After deletion, they are archived, and included in the support bundle if they are not older than 30 days. To create a support bundle, if the web interface is inaccessible, select Create support bundle.
Reboot and shutdown the system.
For details, see Controlling One Identity Safeguard for Privileged Sessions (SPS): reboot, shutdown.
Enable and disable sealed mode.
For details, see Sealed mode.
Set the IP address of the HA interface.
For more information about assigning an IP address to the HA interface of a node, see Resolving an IP conflict between cluster nodes.
NOTE: Note that logging in to the console menu automatically locks the SPS interface, meaning that users cannot access the web interface while the console menu is used. The console menu can be accessed only if there are no users accessing the web interface. The connection of web-interface users can be terminated to force access to the console menu.