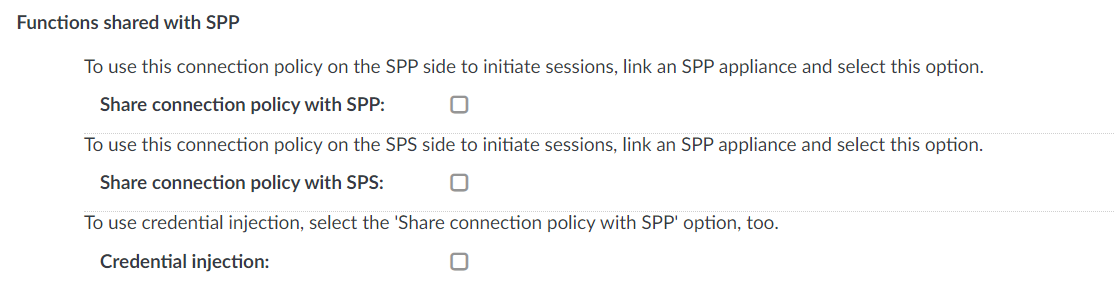
If you have linked an SPP appliance to SPS and want to share specific functions with SPP, use the Functions shared with SPP option. This option lists the shared SPS functions that you can use in SPP without further configuration.
The following example displays the available shared functions under the SSH Control option.
Figure 197: RDP Control > Connections — Functions shared with SPP
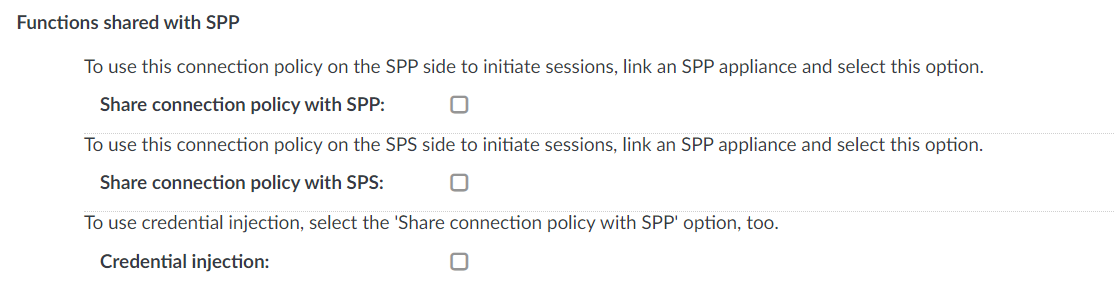
Share connection policy with SPP
The Share connection policy with SPP option is supported currently with SSH and RDP connections. To make a specific SSH or RDP connection policy available in SPP to initiate sessions, select Share connection policy with SPP and set the configuration specified in the respective section:
Share connection policy with SPS
The Share connection policy with SPS option is supported currently with SSH and RDP connections. If you have joined an SPP to SPS, you can use the Share connection policy with SPS option.
To initiate sessions from SPS without using SPP directly, but using the credentials provided by and stored in SPP, select the Share connection policy with SPS option.
Set the configuration specified in the respective section:
Credential injection
The RDP Application session initiated on the SPP side provides the password automatically for the RemoteApp Launcher. To use credential injection, use a connection policy for the RDP Application session that has Credential injection selected.
NOTE: To use the credential injection function, you must select the Share connection policy with SPP option as well.
For more information, see Using credential injection in SPP-initiated RDP sessions.
HTTP request-response pairs do not form a well-defined, continuous connection. SPS will group request to the same session if the following points are true:
-
The IP address of the client is the same.
-
The hostname of the target server (not the IP address) is the same.
-
The username is the same (if the user has performed inband authentication).
-
The time elapsed since the last request-response pair between the same client and server is less then the session timeout value.
The following sections describe configuration settings available only for the HTTP protocol.
Use the following policies to control who, when, and how can access the HTTP connection. For details on configuring Channel Policies, see Creating and editing channel policies. For a list of supported client applications, see Supported protocols and client applications.
Auditing HTTP and HTTPS connections is possible in both transparent and non-transparent modes. SPS can also be used as an HTTP/HTTPS proxy to simplify client configuration and integration into your network environment, or it can forward HTTP traffic, behaving as a HTTP tunnel.
-
Channel Policy: The channel policy determines which HTTP channels can be used in the connection, and whether they are audited or not. The different channels may be available only under certain restrictions, as set in the channel policy. For details on configuring these options, see Creating and editing channel policies.
-
HTTP connections: For details, see Setting up HTTP connections.
-
HTTP sessions: HTTP settings determine the parameters of the connection on the protocol level, including timeout value, and so on. For details, see Session-handling in HTTP.
-
HTTP settings: HTTP settings determine the parameters of the connection on the protocol level, including timeout value, and so on. For details, see Creating and editing protocol-level HTTP settings.
For more information, see the latest One Identity Safeguard for Privileged Sessions Administration Guide.
The available HTTP channel types and their functionalities are described below. For details on configuring Channel Policies, see Creating and editing channel policies. For a list of supported client applications, see Supported protocols and client applications.
-
HTTP: Enables you to use the HTTP protocol. This channel must be enabled for HTTP to work.
The available channel policy options are the following: From, Target, Time policy, Record audit trail, and Remote groups. Note that the Remote groups option is used only if the user performs inband authentication using one of the supported HTTP authentication methods (see Authentication in HTTP and HTTPS). To retrieve the groups of an authenticated user from an LDAP database, you must also set an LDAP Server in the Connection Policy (for HTTP/HTTPS connections, One Identity Safeguard for Privileged Sessions (SPS) uses this server only to retrieve the group membership of authenticated users, you cannot authenticate the users to LDAP from SPS). For details on configuring these options, see Creating and editing channel policies.
When setting Target, note the following:
-
If the connection uses DNAT (NAT destination address), the target address of the original client will be compared to the Target parameter of the Channel policy, that is not necessarily equivalent with the server's address.
-
If the connection is redirected to a Fix address, the redirected address will be compared to the Target parameter of the Channel policy.
-
WebSocket: Enables all WebSocket traffic. If the WebSocket channel type is not allowed, HTTP requests trying the WebSocket upgrade are rejected.
WebSocket/VNC audit trails: You can replay audit trails of a WebSocket connection in your browser or using the Safeguard Desktop Player application only if it contains Virtual Network Computing (VNC) traffic. For all other WebSocket connections, export the audit trail as a PCAP file and replay it using the Safeguard Desktop Player application.
When configuring HTTP or SSH connections, avoid using the IP address configured for administrator or user login on SPS.
The current version of SPS does not support the following features that are available for other protocols:
Forwarding HTTP connections to an HTTP proxy is not supported. If your clients use an HTTP proxy to access the target servers, place SPS behind the proxy: Clients - HTTP Proxy - SPS.
|

|
Caution:
The Clients - SPS - HTTP Proxy scenario is not supported. |