Deprovisioning Policy Objects allows configuration and application of the following policies.
Table 3: Deprovisioning Policy Objects
|
User Account Deprovisioning |
When deprovisioning a user, this policy modifies the user account so that the user cannot log on. You can configure this policy to:
-
Disable the user account.
-
Set the user’s password to a random value.
-
Set the user’s logon names to random values.
-
Rename the user account.
You can also select account properties and configure this policy to update them when processing a deprovisioning request. |
|
Group Membership Removal |
When deprovisioning a user, this policy removes the user account from groups. You can configure this policy to remove the account from security groups, mail-enabled groups, or both. In this policy, both distribution groups and mail-enabled security groups are collectively referred to as mail-enabled groups.
You can also select the groups from which you do not want this policy to remove the user account, or configure the policy not to remove the user account from any security groups or mail-enabled groups. |
|
User Account Relocation |
When deprovisioning a user, this policy moves the user account to a different location. You can select the Organizational Unit to which you want the policy to move the account. You can also configure the policy not to move the user accounts upon user deprovisioning. |
|
Exchange Mailbox Deprovisioning |
When deprovisioning a user, this policy makes changes needed to deprovision Microsoft Exchange resources for that user. You can configure this policy to:
-
Hide the mailbox from the global address list (GAL).
-
Prevent non-delivery reports (NDR) from being sent.
-
Grant the user’s manager full access to the user’s mailbox.
-
Grant selected users or groups full access to the user’s mailbox.
-
Disallow forwarding messages to alternate recipients.
-
Forward all incoming messages to the user’s manager. |
|
Home Folder Deprovisioning |
When deprovisioning a user, this policy makes changes needed to prevent the user from accessing his or her home folder. You can configure this policy to:
-
Remove the user’s permissions on the home folder.
-
Grant the user’s manager read-only access to the user’s home folder.
-
Grant selected users or groups read-only access to the user’s home folder.
-
Make a selected user or group the owner of the user’s home folder.
-
Delete the home folder when the user account is deleted. |
|
User Account Permanent Deletion |
When deprovisioning a user, this policy schedules the user account for deletion. You can specify the number of days (retention period) before the account is deleted. Another option is to delete the deprovisioned user accounts immediately to Active Directory Recycle Bin. It is also possible to configure this policy so that the deprovisioned user accounts are not deleted automatically. |
|
Group Object Deprovisioning |
When deprovisioning a group, this policy makes changes to the group object in Active Directory in order to prevent the use of the group. You can configure this policy to:
-
Hide the group from the Global Address List (GAL).
-
Change the group type from Security to Distribution.
-
Rename the group.
-
Remove members from the group.
-
Change or clear any other properties of the group object. |
|
Group Object Relocation |
When deprovisioning a group, this policy moves the group object to a different container in Active Directory. You can select the Organizational Unit to which you want the policy to move the group object. |
|
Group Object Permanent Deletion |
When deprovisioning a group, this policy schedules the group object for deletion in Active Directory. You can specify the number of days (retention period) before the group is deleted. Another option is to delete the deprovisioned groups immediately to Active Directory Recycle Bin. It is also possible to configure this policy so that the deprovisioned groups are not deleted automatically. |
|
Notification Distribution |
In the course of a deprovisioning operation, this policy sends a notification message to the email recipients you specify. You can customize both the message subject and message body. |
|
Report Distribution |
Upon completion of a deprovisioning operation, this policy sends a report to the email recipients you specify. The report includes a list of actions taken during the deprovisioning operation and the details of the deprovisioning activity. You can customize the subject of the email message containing the report.
You can also configure this policy to send the report only if any errors occurred in the course of a deprovisioning operation. |
|
Script Execution |
In the course of a deprovisioning operation, this policy runs the script you specify. By using a script, you can implement custom deprovisioning actions. |
|
Office 365 Licenses Retention |
When deprovisioning an Azure AD user, this policy automates retention of all or selected Microsoft 365 licenses assigned to the Azure AD user after the Azure AD user is deprovisioned successfully. |
A Policy Object is a collection of administrative policies that specifies the business rules to be enforced. A Policy Object includes stored policy procedures and specifications of events that activate each procedure.
A Policy Object associates specific events with its policy procedures, which can be built-in procedures or custom scripts. This provides an easy way to define policy constraints, implement sophisticated validation criteria, synchronize different data sources, and perform a number of administrative tasks as a single batch.
Active Roles enforces business rules by linking Policy Objects to:
-
Administrative views (Active Roles Managed Units)
-
Active Directory containers (Organizational Units)
-
Individual (leaf) directory objects, such as user or group objects
By choosing where to link a Policy Object, you determine the policy scope. For example, if you link a Policy Object to a container, all objects in the container and its sub-containers are normally subject to the Policy Object.
You can link different Policy Objects to different containers to establish container-specific policies. You may need to do so if each Organizational Unit uses a dedicated Exchange Server to store mailboxes or file server to store home folders.
You can also link a Policy Object to a leaf object, such as a user object. As an example, consider a policy that prohibits changes to group memberships when copying a certain user object.
Policy Objects define the behavior of the system when directory objects are created, modified, moved, or deleted within the policy scope. Policies are enforced regardless of administrative rights of a user performing a management task. It is important to understand that even those who have administrator rights to Active Roles itself are forced to abide by administrative policies once they are enforced.
This section guides you through the Active Roles Console to manage Policy Objects.
The Active Roles Console provides separate wizards for creating Policy Objects both for provisioning and deprovisioning.
To create a Policy Object
-
In the Console tree, under Configuration > Policies > Administration, locate and select the folder in which you want to add the Policy Object.
You can create a new folder by right-clicking Administration and selecting New > Container. Similarly, you can create a sub-folder in a folder by right-clicking the folder and selecting New > Container.
-
Right-click the folder, point to New, then click Provisioning Policy or Deprovisioning Policy.
-
On the Welcome page of the wizard, click Next.
-
On the Name and Description page, do the following:
-
In the Name box, enter a name for the Policy Object.
-
(Optional) Under Description, enter any information about the Policy Object.
Click Next.
-
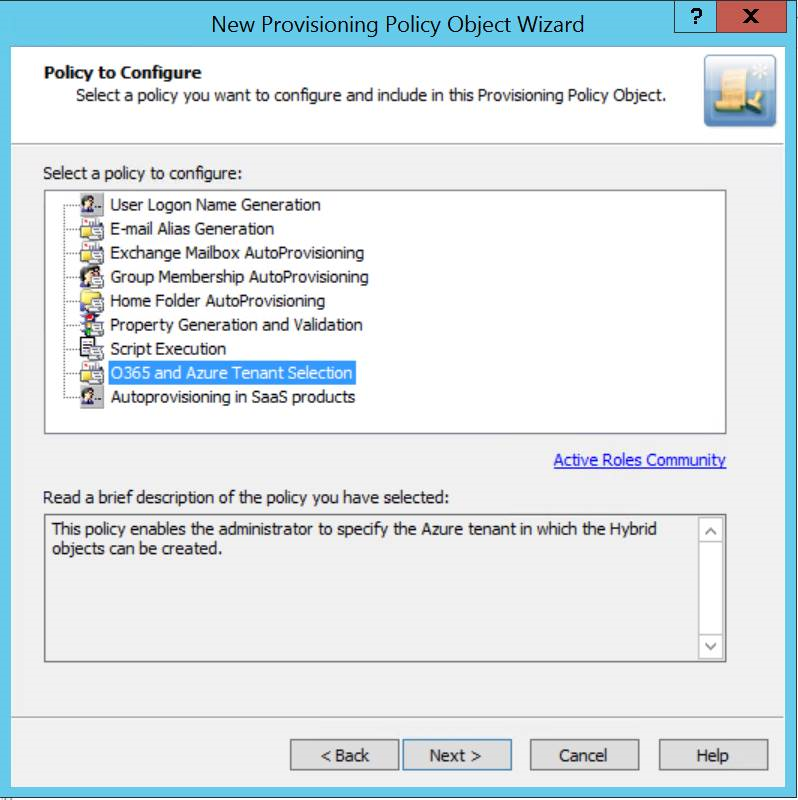
On the Policy to Configure page, select a policy type, and click Next to configure policy settings.
Figure 24: Provisioning policies
-
On the Enforce Policy page, you can specify the objects to which this Policy Object will be applied. To locate and select the objects you want, Click Add and use Select Objects.
-
Click Next, then click Finish.
NOTE: Consider the following when creating Policy Objects: