Active Directory LDAP backend
In addition to the common parameters, the Active Directory (AD) backend has the following additional configurable parameters:
-
membership_check: Enable AD group membership check enables AD specific non-primary group membership checking.Note
The AD user’s primary group is always checked regardless of this setting.
-
nested_groups: Enable nested groups allows AD nested group support. See below for details.
-
Additionally, AD supports case and accent insensitive matching in many of the user and group name attributes. Since One Identity Safeguard for Privileged Sessions (SPS) relies on the server to perform comparisons, case and accent insensitive user and group name support depends solely on the server configuration.
User identification in AD
To determine the user entry for a given plain username, SPS performs a search under user_base_dn for objects having either the sAMAccountName or the userPrincipalName equal to the plain username of the user. The objectClass of the user object is not restricted.
Note
Although userPrincipalName in AD is a Internet-style name like user@example.com, it matches simple names like user.
Only the user object returned here is used for group membership checks.
Group membership resolution in AD
For all group membership checks, only the LDAP user object returned during user identification phase is used.
The plain group name is always compared to the cn attribute of the group object.
A user is treated as a member of a group if both the group object’s objectClass and objectCategory is group, and any of the following is true:
-
The group is the user’s primary group. That is, the objectSID attribute of the group matches the Security Identifier calculated from the user object’s objectSID and primaryGroupID attributes, as described in the Microsoft Support article How to use the PrimaryGroupID attribute to find the primary group for a user.
Note
When using the AD backend, this check is always performed, even if the
membership_checkoption is disabled. However, it is OK for the user to have no primary group. -
The group lists the user’s short username. That is, the group’s memberUid attribute contains the short username from the user object.
This check is performed only when the
membership_checkoption is enabled for AD.Note
For the purpose of this check, the user’s short username is retrieved from the user object’s sAMAccountName attribute only, which is a single-valued attribute in AD. This is a known limitation.
It is OK for the sAMAccountName attribute to be missing, in which case this check will be skipped.
-
The group lists the user’s dn. That is, the group object’s member attribute contains the user’s dn.
This check is performed only when the
membership_checkoption is enabled for AD.This is the only place where nested groups are supported. When the
nested_groupssetting is enabled in the configuration, SPS will also find groups which do not directly contain the user’s dn in their member attribute, but do contain an intermediate group’s dn, which in turn contains the user dn in its member attribute. This nesting can be arbitrarily deep, limited only by AD.Note
Due to the nature of the way AD resolves the nested group chain, intermediate groups might be outside the configured
group_base_dn.
Note
Although an objectCategory in AD is a DN-valued attribute, it does match simple names like group.
Additionally, a user is treated as a member of a group if:
-
The group lists the user’s dn in any of the additional group objects configured in
user_dn_in_groups.For example, if a row is added with
objectClassset to groupOfNames andattributeset to member, SPS will treat the user as a member of all groups where the group is a groupOfNames, and the group’s member attribute contains the user’s dn.Note
There is no additional restriction on the group’s objectClass in this case.
-
The user lists the group’s dn. That is, the user’s
memberof_user_attributecontains the dn of the group, and the objectClass of the referred group is group.This check is performed only when the
memberof_checkoption is enabled for AD.Note
SPS compares the dn stored in the
memberof_user_attributeto the dn of the group object itself in a strict stringwise manner. Therefore, this user attribute must contain the group DN exactly as it would be returned by the LDAP server. No case or accent differences are allowed.
Appendix: Deprecated features
These features have been deprecated and will be removed from the upcoming releases.
Deprecated: Using the Search (classic) interface
Searching audit trails: the One Identity Safeguard for Privileged Sessions (SPS) connection database
Deprecated: Using the Search (classic) interface
IMPORTANT: Support for the Search (classic) interface is deprecated. This feature will be removed from the upcoming releases. One Identity recommends using the supported Search interface instead. For more information, see Using the Search interface.
This section describes how to browse the audit trails stored on One Identity Safeguard for Privileged Sessions (SPS), or archived to a remote server, how to search for a specific audit trail, and also how to replay them from the browser.
-
Searching audit trails: the One Identity Safeguard for Privileged Sessions (SPS) connection database explains how to use and customize the search interface, describes the connection metadata that is available on SPS, and provides examples of wildcards and boolean search operators you can use.
-
Connection details describes how to review the details of a connection, and to replay it online from SPS.
-
Displaying statistics on search results describes how you can create custom statistics from the search results, and how to save them for reports.
Searching audit trails: the One Identity Safeguard for Privileged Sessions (SPS) connection database
One Identity Safeguard for Privileged Sessions (SPS) has a search interface for browsing the audit trails. This connection database also contains the various meta-information about connections and connection-requests. The search queries can include only alphanumerical characters.
To access the search interface, navigate to Search. Only users with the following privileges can access the Search page:
-
Members of groups who are configured as Authorizers with the Search or Search&Authorize permission set in the Access Control field of a connection policy. These users can access only the audit trails of the respective connections.
For more information on configuring authorizers for a connection, see Configuring four-eyes authorization.
-
Members of groups who have the Search privilege set.
Assigning the Search privilege to a user on the AAA page automatically enables the Search in all connections privilege, and grants the user access to every audit trail, even if the user is not a member of the groups listed in the Access Control option of the particular connection policy.
For more information on configuring user rights, see Managing user rights and usergroups.
-
The admin user.
Figure 308: Search — Browse the connections database
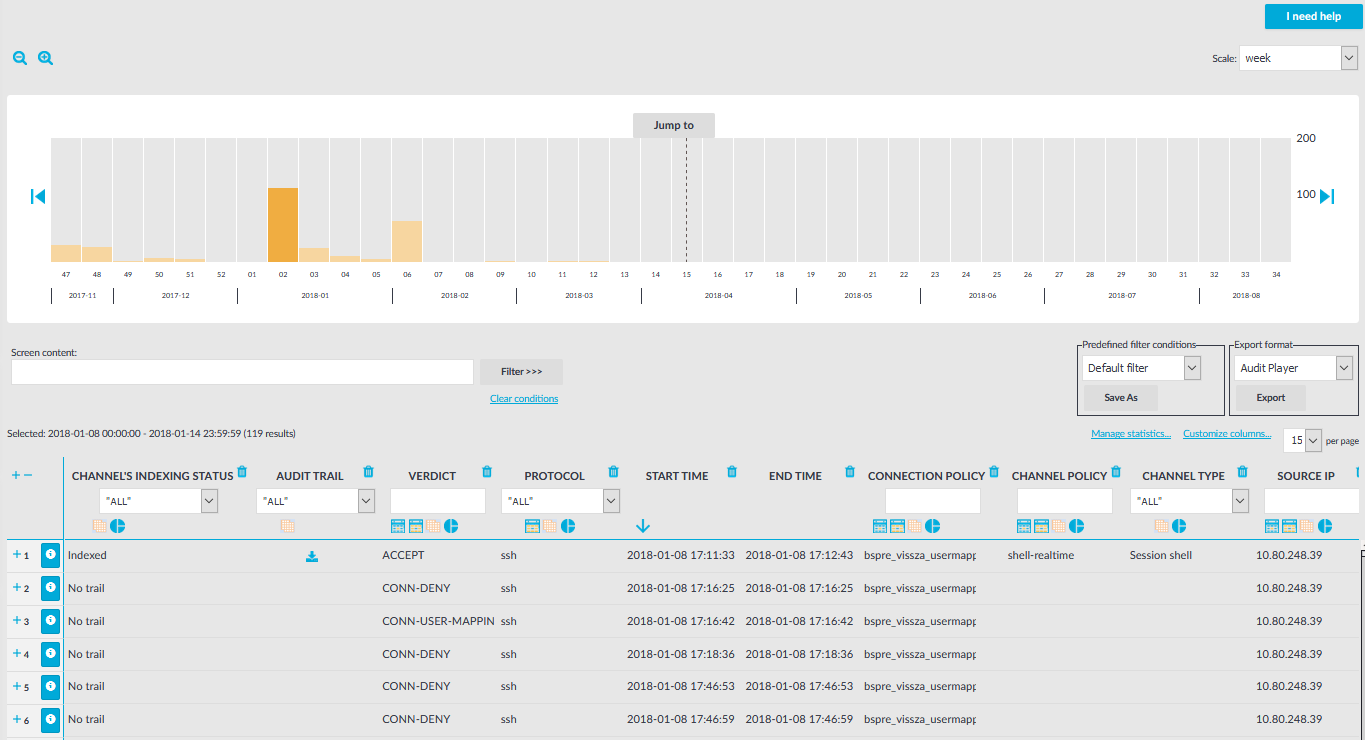
Changing the time interval
The bars display the number of results in the selected interval. Use the 

Hovering the mouse above a bar displays the number of entries and the start and end date of the period that the bar represents. Click a bar to display the entries of that period in the table. Use Shift+Click to select multiple bars.
Searching connections
|
|
NOTE:
This feature is available only if auditing and content indexing was requested for the connection. For details, see Configuring the internal indexer. |
To search in the content of the indexed audit trails, enter your search keywords in the Screen content field, and click Filter. Search is case insensitive. You can use complex expressions and boolean operators. For more information, see Using the content search.
Filtering search results
Connection metadata is displayed in customizable columns that you can filter for any parameter, or a combination of parameters. To filter the list of search results, enter the filter expression in the input field of the appropriate column, and press Enter, or click on an entry in the table.
For the description of the available columns, see Connection metadata.
For information on using and saving filters, see Using and managing search filters.
|
|
NOTE:
When you use filters, the bars display the statistics of the filtered results. |
Filtering displays also partial matches. You can use the 


To restore the original table, click Clear conditions.
|
|
TIP:
Use the drop-down menu of the Protocol column to quickly filter the list for a single protocol. |
Exporting the search results
To export the search results as a comma-separated text file, select Export format > CSV, and click Export.
For instructions on displaying statistics about your search results, see Displaying statistics on search results.
Viewing the details of a connection
To display the summary of a connection, click 

To download the audit trail of a session, click the 

