A Group Membership AutoProvisioning policy performs provisioning tasks such as adding or removing users from groups. A policy can be configured to define a list of groups and conditions so that a user account is automatically added to, or removed from, those groups depending on whether the properties of the user account meet the policy conditions.
Active Roles automatically checks users against conditions, and adds or removes users from specified groups based on the check results. Although the capabilities of this policy are similar to those provided by Dynamic Groups, a Group Membership AutoProvisioning policy gives the administrator extra flexibility and control over group memberships.
Whereas the Dynamic Groups feature delivers a rules-based mechanism for managing a group membership list as a whole, a Group Membership AutoProvisioning policy allows the administrator to define membership rules on a per-user basis. This policy automates the process of adding particular users to particular groups without affecting the other members of those groups.
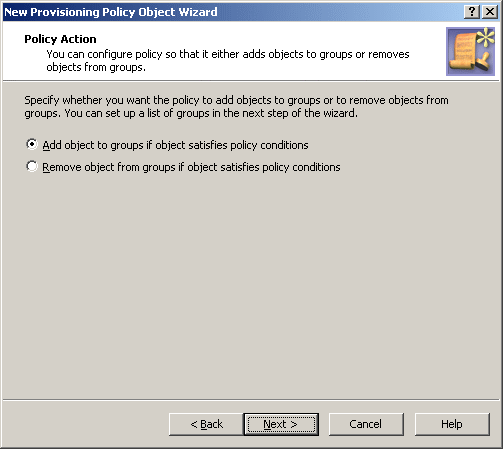
To configure a Group Membership AutoProvisioning policy, select Group Membership AutoProvisioning on the Policy to Configure page in the New Provisioning Policy Object Wizard or in the Add Provisioning Policy Wizard. Then, click Next to display the Object Type Selection page.
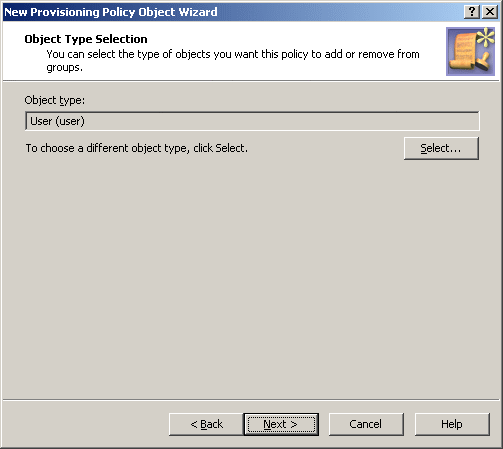
Figure 63: Object type selection
On this page, you can choose the type of objects you want the policy to add or remove from groups. By default, the object type is set to User. If you need to change this setting, click Select to display the Select Object Type dialog.
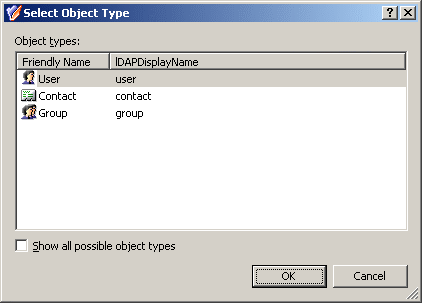
Figure 64: Object types
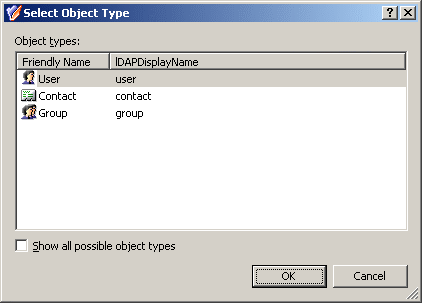
From the Object types list, select the type of objects you want the policy to control. Click OK.
On the Object Type Selection page, click Next to display the Policy Conditions page.
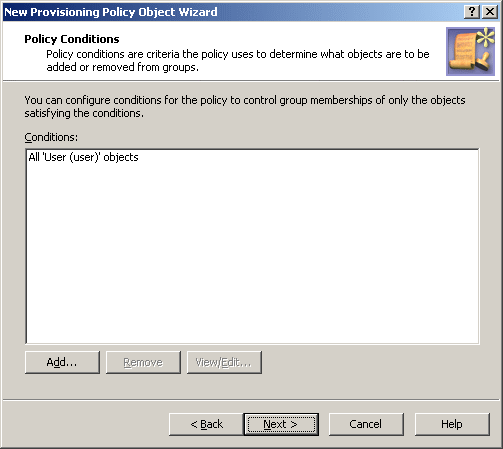
Figure 65: Policy conditions
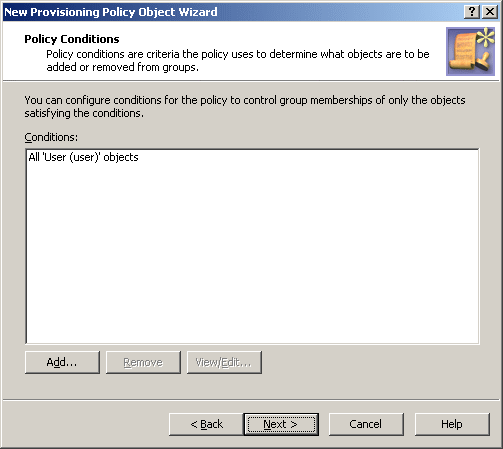
On this page, you can set up policy conditions: criteria the policy uses to determine what objects are to be added or removed from groups. If you specify no conditions, the policy affects any objects of the type you have selected on the previous page. Otherwise, it only affects the objects matching the conditions you specify using this page.
To configure a condition, click Add on the Policy Conditions page. This displays the Set Up Condition dialog.
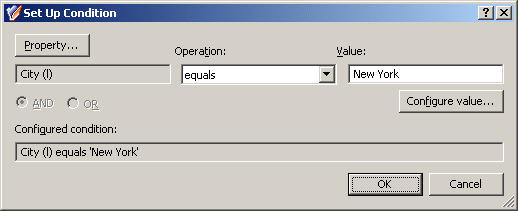
Figure 66: Set up condition
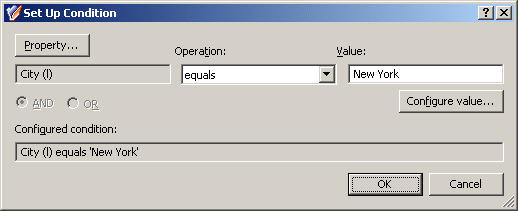
In this dialog, you can configure a condition in the same way as you do for a Property Generation and Validation policy. A condition includes an object property (for example, City or Department), a requirement (for example, equals or begins with), and a value. The term value has the same meaning as for a Property Generation and Validation policy.
First, click the Property button to display the Select Object Property dialog where you can select the object property you want to include in the condition.
Next, from the Operation list, select the requirement you want to apply to the selected property.
Next, click the Configure value button to compose the value for which you want to apply the selected requirement. This displays the Configure Value dialog, discussed in How to configure a Property Generation and Validation policy. You can use that dialog to set up a value in the same way as for a Property Generation and Validation Policy.
If you specify multiple conditions, you can combine them with a logical AND or OR operator by clicking the AND or OR option, respectively.
Finally, click OK to close the Set Up Condition dialog.
After you complete the list on the Policy Conditions page, click Next to display the Policy Action page.
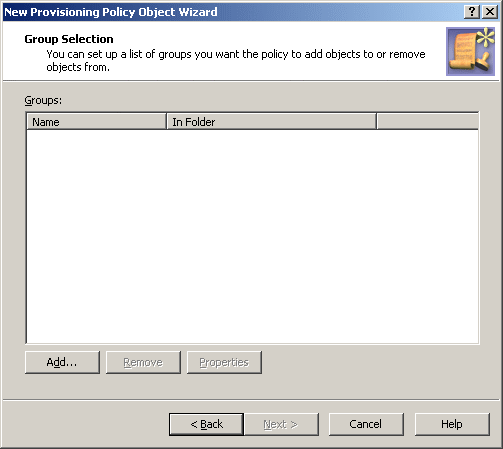
Figure 67: Policy action
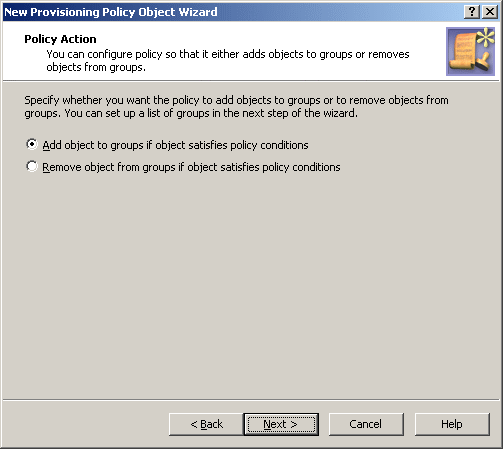
On this page, you can configure the policy to either add objects to groups or remove objects from groups. For example, if you select the option Add object to groups if object satisfies policy conditions, the policy populates groups with the objects that match the conditions you set up in the previous step. Click Next to specify the groups you want the policy to populate. This displays the Group Selection page.
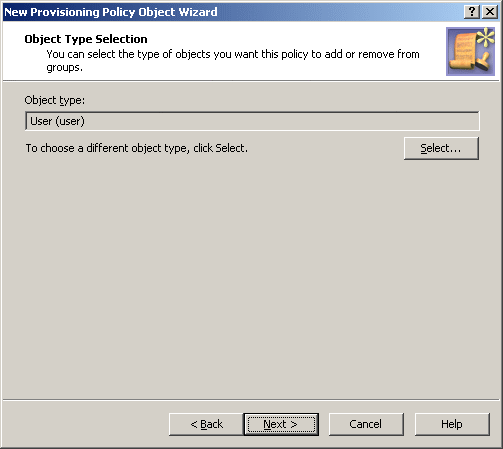
Figure 68: Group selection
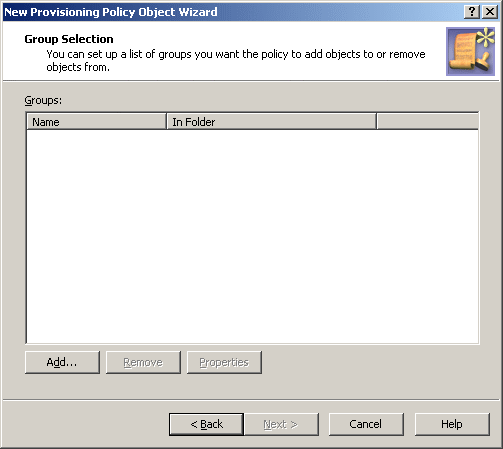
On the Group Selection page, you can set up a list of groups you want the policy to control. Depending on the option you select in the previous step, the policy either adds or removes objects from each of the groups you specify on this page. You can manage the list by using the Add and Remove buttons. Clicking Add displays the Select Objects dialog to select and add groups to the list. Clicking Remove deletes the selected entries from the list.
Once you have set up the list of groups, click Next and follow the instructions in the wizard to create the Policy Object.
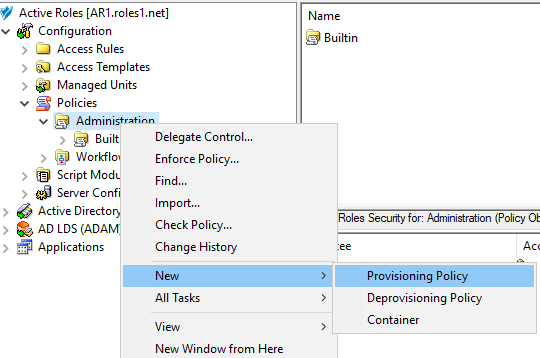
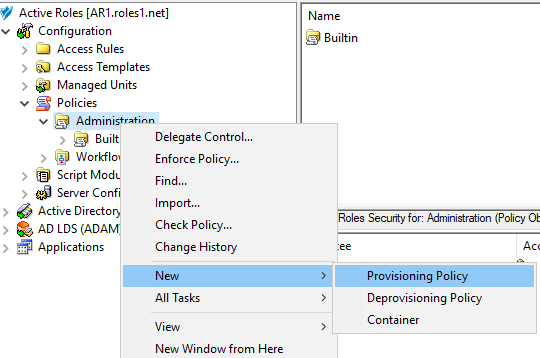
To configure a Group Membership AutoProvisioning policy via the Active Roles Console (also known as the MMC interface), perform the following procedure.
To configure a Group Membership AutoProvisioning policy
-
Navigate to Configuration > Policies > Administration.
-
To open the New Provisioning Policy Object Wizard dialog, right-click in the middle pane to open the context menu, and then select New > Provisioning Policy.
-
On the Name and Description page, provide a unique Name for the new Policy Object. Optionally, also provide a Description. To continue, click Next.
-
On the Policy to Configure page, select Group Membership AutoProvisioning, and then click Next.
-
On the Object Type Selection page, to specify the type of object you want the policy to add or remove from groups, click Select, then click OK.
TIP: If you do not see the object type you need, expand the list by selecting Show all possible object types.
-
On the Policy Conditions page, set up conditions that specify how the policy adds or removes the selected object types to or from groups. To create a new condition with the Set Up Condition dialog, click Add.
-
To select the object property on which you want to set up the condition, click Property to open the Object property page.
-
Select the property you want the condition to check, then click OK.
TIP: If you do not see the object type you need, expand the list by selecting Show all possible object types.
-
In Operation, click the operation type you want to assign to the condition.
-
To specify additional configuration for the condition, enter a variable into the Value field, then click OK to close the Add Value dialog.
Alternatively, click Configure Value, then click Add, and configure an entry manually in the Add Entry dialog. For more information on manual configuration, see Steps for configuring entries. To close the Add Value dialog, click OK.
-
(Optional) To modify or remove an existing condition, click View/Edit or Remove on the Policy Conditions page, respectively.
-
Click Next on the Policy Conditions page to continue onto the Policy Action page.
-
On the Policy Action page, specify whether you want the policy to add or remove objects if the configured conditions are met.
-
Select Add object to groups if object satisfies policy conditions if you want Active Roles to add the object to the specified group(s) if the configured conditions are met.
-
Select Remove object from groups if object satisfies policy conditions if you want Active Roles to remove the object from the specified group(s) if the configured conditions are met.
Click Next to continue.
-
On the Group Selection page, specify the group(s) you want the policy to add the objects to (or remove from, depending on your choice on the Policy Action page). Click Add to open the Select Objects dialog, and then use either the Look in: drop-down or click Browse to specify the group(s). Once you are ready, click Next to continue.
NOTE: Consider the following limitations when configuring a Group Membership Autoprovisioning policy for cloud-only Azure objects:
-
When provisioning cloud-only Azure users or Azure guest users, you must specify an O365 Group (or O365 Groups) in this step. To do so, click Browse to open the Browse for Container dialog, and then navigate to the following node for the list of O365 Groups in the organization:
Azure > <azure-tenant-name> > Office 365 Groups
-
The Group Membership AutoProvisioning policy can only add or remove cloud-only Azure users and guest users to or from O365 Groups that are located in the same Azure tenant as the Azure users and guest users. Selecting O365 Groups located in another Azure tenant causes the configured Policy Object to not work properly.
-
On the Enforce Policy page, specify the objects to which the configured Policy Object will be applied. Click Add, and then use the Select Objects dialog to locate and select the objects.
TIP: When provisioning cloud-only Azure users or guest users, you can either select the respective object category (such as the Azure user or Azure guest user node) in this step, or the Azure tenant that contains the Azure objects.
- Click Next, and then click Finish to create the new policy.
The policy described in this scenario automatically adds user accounts to the specified groups depending on the Department property of user accounts. If the Department property of a user account is set to Sales, the policy adds the account to the Sales group.
To implement this scenario, you must perform the following actions:
-
Create and configure a Policy Object that defines the appropriate policy.
-
Apply the Policy Object to a domain, OU, or Managed Unit.
As a result, when a user account in the container you selected has the Department property set to Sales, Active Roles automatically adds that account in the Sales group.