Implementing a policy to enforce business rules is a two-phase process where configuring the policy within a Policy Object is only the first step. When you create a new policy, you select a policy type from the available options and then define the options that make up the policy. The second step is to use the Active Roles Console to enforce the policy on the desired areas of the directory.
Active Roles allows policies to be enforced on any directory object, that is an administrative view (Managed Unit), a directory folder (container), or an individual (leaf) object. Policies are enforced by applying (linking) a Policy Object that holds the policies.
When you apply a Policy Object to a Managed Unit or directory folder, the policies control the objects in that Unit or folder as well as the Unit or folder itself. When you apply a Policy Object to a leaf object, such as a user or group, the policies only control that object. For example, applying a Policy Object to a group does not affect the members of the group.
The objects that are subject to a given Policy Object, that is, the objects under control of the policies defined in that Policy Object, are collectively referred to as policy scope. For example, if you apply a Policy Object to a Managed Unit, the policy scope is composed of the objects within the Managed Unit.
Thus, the policy scope normally includes all objects that reside in a container or Managed Unit to which the Policy Object is applied. However, sometimes you may need to exclude individual objects or sub-containers from the policy scope, thereby preventing certain objects from being affected by policies.
Active Roles gives you the option to selectively exclude objects or entire containers from the policy scope. You can block policy inheritance on individual objects or containers, refining the policy scope. For more information on how to block policy inheritance, see Managing policy scope.
To apply a Policy Object, you can start from any of the following points:
You can add administrative views (Managed Units) and directory folders (containers) to the policy scope of a given Policy Object in one of following ways:
-
Right-click the Policy Object and click Policy Scope. Then, in the Active Roles Policy Scope window, click Add.
-
Ensure that Advanced Details Pane is checked on the View menu. Then, select the Policy Object. On the Active Roles Policy Scope tab in the details pane, right-click a blank area and click Add.
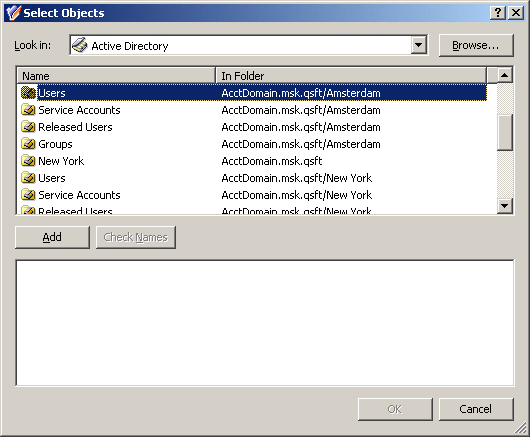
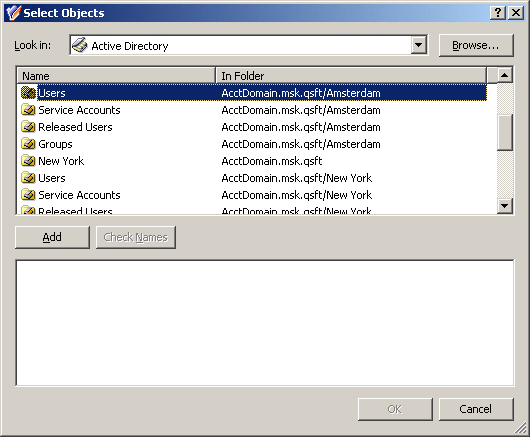
In both cases, clicking Add displays the Select Objects window where you can select containers and Managed Units. To build a list of containers from which to select, click Browse and select Active Directory or a container in the hierarchy under Active Directory.
Figure 40: Policy Objects
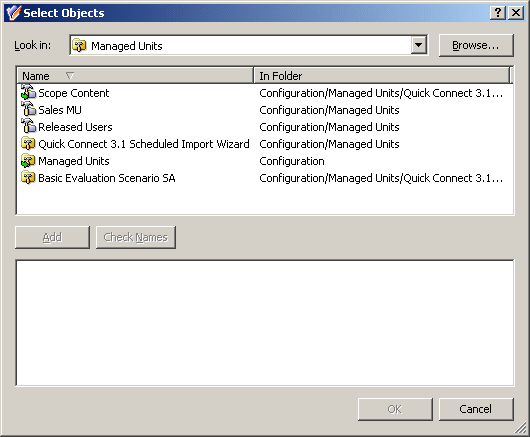
To build a list of Managed Units, click Browse and select Managed Units or a container in the hierarchy under Managed Units.
Figure 41: Managed Units
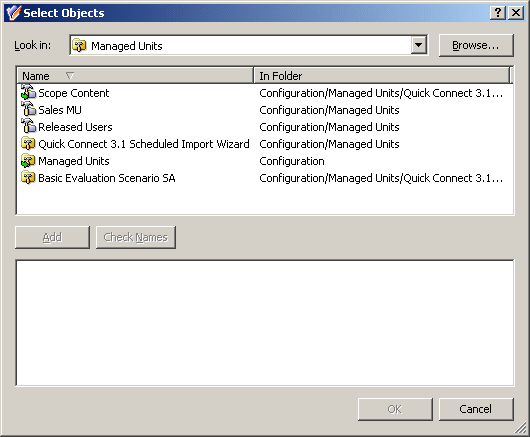
In the Select Objects window, select containers or Managed Units from the list and click Add to build the resultant list of items. When finished, click OK.
For a given directory object (container, user, group, and so on), a list of Policy Objects that affect the directory object is referred to as policy list. If the directory object is in the policy scope of a given Policy Object, the Policy Object is included in the policy list for that directory object.
The steps to add a Policy Object to the policy list for a directory object depend on whether it is a container or leaf object:
-
Right-click a Managed Unit or container and click Enforce Policy. Then, in the Active Roles Policy window, click Add.
-
Right-click a leaf object (user, group, or the like), click Properties, go to the Administration tab, and click Policy. Then, in the Active Roles Policy window, click Add.
If you use the advanced details pane (Advanced Details Pane is checked on the View menu), you can do this as follows, regardless of the type of the directory object:
-
Select the directory object, go to the Active Roles Policy tab in the details pane, right-click a blank area on the tab, and then click Add.
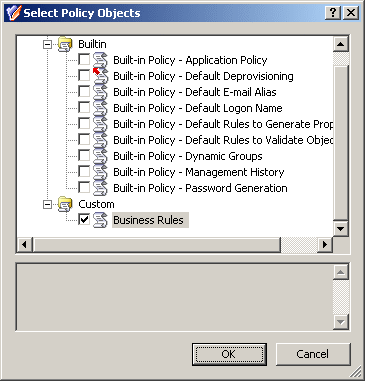
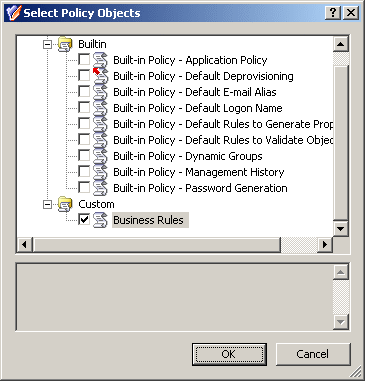
In all these cases, clicking Add displays the Select Policy Objects window where you can select Policy Objects to add. Select the Policy Objects, then click OK.
Figure 42: Policy Objects
To apply a Policy Object
-
In the Console tree, under Configuration > Policies > Administration, locate and select the folder that contains the Policy Object you want to apply.
-
In the details pane, right-click the Policy Object, and then click Policy Scope.
-
In the Active Roles Policy Scope dialog, click Add.
-
Use the Select Objects dialog to locate and select the container, Managed Unit, or a leaf object on which you want to specify policy settings by using the Policy Object.
-
Click OK to close the Active Roles Policy Scope dialog.
To specify policy settings on an object by using a Policy Object
-
Open the Active Roles Policy dialog for the object in one of the following ways:
-
Right-click the object, and click Enforce Policy.
-
Right-click the object, and click Properties. Then, on the Administration tab in the Properties dialog, click Policy.
-
In the Active Roles Policy dialog, click Add.
-
Use the Select Policy Objects dialog to locate and select the Policy Object to apply.
-
To select a Policy Object, click the check box next to the name of the Policy Object. You can select multiple Policy Objects.
-
Click OK to close the Active Roles Policy dialog.
TIP: To apply a Policy Object, you can also use the Active Roles Policy Scope or Active Roles Policy tab in the advanced details pane: Right-click a blank area on the tab, and then click Add. To display the advanced details pane, check Advanced Details Pane on the View menu. For more information, see Advanced pane.
To view or modify inheritance options for a Policy Object on a container or Managed Unit
-
Open the Active Roles Policy Scope dialog for the Policy Object: Right-click the Policy Object, and then click Policy Scope.
-
In the Active Roles Policy Scope dialog, select the container or Managed Unit to which the Policy Object is applied and on which you want to examine inheritance options, and then click View/Edit.
-
On the General tab, view or modify the selection of these options, which specifies the scope where the Policy Object determines policy settings:
-
This directory object: The scope includes the container or Managed Unit you have selected (this option does not cause the scope to include any child objects or members of the container or Managed Unit).
-
Child objects of this directory object: The scope includes all the child objects (or members, as applied to a Managed Unit) in the entire hierarchy under the container or Managed Unit you have selected.
-
Immediate child objects only: The scope includes only the child objects (or members, as applied to a Managed Unit) of which the container or Managed Unit that you have selected is the direct ancestor.