One Identity Safeguard for Privileged Sessions (SPS) version 3.2 and later provides an interface to query the user-rights and privileges of individual users and user groups. To display the privileges of a user or usergroup, navigate to Users & Access Control > Access Rights Report, enter the name of the user or group into the respective field, then click Filter. Note that:
-
It is not possible to filter on both the username and the group at the same time.
-
Partial matches are also displayed.
-
Usergroups can be local usergroups, userlists, or LDAP usergroups.
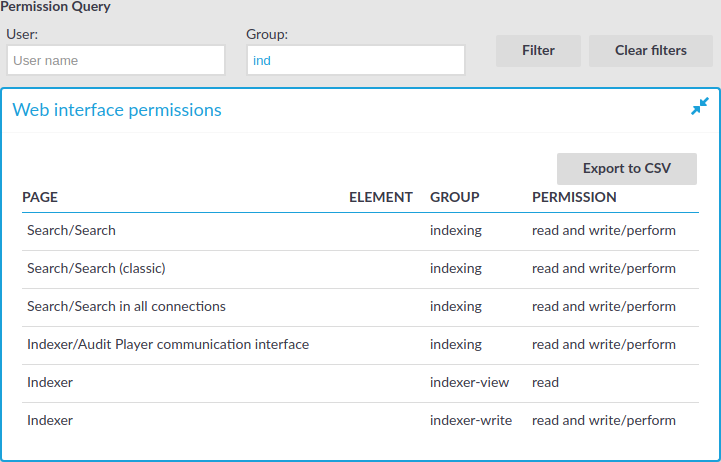
Web interface permissions
For usergroups accessing the SPS web interface, a table is displayed that lists the pages of the SPS web interface that the user or usergroup can access. The following information is displayed:
-
Page: The name of the page or group of pages, for example, Basic Settings.
-
Element: If a group has access only to a section of a page, the name of the element is listed here. For example, a particular Channel Policy.
-
Group: The name of the usergroup.
-
Permission: The type of access that the user or usergroup has to the page: read or read and write/perform.
Figure 100: Users & Access Control > Access Rights Report — Displaying web interface permissions
Connection permissions
To review which servers a user or usergroup can access, SPS collects the main information about the connections the user or group is permitted to use. The following information is displayed.
To display the usergroups that can access a specific Connection Policy, open the Connection Policy, then on the Connections page, select Show connection permissions > Show.
Figure 101: Users & Access Control > Connection permissions — Displaying connection permissions
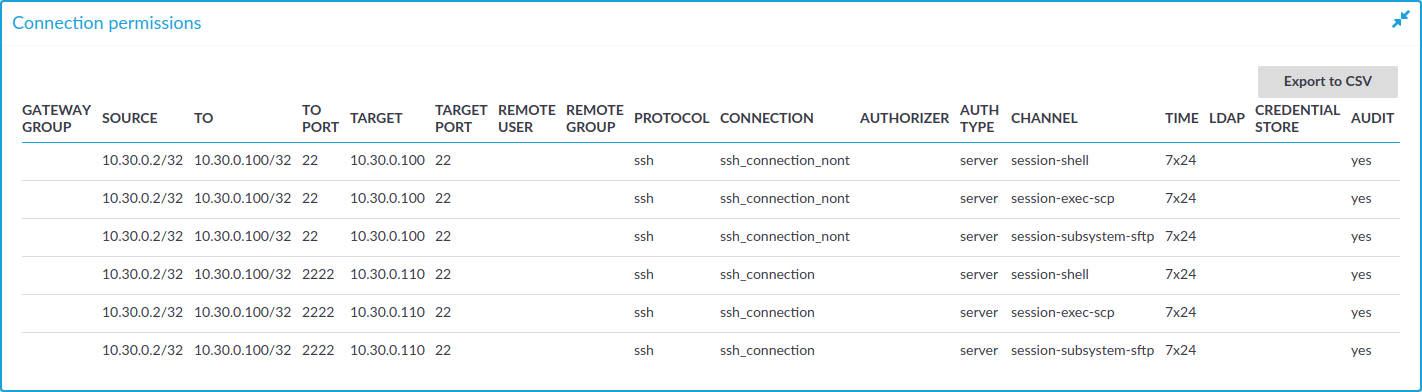
-
Gateway group: Lists the group memberships required to access the connection. Group memberships can be restricted at the following places:
-
Connection > Gateway authentication > Groups
-
Channel Policies > Gateway group
-
Policies > Usermapping Policies > Groups
-
-
Source: Refers to the following field from the session database:
Source IP: The IP address of the client.
-
To: Refers to the following field from the session database:
Destination IP: The IP address of the server as requested by the client.
-
To port: Refers to the following field from the session database:
Destination port: The port number of the server as requested by the client.
-
Target: Refers to the following field from the session database:
Server IP: The IP address of the server connected by SPS.
-
Target port: Refers to the following field from the session database:
Server port: The port number of the server connected by SPS.
-
Remote user: Refers to the following field from the session database:
Username on server: The username used to log in to the remote server. This username can differ from the client-side username if usermapping is used in the connection. For details on usermapping, see Configuring usermapping policies.
-
Remote group: The group that can access the destination server, as set in the Usermapping Policy (if any).
-
Protocol: The protocol used in the connection (Citrix ICA, HTTP, RDP, SSH, Telnet, or VNC).
-
Connection: Refers to the following field from the session database:
Connection policy ID: The identifier of the connection policy.
-
Authorizer: Refers to the following field from the session database:
Four-eyes authorizer: The username of the user who authorized the session. Available only if 4-eyes authorization is required for the channel. For details on 4-eyes authorization, see Configuring four-eyes authorization.
-
Auth type: The authentication method used in the client-side connection during gateway authentication.
-
Channel: The type of the channel, for example, session-shell.
-
Time: The name of the Time Policy used in the connection.
-
LDAP: The name of the LDAP Server used in the connection (if any).
-
Credential store: The name of the Credential Store used in the connection (if any).
-
Audit: Indicates if the connection is recorded into audit trails.
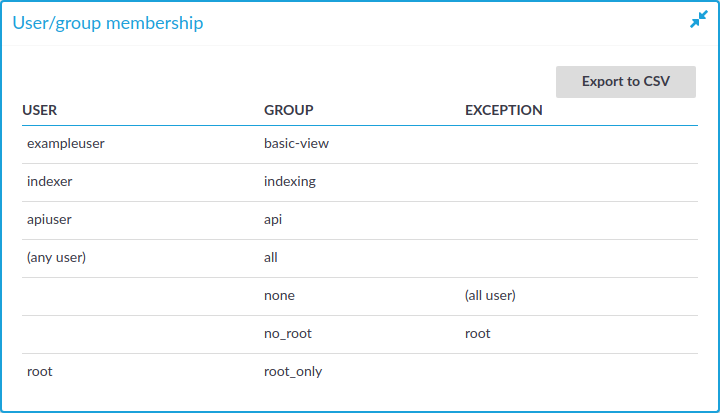
Usergroup memberships
When searching for users, the table displays the group memberships of the matching users. When searching for usergroups, the table displays the members of the matching groups. The following information is displayed:
-
User: The username of the user.
-
Group: The name of the usergroup or userlist.
-
Exception: Usernames that are denied in case of default-deny userlists managed locally on SPS.
Figure 102: Users & Access Control > Connection permissions — Displaying usergroup and userlist memberships

 and
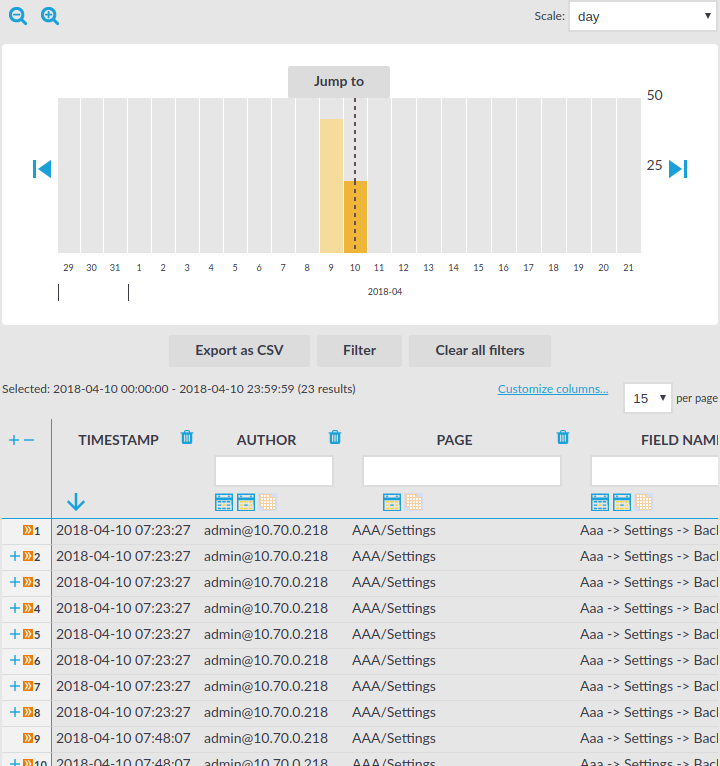
and  icons to zoom, and the arrows to display the previous or the next intervals. To explicitly select a date, select Jump to and set the date in the calendar. You can change the length of the displayed interval with the Scale option.
icons to zoom, and the arrows to display the previous or the next intervals. To explicitly select a date, select Jump to and set the date in the calendar. You can change the length of the displayed interval with the Scale option. . To shrink the row back to its original size, click
. To shrink the row back to its original size, click  . To expand/shrink all rows, click the respective button on the header of the table. The rows can also be expanded/shrunk by double clicking on the respective row.
. To expand/shrink all rows, click the respective button on the header of the table. The rows can also be expanded/shrunk by double clicking on the respective row. icon to perform an exact search, and the
icon to perform an exact search, and the  icon for inverse filtering ("does not include"). To clear filters from a column, click
icon for inverse filtering ("does not include"). To clear filters from a column, click  .
.